Afraid of data breaches? Discover the top Malwarebytes Device Control Alternatives for device control and endpoint security:
Device Control, offered by digital security platforms, allows businesses to restrict unauthorized access to their endpoints, safeguarding their data from breaches and insider threats.
According to IBM’s Cost of a Data Breach Report 2023, the average number of days that it takes an organization to identify and remediate a data breach is 277. Data breaches that were identified and contained after more than 200 days cost an average of $4.95 million to businesses, while those that were identified within 200 days cost an average of $3.93 million.
With the digital transformation of businesses and the increasing number of data breaches and other cyber threats, businesses are now realizing the importance of data security and the need for a powerful device control platform to prevent unauthorized access to important data.
Table of Contents:
Malwarebytes Device Control

Malwarebytes is a leading, award-winning device control platform, used by businesses across the world. Its device control products include:
- Malwarebytes Endpoint Protection
- Malwarebytes Incident Response
- Malwarebytes Endpoint Detection and Response
Malwarebytes is highly trusted due to its intuitive, scalable, and easy-to-configure platform. Its customer base is mainly small to mid-sized businesses, and, based on reviews, very satisfied with the solution.
Malwarebytes protects endpoints, preventing data from unauthorized transfers to external storage devices. With Malwarebytes Device Control, policies can be set to allow read-only or full access to a device or block full access altogether.
Here is a video that details the Device Control features:
Price plans offered by Malwarebytes are:
- Malwarebytes Endpoint Protection (10-99 devices): $4.96 per device per month
- Malwarebytes Endpoint Detection and Response (10-99 devices): $6.02 per device per month
- Malwarebytes Endpoint Protection for Servers (1-20 devices): $8.85 per device per month
- Malwarebytes Endpoint Detection and Response for Servers (1-20 devices): $10.63 per device per month
*Contact directly for a price quote for 100+ devices.

In this article, we have come up with detailed reviews about the top best alternatives to Malwarebytes.

[image source]
Why look for an alternative to Malwarebytes?
Malwarebytes is one of the best device control platforms in the industry. But, some businesses look for alternatives due to various reasons, including:
- Issues while integrating the platform with their existing workflow
- Too many false positives
- A more cost-efficient solution
- More advanced features
- Specific features, in addition to Device Control
Further Reading => Is Malwarebytes Safe: Check Detailed Review
How we chose the top alternatives to Malwarebytes:
We have provided a well-researched list of the best cybersecurity platforms that are good alternatives to Malwarebytes. The top attributes that we looked upon while picking up the platforms for our list are:
- The range of features
- Customer reviews
- Customer support
- Compatibility with multiple operating systems
- Ease of use
- Scalability
- Value for money
Market Trends: According to a report by Verified Market Research, the global Access Control market size was more than $8.5 billion in the year 2021, which is now expected to expand at a Compound Annual Growth Rate (CAGR) of 8% over the years from 2023 to 2030, and reach the net value of $17 billion by 2030.
This expansion can be attributed to the following factors:
- Increased data security concerns
- Growing number of cyber threats
- Increasing use of wireless technology and electronic devices

List of the Best Malwarebytes Device Control Alternatives
Here are some popular competitors to Malwarebytes:
- Netwrix Endpoint Protector
- NinjaOne MDM
- ManageEngine Device Control Plus
- Eset Endpoint Security
- Microsoft Defender for Endpoint Device Control
- Sophos
- CrowdStrike Falcon
Comparing Malwarebytes Device Control With Alternatives
| Platform | Best for | Benefits | Compatibility |
|---|---|---|---|
| Malwarebytes Device Control | An intuitive endpoint security platform that gives good value for money | ● Intuitive platform ● Scalable ● Suitable for businesses of all sizes | Windows, Mac, iOS, Android, Linux |
| NinjaOne MDM | Centralized endpoint and mobile device management | ● Fast deployment ● Unlimited free training and support ● Easy-to-use dashboard | Windows, macOS, Linux, Android, Apple |
| Netwrix Endpoint Protector | Advanced tools for controlling USB and peripheral ports | ● Easy to use ● Zero-day support services ● Simple deployment | Windows, Mac, Linux |
| ManageEngine Device Control Plus | Protecting devices from removal and peripheral devices. | ● Simple set-up ● User-friendly interface ● Real-time monitoring | Windows, Web-based |
| Eset Endpoint Security | A unified cybersecurity platform | ● Reasonable pricing ● Customizable solutions ● 24/7/365 support | Windows, Mac, and Android devices |
| Microsoft Defender for Endpoint Device Control | Powerful, real-time threat protection tools for businesses of all sizes | ● Integration with Microsoft solutions ● Near-instant detection and blocking of threats ● Useful automations | Windows, Mac, iOS, and Android devices |
| Sophos | An easy-to-use and cost-effective platform | ● Easy deployment ● 24/7 English-only support ● Advanced automations | Windows, Chrome, Mac, iOS, Android and Linux |
| CrowdStrike Falcon | A feature-rich platform that gives good value for money | ● Highly scalable ● Seamless integration with existing workflows ● Easy deployment, instant operationalisation | Windows, Mac, Linux, iOS, and Android devices |
Detailed Reviews:
#1) Netwrix Endpoint Protector
Best for offering advanced tools for controlling USB and peripheral ports.

Netwrix Endpoint Protector is one of the best device control platforms in the industry today. The platform offers detailed device control and data loss prevention features while ensuring business continuity. You can visit their YouTube page to find plenty of video tutorials in many languages about each feature.
Netwrix Endpoint Protector is available as a Cloud service (AWS, Azure, Google Cloud Platform) or as a virtual appliance. The advanced, deep scanning, e-discovery, and device control features, along with its ease of use, have compelled us to add this platform at the #1 spot in our ‘Top Malwarebytes Device Control Alternatives’ list.
The platform makes protection of Intellectual Property (IP), Personally Identifiable Information (PII), and other sensitive data, as well as compliance with local and federal regulations, feasible for businesses of different industries including Consulting, Healthcare, Law, Pharmaceutical, Accounting, Education, Finance, Manufacturing, IT & Software, Media, Insurance, Advertising, and Aerospace.
Why it is a good alternative to Malwarebytes Device Control: Netwrix Endpoint Protector offers simple yet powerful tools for protecting your company’s data while maintaining business continuity. With Endpoint Protector, you can set access control policies based on users, devices, and more.
Plus, it’s a highly scalable platform that offers multi-OS support and simplified deployment.
How it works: Netwrix Endpoint Protector works by offering you tools for Device Control, Content Aware Protection, Enforced Encryption, and eDiscovery.
Watch this video showing a demo of the Device Control feature:
Features we like most:
- Offers granular control and policy customization tools including restrictions based on device type, brand, serial number, and more
- Scanning of data in motion, based on content inspection.
- Compatible with Windows, Mac, and Linux
- Offers tools for controlling more than 40 different device classes
- Data loss prevention tools including file tracing and file shadowing, allowing to track sensitive data
Pros:
- User-friendly interface
- Simplified deployment
- Scalable platform
- Zero-day support for Mac and Windows
- Helps in addressing compliance regulations including NIST, GDPR, HIPAA, PCI DSS, CCPA, and LGPD
- Supports Czech, German, English, Persian, French, Hungarian, Italian, Japanese, Korean, Polish, Portuguese, Romanian, Russian, Spanish, Thai, Turkish, Vietnamese, Chinese (Simplified), and Chinese (Traditional) languages.
Cons:
- Less features for Linux users.
Our review: Netwrix Endpoint Protector is trusted by renowned companies like Samsung, Western Union, ING, AON, and more. And, they have quite impressive reviews. Its scalable platform has won many prestigious awards for its excellence in cybersecurity.
I would highly recommend Netwrix Endpoint Protector for businesses of all sizes.
Price: Contact directly to get a price quote.
#2) NinjaOne MDM
Best for Centralized endpoint and mobile device management.
NinjaOne is a cloud-native solution that can be used by enterprises to gain better control and visibility over all devices within their IT estate. This includes Android and Apple smartphones alongside Linux, macOS, and Windows running systems.
The software considerably improves the user-experience via remote, automated device enrollment. Once the device is enrolled, managing certain aspects related to it becomes very simple. For instance, you’ll be able to take remote actions like device lock or passcode reset to mitigate security risks.
You’ll also have the ability to install and remove applications on all devices across operating systems. The software also features an intuitive geolocation service. You can use this feature to track mobile devices in your inventory. The geolocation services prove immensely helpful in preventing device loss.
Why is NinjaOne a Better Alternative to Malwarebytes:
NinjaOne has one of the best interfaces that we’ve come across when it comes to device management solutions. Whether it is enrolling a device or taking remote actions, everything is simple because of its intuitive interface.
You are also provided with unlimited training and support for free. It is easier to overcome NinjaOne’s learning curve because of this. Furthermore, deployment is also quite brisk with this tool. You can have it up and running within a month or just a few days.
How It Works:
Managing devices on NinjaOne requires the creation of policies. To do so, you’ll need to follow the steps below:
- Go to Administration on your console, then click Policies.
- Under Policies, find MDM policies, and select “Create New Policy.”
- You can then create a policy or choose a pre-existing one.
- Configure the policy, save, and deploy.
Features:
- Mobile Application Management
- Unified policy-based management
- Geolocation services
- Single and Multi-app kiosk mode.
Pros:
- Fast and easy deployment
- Centralized management of all devices
- Unlimited free onboarding training and support.
- Flexible annual and monthly plans.
Cons:
- A learning curve may apply to some users.
Our Review: NinjaOne is a very popular endpoint management software that also features robust mobile device management capabilities. It is easy to use and will help you manage both mobile devices and computer systems across multiple endpoints and operating systems through a centralized dashboard.
Price: You’ll need to contact the NinjaOne MDM team for a clear quote. A free trial and demo are also offered upon request.
#3) ManageEngine Device Control Plus
Best for protecting devices from removal and peripheral devices.
Device Control Plus is why ManageEngine is one of the most sought-after vendors of security solutions out there. This is a tool that serves as both an efficient device control as well as file access management solution. Once launched, you can use it to completely secure your devices from all sorts of removable devices.
For instance, you’ll be able to set-up read-only access to block certain devices from copying files. You can crack down on devices by the simple implementation of policies. The software keeps an unwavering eye on all data transfers. You can set up policies to restrict the transfer of certain file types or limit the transfer of files based on their size.
Why Is it a good alternative to MalwareBytes?
I like the fact that Device Control Plus takes a zero-trust approach to secure enterprise data from certain removable devices. The software creates a list of trusted devices. It leverages this list to only allow authorized devices access to your endpoints.
The software is also very simple to use. You get expertly crafted dashboards to play with. You can impose device control policies at a granular level in a couple of simple steps. You also get extensive reports that are easy to comprehend.
How it works?
As I mentioned before, Device Control Plus can help you control and regulate the access of peripheral devices. For the sake of this guide, let’s see how you can block USB devices using this software.
#1) Launch the software
#2) Navigate to the “Policies” tab and click on “Create Policy”
#3) Now, select the block option from the drop-down menu against “Removable Storage Devices”.
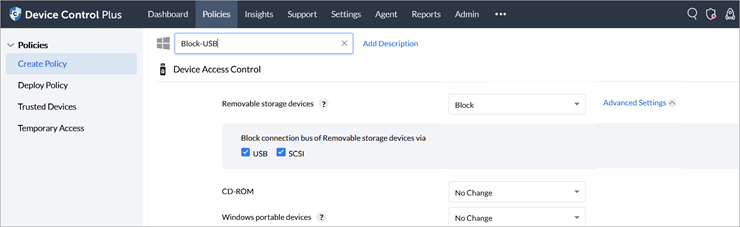
#4) Based on your preference, you can choose to block the connection bus of removable devices via USB or SCSI.
#5) Select “Save and Publish” to enforce this policy.
Features we like the most:
- Create secure and temporary access for devices
- Control all ports and connected removable devices
- Enforce role-based access control policies.
- Limit file transfers by setting a cap on the maximum size of files that can be transferred out of your device.
- Create a trusted device list to only ensure access to authorized devices.
Pros:
- Very simple to set up
- Easily configure device control policies.
- Intuitive and easy-to-navigate interface
- Monitor file actions in real-time
- File shadowing.
Cons:
- It is expensive.
Our review: ManageEngine is far more comprehensive when it comes to device control than MalwareBytes. This is a tool we’d recommend to mid and large enterprises who have a large pool of sensitive data to protect. It is simple to use and you should have no problem securing your endpoints from removable devices with this software.
Price: Device Control Plus starts at $595 per annum. You can also request a custom quote based on your specific requirements. A free demo and trial are also available.
#4) Eset Endpoint Security
Best for being a unified cybersecurity platform.

Eset Endpoint Security is a flexible device control services provider. They help you set control permissions based on device parameters such as serial number, manufacturer ID, model, and more.
Their device control feature supports many external devices including disk storage, CD/DVD, USB storage, USB printer, FileWare storage, Bluetooth, Smart Card reader, imaging, modem, LPT/COM port, portable device, and more. Eset allows you to set actions to be taken whenever an external device is inserted or connected to the network.
They also help you in adapting a unique, multi-layered approach to security, through their ESET LiveSense technology, machine learning expertise, cloud reputation system, and other resources.
Here is an overview of Eset Endpoint Security:
This cyber threat prevention, detection, and response platform was launched in 1992 with the values of integrity, reliability, passion, and courage, and, today, has 13 R&D centers where hundreds of experts from all over the world work to improve cybersecurity. Their team was involved in some high-profile discoveries like Industroyer, KrØØk, and Lojax.
Why it is an excellent alternative to Malwarebytes Device Control: Eset is a highly scalable platform that offers robust, detailed device control features for businesses. Eset offers more flexible pricing options to its customers as compared to Malwarebytes.
How it works:
#1) Open the Homepage of your Windows ESET application, then press the F5 key to open the Advanced setup page. Then, click the Device Control option, enable it, and restart your computer.

#2) Open the Advanced setup page, then click on ‘Edit’ found next to Rules. From here, you can set device control rules as per your needs.
Watch a demo of the Device Control feature here:
Security services offered by Eset:

Features I like:
- Real-time visibility for endpoints including desktops, servers, virtual machines, and even managed mobile devices
- Connect anytime from anywhere from any web browser
- Dynamic, built-in, and custom reporting tools
- Advanced threat defense features help in improving the detection of zero-day threats
- Granular policy control features that allow businesses to set up multiple policies for a system
Features offered in different subscription plans:

Pros:
- Security for Windows, Mac, and Android devices
- Free version for Android users
- Customizable security solutions
- Free trial
- Reasonable pricing
- Available customer support 24/7/365
Cons:
- Can be a bit hard to use at the beginning, but the all-time-responsive customer support helps you get the best experience.
Technologies used by Eset Endpoint Security for detecting and blocking a threat:

Why we choose it: Eset claims to serve more than 400k businesses coming from 195 countries and protects over 1 billion users through their technology. Their customer support services are good. They offer different plans for homes and businesses. I found this platform to be suitable for organizations of all sizes.
Price: Contact them directly for a price quote.
Website: https://www.eset.com/int/business/enterprise/
#5) Microsoft Defender for Endpoint Device Control
Best for offering powerful, real-time threat protection tools for businesses of all sizes.

Microsoft Defender for Endpoint Device Control (now known as Purview) is a leading endpoint security platform built to protect enterprise networks by preventing, detecting, investigating, and responding to advanced threats to endpoints including laptops, phones, tablets, PCs, access points, routers, and firewalls.
Features offered by Microsoft Defender include:
- Anti-malware and antivirus protection, attack surface reduction, centralized management, security reports, APIs, device discovery, vulnerability management, threat analytics, automated investigation and response, advanced hunting, endpoint attack notifications, and more.
Also, refer to How to access and onboard unmanaged devices that Microsoft Defender for Endpoint discovered.
Why it is a good alternative to Malwarebytes Device Control: Microsoft Defender is a feature-rich, highly customizable threat protection platform for businesses of all sizes, while Malwarebytes is most suitable for small- to medium-sized businesses.
How it works:
Microsoft Defender 365 homepage looks like this:

From here, you can view all incidents, and alerts, track remediation, manage devices, view reports, and more.
What we like:
- Helps in reducing attack surface by targeting certain software behaviors, detecting configuration gaps, and more
- Tools for antivirus scanning, device isolation, and more
- Ransomware mitigation tools, that help in controlling folder access, to be allowed for trusted apps only
- Web threat protection tools, including preventing access to phishing sites, malware vectors, exploit sites, low-reputation sites, and sites that you have blocked
- Tools for assessing and onboarding unmanaged devices, discovered by Microsoft Defender
- Discovers network devices, classifies them, and adds them to the asset inventory
Pros:
- Near-instant detection and blocking of new and emerging threats
- Compatible with Windows, macOS, iOS, and Android devices
- Centralized management of threat protection settings
- Automation tools for investigation and response management
- A free trial
- Integration with Microsoft solutions
Cons:
- Sends too many alerts at times
Our review: Microsoft Defender is a reliable platform that offers a wide range of features for safeguarding your business from various threats. I picked Microsoft Defender for this spot in our list because of its impressive ratings and reviews, as well as its usability for businesses of all sizes and types.
Price: Contact directly to get a price quote.

Website: https://learn.microsoft.com/en-us/microsoft-365/security/defender-endpoint/microsoft-defender-endpoint?view=o365-worldwide
#6) Sophos
Best for being easy to use and cost-effective.

Sophos is a leading Managed Detection and Response services provider with more than 15,000 customers from all over the world.
They offer their security services in two ways:
- With the help of a team of experts, who work to detect and eliminate advanced threats on your behalf
- With the help of their centralized cloud security platform
You are free to choose either their managed services or platform for endpoint, network, email, and cloud security.
Sophos offers you intuitive yet powerful dashboards, with reporting, analytics, visualization, and other tools. It offers seamless integration with Kaseya, ConnectWise, Autotask, and more, for enhanced automation.
This video illustrates how to use the App and device control feature with Sophos:
The device control features provided by Sophos help in reducing the risk of network bridging between a corporate network and a non-corporate network. It offers you a ‘Block bridged’ mode, which is available for wireless and modem types of devices. It disables the wireless or modem network adapters, whenever an endpoint is connected to a physical network.
Why it is a good alternative to Malwarebytes Device Control: Sophos allows you to select devices to control and lets you decide which device types to block, and which, if any, devices should be exempt. It also allows you to detect and block devices or simply give read-only access to the storage devices.
Moreover, it is easy to use and works with all of your desktops, laptops, servers, tablets, mobile devices, and all major operating systems.
Solutions offered by Sophos Intercept X Endpoint: Sophos offers solutions for the following use cases:

What I like:
- Device control features, including blocking devices based on a specific type, allowing read-only access to storage devices, and more
- Centralized security management and operations, intelligent endpoint detection and response
- Isolates infected endpoints and blocks lateral movement
- Restricts Wi-Fi for non-compliant mobile devices, scans endpoints when compromised mailboxes are discovered
- Identifies apps that are available for access by the users
Pros:
- Compatible with Windows, Chrome, macOS, iOS, Android, and Linux
- Easy to use
- Easy deployment
- Free trial
- Rich set of open APIs
- 24/7 English-only support
- Support is also available in other languages including French, Italian, Spanish, Japanese, and Portuguese
Cons:
- Customer support services can be improved
Verdict: Sophos offers powerful yet simplified, cloud-based threat protection services. It gives you tools for accessing and managing your endpoint security anytime, from anywhere. Customers of Sophos have reported an 85% reduction in security incidents and a 90% reduction in the time taken to identify issues.
I found Sophos to be most suitable for small to medium-sized businesses.
Price: Contact us directly to get a customized price quote.
Website: https://www.sophos.com/en-us/products/endpoint-antivirus
#7) CrowdStrike Falcon
Best for being a cost-effective, feature-rich platform.

CrowdStrike Falcon is a cloud-native, complete cybersecurity solutions provider. It is a unified platform for XDR, EDR, Net-Gen Antivirus, Firewall Management, Device Control, Cloud Security Posture Management, Threat Hunting, Malware Analysis, Situational Awareness, and more.
Learn how Crowdstrike detects and prevents intrusion campaigns:
It offers solutions for preparing, responding to, and fortifying threats. Features offered for preparing for threats include Tabletop Exercises, Red Team/Blue Team Exercises, Adversary Emulation Exercises, and Penetration Testing.
Response features include incident response, compromise assessment, endpoint recovery, and network detection. Solutions offered for fortification include maturity assessment, technical risk assessment, SOC assessment, and active directory assessment.
You can also opt for their managed services, where you get a team of experts to remotely configure and operate the security process.
Why it is a good alternative to Malwarebytes Device Control: CrowdStrike Falcon is an AI-powered, feature-rich, unified platform for 24/7 security of your cloud infrastructure. It is easy to use and offers good value for money. Their device control features are praiseworthy. It offers you tools for complete functional management of your USB device policy.
Here is a video to see a demo of the device control feature offered by CrowdStrike Falcon:
CrowdStrike Falcon offers the following services for threat remediation:

Features:
- Real-time visibility tools enable you to investigate and respond to threats immediately.

- Offers actionable insights based on over 15 petabytes of data of more than a trillion events per day spanning across 2 trillion vertices
- Intuitive dashboards that allow you to manage policies

- Cloud security posture management, e-discovery, and advanced device control features
Pros:
- 15-day free trial
- Scalable platform
- Seamless integration with your existing workflows
- A wide range of features
- Helps in meeting your compliance requirements
- Easy deployment, instant operationalization
Cons:
- The customer support services are reportedly not good
Our review: CrowdStrike Falcon is trusted by companies like Deloitte, Expensify, Verizon, Netlify, and Lands’ End. The platform claims to capture more than 1 trillion events per day and protects over 2 trillion vertices.
With CrowdStrike Falcon you will get good value for your money. Plus, you get protection for your data, even when the endpoints are offline.
Price: CrowdStrike Falcon offers different product bundles:
- Falcon Go: $299.95 per annum
- Falcon Pro: Contact directly for a price quote
- Falcon Enterprise: Contact directly for a price quote
- Falcon Elite: Contact directly for a price quote
- Falcon Complete: Contact directly for a price quote.
Website: https://www.crowdstrike.com/falcon-platform/
Frequently Asked Questions
Is Malwarebytes trusted?
Malwarebytes is a leading cybersecurity services provider with millions of customers, offering plans for homes, businesses, and enterprises, delivering good value for money.
Which solutions are better than Malwarebytes?
Based on our study, the top alternatives to Malwarebytes based on customer reviews, features, and other aspects are Netwrix Endpoint Protector, Eset Endpoint Security, Microsoft Defender for Endpoint Device Control, Sophos Intercept X Endpoint, and CrowdStrike Falcon.
Does Sophos detect ransomware?
Sophos Intercept X Endpoint is one of the best platforms for detecting ransomware. The advanced automation that they offer for detection and response is noteworthy. It automatically isolates infected devices, instantly detects and removes malware, and offers centralized tools for security posture management.
Suggested Read =>> Sophos Device Control Alternatives with features
What is cybersecurity?
Cybersecurity refers to safeguarding the digital assets of individuals and businesses. Since organizations are rapidly digitizing their operations, cases of data breaches are also increasing and have caused significant losses. Most businesses look for a platform that can undertake the tasks of securing data from both insider and outsider threats.
What is Microsoft Defender?
Microsoft Defender is a reliable, powerful, endpoint security platform, trusted by businesses of all sizes, all over the world. It offers tools for instant detection and blocking of threats, automated investigation and response, and integration with other Microsoft solutions.
Conclusion
There are plenty of device control solutions available in the industry to choose from. But, picking the most suitable platform for your business can be a critical task.
Your device control platform must be easy to use and it must not hinder business continuity. Free trials are offered by most of the security platforms that can be used in determining whether the platform suits your needs or not.
Automation tools help in the instant detection and remediation of threats, thus making the process easier for businesses. Plus, 24/7 customer support would be quite helpful, in case you need immediate help.
Based on all these aspects, we have picked Netwrix Endpoint Protector, Eset Endpoint Security, Microsoft Defender for Endpoint Device Control, Sophos Intercept X Endpoint, and CrowdStrike Falcon to be the best, most powerful Malwarebytes Device Control Alternatives.
Research Process:
- Time taken to research this article: We spent 22 hours researching and writing this article so you can get a useful summarised list of tools with a comparison of them for your quick review
- Total tools researched online: 36
- Top tools shortlisted for review: 5










