Read this review and comparison of the top Sophos Device Control Alternatives with features, ratings, and pricing to select the best Sophos Device Control Competitor:
Sophos is widely regarded as a premier device control solution. Its proficiency in managing the use of peripheral devices and preventing unauthorized access to sensitive data through clear device control policies is excellent.
This software prevents data leakage and enables the monitoring and control of data transfers between endpoints and peripheral devices. In addition, you can customize the policies defined by the software as per your requirement. The software is truly exceptional at simplifying deployments and reducing administrative overhead.
That said, the tool isn’t without its flaws. For starters, configuring policies for different user roles on the platform can be time-consuming. Some users have also reported the tool, generating too many false positives.
Table of Contents:
Sophos Device Control Alternatives – Top Selected

Understandably, the tool may not be a perfect fit for everyone. Fortunately, Sophos isn’t the only platform out there with device control capabilities.

[image source]
In this article, I will recommend such tools that feature robust device control capabilities. In my personal experience, these tools can easily go toe-to-toe with some of the best features that Sophos provides.
So, without much further ado, let’s get started.
Who is This Article For?
Companies across the industrial spectrum can benefit immensely from a tool that offers device control capabilities. The tools I am about to recommend are solutions that can cater to the needs of both start-ups and large enterprises.
From healthcare and education to legal services and the government sector, almost as many companies will need a device control solution.
Besides companies, the following professionals in an organization can breathe a sigh of relief with a device control solution by their side:
- Security Teams
- Help Desk and Support Team
- IT Administrators
- Data Privacy Officers
- Compliance Officers
- End Users
Select the Best Sophos Alternative: Factors
Consider the following essential parameters to ensure you’re selecting the right tool for your need:
#1) Ease of Use: With device control solutions, a lot of action lies within the management console that you’ll be using to define policies and configure settings. So it is important to only go for tools that feature a UI that’s both intuitive and user-friendly. It should be easy to navigate with features easily accessible to the administrator.
#2) Features: Features are the backbone of any software and device control solutions aren’t an exception to this rule. So pay special attention to the features being offered to you.
Look for a Device Control solution that offers multi-OS support, offer a broad scope of control (including not just USB control, but also Bluetooth devices, printers, etc.), granular visibility, real-time monitoring, and customizable reporting capabilities.
#3) Your Industry: Different companies have different requirements. These requirements can be determined clearly based on the industry your company belongs to.
For instance, a healthcare company will need its device control solution to comply with regulatory frameworks like HIPAA. So make sure the tool you choose can meet your industry’s specific requirements.
#4) Scalability: Whatever tool you choose, make sure it scales on demand. You want the tool to meet the needs of a growing organization. Preferably go for tools that have no qualms managing large-scale environments.
#5) Integration: Optimal security entails 24/7 threat detection, appropriate response deployment, and prevention of unauthorized access. This is only achievable with a unified approach to security. So you’d want a tool that can integrate seamlessly with other security solutions like SIEMs, Anti-virus tools, and Endpoint Protection Platforms.
Suggested Read =>> EDR Security Service provider companies
#6) Vendor Reputation: Make sure the vendor selling you the tool enjoys a spotless reputation in the industry. You can easily find out if this is the case by referring to a few Google reviews and going through testimonials left behind by past clients.
#7) Price: Do not compromise on quality for a cheaper tool. Most device control solutions offer customized pricing plans to their clients, anyway. Be sure you know what your requirements are and get a clear quote from the vendor. Also, make sure there aren’t any hidden charges. You want your vendor to be fully transparent with you regarding the price.

Expert Advice:
- Foremost, know what your company requires. Go for a tool that can meet those requirements without compromise.
- Make a shortlist of all the tools you like and compare them against each other based on the functionality, usability, features, and price they offer.
- The software should offer advanced automation capabilities.
- Granular control and visibility over devices on a network are non-negotiable.
- The interface should be easy to use, even for non-technical users.
- The price should be reasonable and fit within your budget.
List of the Best Sophos Device Control Alternatives
Below are the workable alternatives to Sophos:
- Netwrix Endpoint Protector
- NinjaOne Endpoint Management
- ManageEngine Device Control Plus
- Bitdefender
- Ivanti
- CrowdStrike
- SentinelOne
Comparing Some of the Top Sophos Competitors
| Name | Best for | Deployment | Key Features |
|---|---|---|---|
| Netwrix Endpoint Protector | Policy customization and granular control | On-Premise Cloud-hosted, Mac, Windows, Linux | File encrypting, content-aware data scanning, granular control policy, multi-OS |
| NinjaOne Endpoint Management | Real-time monitoring and intuitive interface | iOS, Android, Web | Patch Management, Auto Remediation, Real-Time Monitoring |
| ManageEngine Device Control Plus | Protecting data from removable devices. | On-premise, Web-based, Windows | Device and port control, file access control, file shadowing, and file tracing. |
| Bitdefender | Granular Control and Visibility | Mac, Windows, Cloud-hosted, Android, iPhone | Real-time monitoring, granular policy control, and content-aware protection. |
| Ivanti | Comprehensive DLP Capabilities | Web-based, Windows | Application control, content-aware control, granular device control |
| CrowdStrike | Integration with endpoint protection platform | Cloud-hosted, iPhone, Android | Automatic visibility, pre-built dashboard, granular policy control |
| SentinelOne | AI-powered security | Mac, Windows, Cloud-hosted | Single-agent architecture, EPP integration, automated threat response |
Top Sophos Alternatives:
#1) Netwrix Endpoint Protector
Best for policy customization and granular control.

Netwrix Endpoint Protector DLP provides a sophisticated device control solution, allowing you to manage removable storage devices and peripheral ports across macOS, Windows, and Linux systems.
The solution can control over 40 different device classes, including USB removable storage, printers, SD-cards, smartphones, and many others. Comprehensive coverage is guaranteed through a diverse range of options, leading to a secure and controlled IT environment.
Functionality: The first thing you’ll notice when you launch Netwrix Endpoint Protector is the broad range of DLP capabilities it features. Besides device control, you can also use the software for file encryption and content-aware data scanning.
The solution simplifies device control by making it easy to define and configure policies that apply to any device accessing your network. The software was designed for large-scale environments. You’ll have no issue integrating the software with your company’s existing security infrastructure.
Usability: Netwrix Endpoint Protector features a user-friendly interface that is very easy to navigate. The features are easily accessible, thus making the tool ideal for both new and experienced administrators. It comes with a great visual dashboard that presents you with actionable insight.
You get better visibility and granular control over all devices on your network through this dashboard. You’ll be able to define policies, configure and apply them to different users or teams, and access key information about your system’s status via this dashboard in a matter of minutes.
How to Use Netwrix Endpoint Protector for Device Control:
- Launch the Netwrix Endpoint Protector’s server management console on your browser.
- Once done, define policies and configure settings for device control.
- You can determine what device to authorize and what devices to block with the help of these policies.
- We can customize further the policies, depending on the needs of your user groups and department requirements.
- Deploy the policy to the endpoint and the tool will enforce it.
- Access Endpoint Protector’s real-time reports to know how your policies are performing.
Here is a video on how Device Control works:
Features:
- Granular Control Enforcement: The software allows administrators to define policies across over 40 different device classes (from USB drives to printers). Controls are highly detailed and customizable.
- Data Monitoring: The software provides you with real-time insight into data usage, system vulnerabilities, policy violations, etc. You can rely on detailed logs and real-time alerts that respond appropriately to these issues.
- Offline Protection: The software is deployed locally on the endpoint, so will continue to maintain policy protection, even if the endpoint is taken offline.
- Data Compliance: The software enables your organization to protect sensitive data and achieve regulatory compliance with NIST, HIPAA, PCI-DSS, GDPR, GLBA, and others, avoiding fines and other damages imposed by regulatory entities.
- Content-Aware Data Scanning: The software’s device control capabilities can be enhanced with content-aware scanning, allowing even greater controls. For example, only blocking the transfer of a file to a removable storage device if it contains confidential data.
- File Encryption: If you do need to allow users to use removable storage devices, the software offers an additional encryption feature to automatically encrypt data being transferred. The software can also remotely lock a removable USB storage device if it gets lost or stolen, adding to your security.
Why do I think Netwrix Endpoint Protector is the Best Sophos Device Control Alternative?
Netwrix Endpoint Protector is considerably better than Sophos when it comes to policy customization. Defining device control policies is very simple with Endpoint Protector. Plus, the broad range of data loss protection capabilities, and breadth of devices that can be managed, really helps as well.
Pros:
- The tool comes with a user-friendly interface that’s easy to navigate. Its UI is further bolstered by an excellent visual dashboard that can be used for defining policies as well as referring to reports.
- It has the widest list of controllable devices, everything from USB storage drives and printers to SD-Cards, smartphones, and Bluetooth connections.
- The software offers zero-day support for both macOS and Windows systems. This is software that works well with even the latest versions of your OS.
- The software is adequately scalable and can meet the requirements of a growing business. It is best suited for large-scale environments.
Cons:
- Nothing significant
Our Review: Multi-OS support, a user-friendly interface, easy policy customization, and granular control are just some features that make Endpoint Protector one of the best alternatives for Sophos. It is very easy to use and deploy.
Plus, you get robust threat protection capabilities to keep both your system and the data within it secure around the clock. Endpoint Protector is definitely among the best Sophos Device Control competitors and alternatives.
Price: The official website of Netwrix does not disclose its pricing. You’ll need to contact the team and convey your requirements. Based on those requirements, they’ll offer you a quote. You can also request a free demo.
#2) NinjaOne Endpoint Management
Best for Real-time monitoring and intuitive interface.
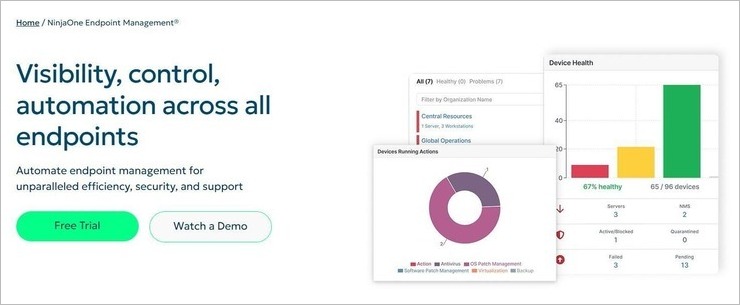
NinjaOne Endpoint Management has a lot to offer, enough to make it seem a better alternative to Sophos. First and foremost, it is a tool that boasts impressive automation capabilities. You can count on it to automate the most time-consuming endpoint management tasks. Add to that, it arms IT technicians with the tools necessary for improved IT efficiency.
Functionality: Once deployed, NinjaOne grants you better visibility and control of your entire IT estate. You can use it to monitor and control all Windows, Mac, and Linux end-user devices as well as networking devices. Like I mentioned before, automation is what gives this tool an edge over so many of its contemporaries in the market.
Through simple automation mechanisms and form-based deployment, the tool can help you automate almost all time-consuming endpoint management tasks. You are also provided with real-time device telemetry, which makes you privy to insight into the health and performance of devices across endpoints.
Usability: NinjaOne is known for its user-friendly, lightning-fast UI. Managing and monitoring endpoints is easier as you are provided with a unified console. You can also deploy it very fast. You can have the software up and running within a month or just a few days.
How to Get Started with NinjaOne Endpoint Management
- Start by creating an organization template with accurate configurations.
- Import more organizations via CSV. Skip if you have a single organization.
- Generate NinjaOne installer. You can do so manually via the interface or programmatically through the NinjaOne API.
- Proceed to install the NinjaOne Agent. The agent can be deployed in any of the following ways:
- Deploy via existing RMM or endpoint management solution.
- Send MSI links to end users
- Deploy via Azure / Intune.
- Manually install the agent in person or via remote access
- Use NinjaOne’s native Active Directory Discovery and Deployment.
Features:
- Patch Management: The software automates patching for Windows, macOS, and Linux systems. It can also automate patching for over 200 applications. You can get a full picture of your patching stance via the centralized dashboard.
- Task Automation: Even the most time-consuming tasks can be automated through NinjaOne. The automation takes the burden off technicians and ensures better device stability.
- Auto-Remediation: The detection and remediation of endpoint issues is fully automated with the help of condition-based script deployment. From stopped services to missed reboots, the software will automate remediations for all such issues.
- Inventorying: You are provided with complete, up-to-date information on all devices within your IT estate. This includes both hardware and software information.
- Real-time Monitoring: This is one of NinjaOne’s most appealing features. It can help you monitor all devices across endpoints in real-time. Technicians are automatically notified if a threat or vulnerability is detected.
Why I Like It?
Firstly, I like how quick it is to deploy this software. Secondly, its automation capabilities are second to none. You are guaranteed better visibility and control across endpoints with this tool.
Pros:
- Easy-to-use interface with a centralized dashboard.
- Flexible pricing
- Integrations with many third-party tools
- Flexible reports and real-time monitoring.
Cons:
- Some advanced features might require a learning curve.
Verdict: NinjaOne Endpoint Management offers everything you’d want from a tool that promises to automate and simplify IT operations. From real-time monitoring of devices to automated patching, you can count on this tool to free up your technicians, stabilize your devices, and standardize outcomes.
Price: NinjaOne Endpoint Management offers flexible monthly and annual contracts. You’ll need to contact NinjaOne’s team for a custom quote. A free demo and trial is also available upon request.
#3) ManageEngine Device Control Plus
Best for protecting data from removable devices.
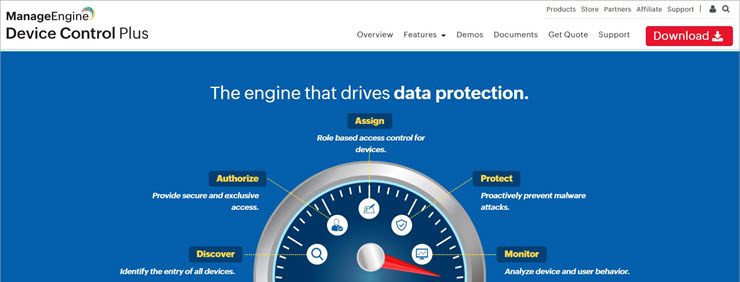
ManageEngine’s Device Control Plus has a lot to offer to enterprises who wish to safeguard their data from all sorts of threats, especially those that come through removable devices. This is software you can use to control, block, and manage all sorts of peripheral devices.
Functionality: Device Control Plus lets you easily set up a variety of policies designed to secure a system’s endpoints. You can set up exclusive access privileges to safeguard data. You can set up a policy that allows read-only access, thus blocking any other action. You can set up caps that limit the type of file or the size of files that can be transferred.
Once this policy is implemented, you can sit back and let Device Control Plus take the steering wheel. It will automatically prevent the transfer of files based on the restrictions you’ve put in place. Device Control Plus is also miles ahead of your average cyber-security tool as it takes a zero-trust approach to threat detection.
You can count on the tool to create a trusted device list. This ensures that any unauthorized device never has a chance of connecting with your systems.
Usability: Device Control Plus is very simple to use. This is in large part because of its expertly curated interface, which is easy to navigate. Everything crucial is easily visible and accessible with a few clicks. You can configure device control policies on a granular level.
You also get audit data and reports that are easy to comprehend. You are instantly alerted every time there is unauthorized access by any device.
How it works?
Device Control Plus lets you set up policies that control and restrict the access certain removable devices have. Here’s an example of how Device Control Plus can block a device.
- Launch the software and navigate to “Policies”
- Under “Policies” click on “Create Policy”
- Against the “Removable Storage Devices”, select “Block”
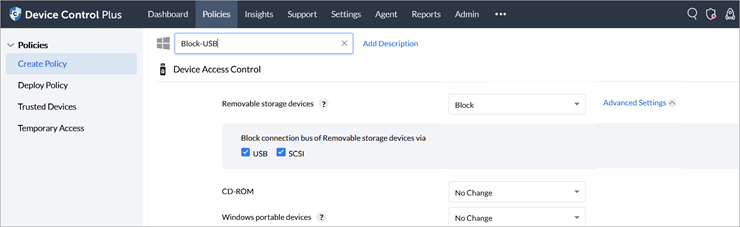
- Based on your preference, you can choose to block the connection bus of removable devices via USB or SCSI.
- Select “Save and Publish” to enforce this policy.
Features:
- Device Control: The software will help you control all devices and ports. You will be able to block any device you wish. You’ll also get to monitor all device actions from a single place.
- File Access Control: You can set role-based access control. The tool also helps you set up read-only permissions. This way you can block data from being copied out of your devices.
- File Transfer Control: You can set up a cap on the size of data that can be transferred. You can limit file transfer activity by setting up the maximum size of file transfer and file type.
- Trusted Device List: Easily set up a list of devices that you trust. The tool will take this list as a reference when providing access to devices. All unauthorized devices will be blocked automatically.
Why I like this software?
Device Control Plus is very simple to use. You can easily navigate through its interface, set up a control policy, and publish it in just a couple of simple steps. The data reports it presents to you are also another one of its highlights.
Pros:
- User-friendly UI
- Granular-level policy configuration
- Real-time monitoring
- Comprehensive data reporting
Cons:
- Can be expensive.
Verdict: With Device Control Plus, you get a solution that goes above and beyond to ensure your data remains safe from unauthorized USB or removable devices. This is an excellent software that’s ideal for stopping insider attacks, preventing data theft, and managing the transfer of files to and from your system.
Price: Device Control Plus starts at $595 per annum. You can also request a custom quote based on your specific requirements. A free demo and trial are also available.
#4) Bitdefender Device Control
Best for Granular Control and Visibility.

Bitdefender is the final tool on my list that I truly believe can go toe-to-toe with Sophos, especially when you consider device control.
Functionality: Bitdefender offers a device control module that’s designed to prevent malware infestation and data leakage. It does so allowing you to define granular control policies that let you determine how a particular external device or peripheral port should be treated on your device.
You can easily configure device permissions for USB devices, printers, and other peripherals. You can clearly define specific rules like establishing read-only access, whitelisting authorized devices, or blocking unauthorized devices. Also, you can implement content-aware policies to prevent unauthorized data transfers.
Usability: Bitdefender’s core management console features a layout that’s easy to get a handle over. You can use the management console to monitor device activity and events in real time. Besides this, you can set alerts and notifications for security events. You can also refer to the console to review activity logs or get detailed audit trails.
How to Use Bitdefender for Device Control:
- Install the Bitdefender Device Control Module on the endpoint.
- Log into your Bitdefender Device Control management console using the provided credentials.
- Start defining security policies based on compliance and organization requirements.
- Configure device access permission for external storage devices and other peripherals.
- Configure actions for alerts and email notifications.
- Deploy the policies and monitor their performance on the management console dashboard.
Here is the video tutorial:
Features:
- Content-Aware Data Protection: The software allows you to define policies based on keywords, file types, and regular expressions. This mitigates the risk of data breaches and protects sensitive information.
- Granular Device Control: Define policies that will dictate access permissions for USBs, printers, and other peripheral devices. Define what device to whitelist and what devices to block.
- Integration with EPP: The software integrates with Bitdefender’s broader endpoint protection platform seamlessly. As such, you get a single console for device control and advanced threat detection and response.
- Real-time Monitoring: The software offers comprehensive auditing and reporting features. The software can produce real-time alerts for policy violations and unauthorized device access.
Why I Like It: I found Bitdefender quite effective in proactively managing and securing peripheral devices. It can help your organization maintain regulatory compliance while protecting sensitive data. It seamlessly integrates with Bitdefender’s endpoint protection platform and excels with its granular device control capabilities.
Pros:
- The process of defining specific access permission and rules. It is quite effective in preventing data exfiltration and unauthorized access.
- The software offers greater visibility into device usage across the organization. You get real-time alerts and notifications for security issues.
- The software can generate reports that assist with auditing and compliance with certain regulatory frameworks, like GDPR and HIPAA.
Cons:
- Although easy to use, the initial configuration demands a certain level of technical expertise from its users. As such, the software may not be ideal for less-experienced IT staff.
Verdict: Bitdefender shines because of two key factors. Its granular device control capabilities and real-time monitoring features are outstanding. Add to that, you get an intuitive interface to play with. This is definitely great software for data protection and device control.
If is definitely one of the better Sophos UTM alternatives and competitors out there.
Price: The software is available in two forms. One is suitable for home use while the other is ideal for business use. Choose the one you need based on your requirements and contact the Bitdefender team to discuss the pricing.
#5) Ivanti
Best for comprehensive DLP Capabilities.

Like Endpoint Protector and Sophos, Ivanti too is a popular endpoint security solution. The software arms IT administrators and security teams with the tools they need to manage and secure their endpoints.
Functionality: Ivanti boasts comprehensive device control capabilities. Once launched, you can rely on Ivanti to define granular policies. These policies can grant you better visibility and control over all devices currently present on your network.
The rules can be defined based on user groups, device types, and time of day. Besides device control, the software comes jam-packed with robust data loss prevention features to prevent data leakage and unauthorized access. You can use the software to restrict access to applications running on your network as well, thus ensuring optimal security.
Usability: Ivanti’s UI makes it very easy for administrators to manage and enforce device control policies. You get a visual dashboard that’s easy to navigate. This dashboard gives you a clear overview of your endpoint’s security status.
You can rely on this dashboard to monitor and control access to various peripherals, device ports, and storage media on your network.
How to Use Ivanti for Device Control:
- Install the Ivanti Device Control agent on the endpoints you wish to protect.
- Open the Ivanti Device Control management console.
- Define security policies as regulatory standards and organization’s requirements.
- Set device permissions. For instance, specify whether to authorize, restrict, or block external storage devices, USB ports, and other peripherals.
- Configure alerts and notifications for unauthorized device access or data transfer attempts.
- Define appropriate response actions if the above events transpire.
- Save and deploy the policies to endpoints.
Here is a video tutorial on how to install Ivanti Device Control:
Features:
- Granular Device Control: Like the best device control solutions out there, Ivanti too lets you get granular control over all endpoints on your network. You can easily enforce granular control policies to restrict the use of removable storage devices, printers, Bluetooth devices, and other peripherals.
- Content–Aware Control: The software allows users to define policies based on keywords, file types, and regular expressions. This proves helpful in securing confidential data like financial records, IP, PII, etc.
- Application Control: The software facilitates application whitelisting and blacklisting. This way, administrators can identify what applications we can trust and block those that are proven to be malicious.
- Auditing and Compliance: Users get auditing and reporting features that are essential to ensuring compliance with regulatory bodies. It offers detailed logs and can also monitor device activity in real time.
- Strong Integration: The software offers integration with other security solutions. It can integrate seamlessly with existing SIEMs, EPPs, and other security solutions to strengthen the overall security posture of an organization.
Why I Like It: I really like Sophos because of how easy it is to define granular device control policies using this tool. It also works great as a data loss prevention and EDR tool. The software’s also highly scalable and integrates seamlessly with most security solutions I am aware of.
Pros:
- The software’s designed to scale and cater to the needs of a growing business. The software’s ideal for both small and large-scale enterprises alike.
- Its UI is intuitive while being easy to navigate. You really don’t need any technical expertise to use its dashboard or define policies within it.
- The customer support is excellent. You get documentation that’s easy to comprehend with technical assistance that is very responsive.
Cons:
- While the interface is user-friendly, I can say the same about the initial configuration process. Some users, especially beginners, will find the tool tough to set up and configure.
Verdict: If you are looking for an alternative to Sophos that is feature-rich, and robust in its ability to manage endpoints, then you’ll like Ivanti. The comprehensive device control capabilities and advanced DLP features are some of its strongest aspects. I feel the tool is ideal for those who prioritize data protection and security.
Price: You’ll need to contact the Ivanti team for a quote. You can also request a free live demo by filling up the form that’s presented on their official website.
Website: https://www.ivanti.com/products/device-control
#6) CrowdStrike
Best for integration with endpoint protection platform.

CrowdStrike is yet another powerful device control solution that I would like to recommend for preventing data breaches and unauthorized access. It comes jam-packed with advanced features that are critical to monitoring and controlling the use of peripheral devices.
Functionality: Like the other tools on this list, CrowdStrike too offers granular device control capabilities. The tool allows you to define policies comprehensively. In just a few steps, you’ll be able to manage and restrict the use of several devices accessing your network. Defining policies is very flexible and suitable for ensuring the safety of sensitive data.
Usability: The user interface is also solid. You’ll have no issue managing or configuring security policies with the dashboard it provided you to work on. You also get a clear overview of policy violations, device activity, and alerts. It is very simple to navigate through the settings and policies you’ve defined, thus making the tool ideal for beginners and professional users.
How to Use CrowdStrike for Device Control
- Launch the CrowdStrike Falcon agent on the endpoint you wish to protect.
- Log into your CrowdStrike Falcon management console with your credentials.
- Start defining security policies based on your organization’s requirements.
- Configure device permissions and define restrictions for specific device types or classes.
- You have the option to implement content-aware policies to prevent unauthorized data transfers as well.
- Deploy the policies once you’ve defined them.
- You can regularly fine-tune the policies as per changing circumstances.
Here is a video tutorial for your reference:
Features:
- Automatic Visibility: You get automatic visibility across USB device usage once the software’s launched. The software automatically discovers and captures a device’s information.
- Pre-Built Dashboard: CrowdStrike’s dashboard is one of its standout features. The dashboard is easy to navigate and offers intuitive search functionality.
- Granular Policy Control: The software offers granular access rights. It is very easy to create policy workflows using this tool. You can also test the policies before enforcing them.
- Content-Aware Data Protection: You can use the software to define policies based on regular expressions, keywords, and file types. This is essential for preventing the leakage of certain types of confidential data, like financial records and PII.
- Compliance and Reporting: The software offers detailed logs and activity reports. It ensures your organization is complying with the regulatory framework that applies to your industry.
Why I Like It: CrowdStrike is very effective in mitigating risks that are often associated with USB devices. The software gives you complete visibility to monitor the use of external storage devices in your environment. It is also very easy to define and manage policies with the help of this tool.
Pros:
- The software integrates seamlessly with CrowdStrike Falcon’s EPP platform. This integration arms organizations with a unified security ecosystem with both device control and advanced threat detection capabilities.
- The software offers extensive documentation and responsive technical support. There are comprehensive guides, knowledge-based, and other online resources to assist users.
- The software offers both activity reports and compliance reports. Both are essential for complying with regulatory frameworks like GDPR and HIPAA.
Cons:
- While the software’s designed to scale, complex deployment for some large-scale enterprises may require additional planning and resources.
Verdict: CrowdStrike offers a comprehensive set of features that all work in tandem to offer excellent device control and endpoint security benefits. The user-friendly interface, granular device control, and real-time monitoring capabilities make the tool worth every penny you spend on it.
Price: You’ll need to contact the CrowdStrike team to request a quote. They’ll assess your requirements in order to come up with a quote that’s fair. Alternatively, you can also request a free demo.
Website: https://www.crowdstrike.com/products/endpoint-security/falcon-device-control/
#7) SentinelOne
Best for AI-powered security.

With SentinelOne, you get an AI-powered cyber-security solution that’s quite advanced and sophisticated in its ability to detect and eliminate threats. For device control, the tool is just as efficient as Sophos or any other tool I’ve mentioned on this list.
Functionality: SentinelOne is very easy to use when it comes to defining device control policies or configuring settings to meet your specific needs. Where SentinelOne truly sets itself apart is in the behavioral AI engine it leverages. The software is quite effective in analyzing and identifying patterns of harmful user behavior.
It uses advanced machine learning technology to accurately detect and block emerging threats. The software is excellent when facing file-less attacks and zero-day vulnerabilities.
Usability: Like Endpoint Protector and Sophos, SentinelOne too offers a UI that’s accessible to even the most technically inept users. SentinelOne is one of those tools that’s bolstered by a single-agent architecture. This means low resource consumption and streamlined deployments.
Users only need to rely on a single management console to switch between SentinelOne’s various capabilities in an instant.
Further Reading => List of the BEST Fortinet DLP Alternatives
How to Use SentinelOne:
- Launch the SentinelOne management console with your login credentials.
- Go to the ‘Policies’ section.
- Navigate to ‘Device Control’.
- In the ‘Device Control’ section, start defining and configuring policies based on your organization’s requirements.
- You can set permissions and password protection to authorize and restrict access to certain devices.
- Once you have a clear-cut policy defined, save it, and deploy it to all applicable endpoints.
Here is a video tutorial for your reference:
Features:
- ERP Integration: You’ll have no issue integrating SentinelOne with other existing endpoint protection platforms on your network. Its software can seamlessly integrate with threat intelligence feeds, security orchestration tools, and existing SIEMs.
- Next-Gen Anti-Virus: The software’s great at blocking malware and virus attacks in its tracks. It leverages AI and advanced machine learning models to block both old and emerging threats.
- Automated Threat Response: With automated threat response, the software considerably reduced the need for costly and time-consuming manual intervention. The software immediately isolates a compromised endpoint to prevent the spread of a virus or malware.
- Endpoint Detection and Response: The software’s quite comprehensive when it comes to its EDR capabilities. Once launched, the software proactively investigates potential threats and responds to them in an appropriate manner.
Why We Like SentinelOne: Backed by advanced AI and machine learning technology, you can bet SentinelOne is extremely powerful and reliable in both its functionality and usability. You get better control and visibility over all your endpoints. Plus, the threat detection and response by this tool are very effective.
Pros:
- The software is bolstered by a single-agent architecture. Users will get better endpoint protection and resource consumption is also fairly low.
- The software proactively isolates infected endpoints to contain the spread of malware or virus. The software automates threat response.
- The software offers comprehensive reporting and real-time monitoring capabilities. This makes it easier for IT admins and security teams to respond to threats.
Cons:
- I wouldn’t advise this tool to large enterprises. It isn’t that scalable and will serve small to mid-sized businesses well.
Our Review: SentinelOne is great when it comes to defining and configuring device control policies. Its true benefit, however, lies in its AI-backed threat detection capabilities. The automated threat response feature alone makes the tool a great cybersecurity solution.
Price: To get a clear quote, you’ll need to call the SentinelOne team. They’ll offer a quote that’s customized to your business’s scale and specific requirements. You can also request a free demo.
Website: https://www.sentinelone.com/
Frequently Asked Questions
What is device control in endpoint security?
Device control solutions are technology designed to monitor and control the transfer of data between endpoints, removable storage devices or connected peripherals such as printers.
These solutions let IT administrators get better control over all devices currently accessing an organization’s network. They can define and enforce policies that restrict or authorize the use of peripheral devices. For instance, you can use a device control solution to determine whether to block a particular USB device, whitelist it, or render it read-only.
What is Sophos Device Control?
Sophos Device Control is a software that allows users to put restrictions on the use of certain external devices. These devices include printers, USB devices, SSDs, Hard Disks, wireless connection technology, and other peripheral devices.
Does Sophos slow down your computer?
Many Sophos Endpoint Protection users have reported widespread system slowdown, especially on Windows 10 and 11 devices. There’s a chance that Sophos could affect your system’s performance.
What are the Sophos Device Control alternatives for enterprises?
In my assessment, the following five tools can be viable alternatives to Sophos, particularly in terms of Device Control:
– Netwrix Endpoint Protector
– Bitdefender
– Ivanti
– CrowdStrike
– SentinelOne
You’ll find a detailed review of each of the above tools further down below in this article.
What is USB Device Control?
USB Device Control refers to a security feature or policy that regulates how USB devices can interact with a computer or network. This includes allowing or denying permissions for data transfers between the USB devices and the computer system.
By implementing USB device control, organizations can prevent data leakage, malware infections, and unauthorized access to sensitive information, enhancing overall data security.
Also Read =>> Compare various USB Device Control Software Tools
What are the Sophos Device Control Alternatives for small businesses?
Owing to their scalability and the support offered, I believe that Netwrix Endpoint Protector, SentinelOne, and BitDefender are great alternatives to Sophos Alternatives.
Conclusion
Sophos is one of the best device control solutions out there but it isn’t the only one. No tool, even the ones that are as powerful as Sophos, will cater to your every need. Therefore, it is wise to keep certain alternatives in mind. The 5 Sophos Device Control Alternatives we’ve mentioned above are very effective at enforcing granular device control policies as well as preventing data leakage.
They also are easy to use, highly scalable, and feature-rich. These are tools you can rely on to secure endpoints across your network environment and make sure there isn’t any unauthorized access.
As for my personal recommendations on Sophos Device Control Alternatives, I recommend you go with Netwrix Endpoint Protector for its user-friendly interface, policy customization, and advanced DLP features.
Research Process:
- We spent 12 hours researching and writing this article so you can have summarized and insightful information on which Sophos Device Control Alternatives will best suit you.
- Total Sophos Device Control Alternatives Researched: 35
- Total Sophos Device Control Alternatives Shortlisted: 5











