This Tutorial discusses the Basics of Blockchain Security. Also explains how Cryptography, Digital Signatures, Hashings, and Private and Public Keys work to Secure Data:
In the previous Blockchain ETF tutorial of the Blockchain tutorial series, we have learned about the workings of Blockchain ETF along with their comparison with other assets.
The security of data is paramount to blockchains and how they operate. For instance, top-notch security prevents digital assets like cryptocurrencies on a blockchain from being duplicated or destroyed.
Several methods ensure top-notch security of data and information inside of blockchain including the advanced cryptography techniques and mathematical models of the behavior and decision-making.

In this blockchain security tutorial, we will learn the basic concepts of security inside a blockchain to understand what makes a blockchain secure, and the basics of cryptography. We will also look at how decentralization, consensus, and crypto-economics ensure the security of blockchains.
We will also consider some tips on making blockchain more secure, the basics of quantum security, and the concept of quantum-resistant blockchains.
Table of Contents:
- Why Is Blockchain Security Critical?
- Factors Contributing To Blockchain Security
- #1) Consensus And Immutability
- #2) Cryptography And Its Role In Blockchain Security
- #3) How Do Private And Public Keys Work To Secure Data?
- #4) Creation Of Digital Signatures
- #5) How Hashing Helps To Secure Data In Blockchain?
- #6) Crypto-economics And Blockchain Security
- #7) Quantum Computers And Quantum-Resistant Blockchains
- Conclusion
Why Is Blockchain Security Critical?
Let us understand the importance of security for blockchains and see the areas that need to be secured.
- Take for instance cryptocurrencies, if blockchain is not secure, cryptocurrencies can be copied, destroyed, or stolen. The same can happen for all messages so encrypted.
- Besides, the information so secured would no longer remain private or confidential. This would mean more insecurity, theft, and hijacking incidences, for instance when owners of huge amounts of crypto are known.
- Trustless smart contracts would be hard to do without assurance that the written agreement will not be altered.
Factors Contributing To Blockchain Security
#1) Consensus And Immutability

Consensus and immutability contribute to blockchain security in the following ways:
- Consensus, being the ability of nodes on the blockchain network to agree on the status of the network, ensures that the rules of securing the network are adhered to.
- The consensus algorithm defines those rules and how they are to be followed by anyone sharing the network. An important aspect of the consensus is the coding of those rules to ensure that the users adhere to the rules without having to trust each other.
- Immutability, on the other hand, is the ability of transactional data on a blockchain to not get altered or deleted. This is a technological functionality of the blockchain. The linking of blocks in a blockchain ensures that such changes would be transmitted to every node and node operator thanks to the consensus algorithm code. Node operators can technologically reject or accept those changes.
- If changes are rejected, the modified block is passed on as orphaned or disengaged from the main longest chain. The person who mines the block does not even receive the reward.
Therefore, the consensus secures the blockchain since it allows verifiers and nodes to disagree with changes that are unacceptable even as they agree on those that are acceptable to ensure the continuity of the chain. Immutability ensures the traceability of every piece of data and information secured on a blockchain, meaning that any kind of changes would be noticed.
#2) Cryptography And Its Role In Blockchain Security
Cryptography is the main security system of the blockchain. It allows the storing and exchanging of data in a format hidden from third parties and only the person who has the technological permission to unravel the meaning of the message can receive and decode the message sent to them.
The hashing algorithm converts easily readable data to data that can’t be understood without decryption:

Cryptography works by
way of hashing in addition to using public and private key pair security methods. Asymmetric and symmetric public key cryptography is the main way of securing data in a blockchain. In symmetric-key cryptography, one key is used to encrypt and decrypt data and information. DES and AES are examples of symmetric public-key cryptography.
These are employed in Email and Internet encryption methods such as TLS and SSL although these sometimes use a combination of symmetric and asymmetric key cryptography.
(i) Blockchains employ asymmetric public-key cryptography, which is more secure and uses different private and public keys to encrypt and decrypt data and information. The public keys are available publicly for instance via digital certificates.
The sender of information or crypto or whatever will use the receiver’s public key to encrypt data. The recipient will have the key to unravel the data by decrypting with the private key connected to the public key.
(ii) Of course, a third party cannot access the message as it is sent in an encrypted format or an unreadable format.
(iii) The holder of the private key is the person with the authority and right to decrypt the information contained therein, as proof of ownership.
(iv) A key generator is a computer program used to generate public and private keys in cryptography. These Random Number Generators (RNG) or Pseudorandom Number Generators (PRNG) use a degree of randomness to secure data.
(v) Keys secure data by being harder to find out. Let’s consider brute force, which is one of the ways of trying to decrypt encrypted data without having its associated private keys. Brute-force works by trial and error method where the software guesses multiple combinations of likely characters making the keys starting with the least number.
This software is quite fast and is used to successfully penetrate some encryption techniques and hack systems by guessing passwords and keys etc.
Brute-force is unable to break asymmetric public-key cryptography, first because the key composition and length make it hard to guess. Not only would it take forever to get it right, but also the resources needed would be unaffordable. Hence, while 128-bit encryption systems that produce 128-bit long keys are employed in symmetric key algorithms that are hard to crack, 2048 bits.
(vi) You can test random public and private key generators on bitcoinaddress.org by generating a Bitcoin wallet address and its private key manually. Both keys are generated offline while decreasing the possibility of being compromised.
This method uses sporadic user mouse movements to generate unique seeds and increase the degree of randomness which makes it harder – actually impossible – to guess the generated keys. This type of PRNG uses system entropy to seed data to the randomness process to make results hard to guess by way of making it hard to guess the initial conditions of the PRNG.
Other systems derive private keys deterministically using a passphrase and a key derivation function. These methods are employed in modern HD wallets that make it easy to generate and manage wallet addresses. All the private keys for all the wallet addresses in the HD wallet are generated using the same key derivation function and can be recovered with a single passphrase.
Cryptographic Algorithms
Cryptography can be strong or weak, measured by the time and amount of resources needed to recover the plaintext from its cypher text.
#1) Conventional encryption does a good job of securing stored data but can be very expensive when securing data in transit.
#2) Modern asymmetric public-private key cryptography solves the problem of distributing the keys. Methods such as OpenPGP use a hybrid of public-key cryptography (asymmetry encryption) and conventional cryptography.
Ciphers are mathematical functions that allow the encryption and decryption of information. It uses a key – which is a word, number, or phrase, to encrypt a plain text. Different keys will result in different cypher texts or hashes.
#3) A cryptographic algorithm collects random data to inject into its mathematical function and the plain message inputs to produce an encrypted cypher text.
The below image explains the working of the cryptography algorithm:
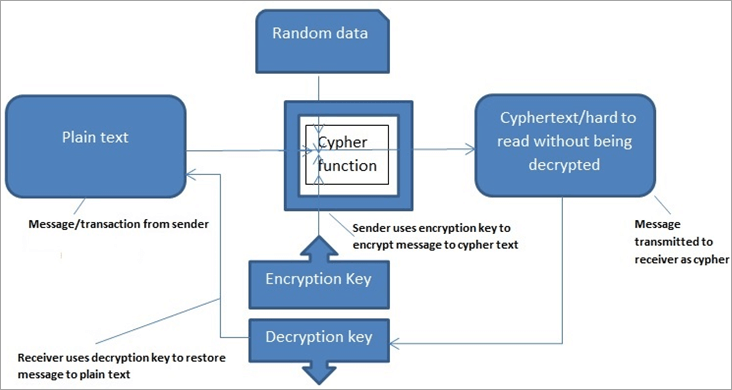
#4) Cyphers work using different strategies to hide messages. They may combine it with additional data, inverse, or transpose it, these are just a few examples.
#5) For instance, in symmetric key encryption, the algorithm might use transposition cyphers where the order of the units in plain text is reordered regularly to hide the message.
The used function or cypher is called a bijective function. The cypher text constitutes a permutation of plaintext. In this case, to decrypt the message, an inverse function is applied to the cypher text to restore the original order of the text and back to the plaintext.
#3) How Do Private And Public Keys Work To Secure Data?
(i) Cryptography with public and private key pairs is a mathematical process. Once the private key has been used to create a digital signature, the transaction is unique to any other and cannot be copied by anyone outside or inside of the blockchain.
(ii) A signature for a given transaction cannot be similar to a signature for a different transaction even when the same private key is used to generate the two signatures.
(iii) Further, in addition to the keys being hidden mathematically via hashing, the relationship between them is hard to unravel. Hence original message so secure is hard to find.
(iv) Securing data, information, and transactions with private and public keys relies on the idea that while it is easy to find the product of two large prime numbers, it is increasingly harder and impossible to find factors of a large number if it has only very large prime factors.
(v) This is because it would take many thousands of years to compute, by any method possible currently including the fastest computer, the factors of the number.
Two numbers are said to be congruent in modulus if the difference in them is divisible by the modulus. Number 30 is congruent to 9 modulus 7 because the difference between 30 and 7 is divisible by 7.
In other words, it is expressed as;
>> a b (mod l) if and only if a = kl + b where k is an integer, a and b are congruent and modulus to each other.
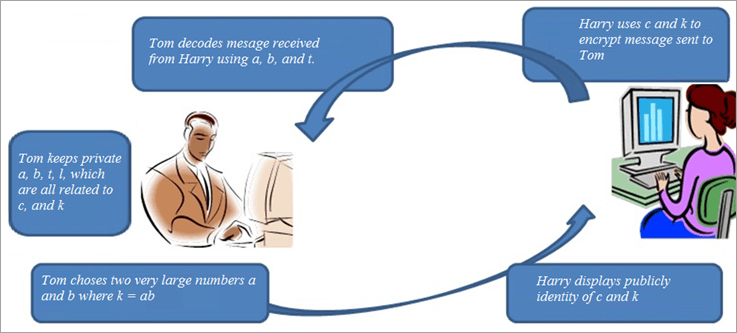
If Tom wants to receive a message from Harry, he is the only one capable of decoding the message even though everyone is capable of writing the message in code. Tom will choose two very large prime numbers a and b, then write k = ab and code the message using k but a and b are needed to decode the message.
Tom choses two numbers a and b where k = ab while l = least common multiple {a-1, b-1}
Tom, who wants to receive a private and secure message from Harry chooses d where c>1 and c is co-prime with l meaning c, l have no common factors.
Tom will also find unique t less than l, where ct = 1 (mod l).
Tom displays publicly the identity of c and k while keeping a, b, t private.
Harry then sends L a single number as the message to Tom; L and k are co-prime and they maintain the condition 0<L<k.
Harry finds Ld where Ld = Lc (mod k), and sends the message Ld to Tom.
After receiving the message Ld from Harry, Tom decodes it using a, b, c, t, l, k to find Ld.
To decode, Tom will use the theorem that;
Example;
- Harry sends message L to Tom; Tom chooses a = 17, b = 23; which means k = 39, l = 176, c = 3 and t = 59
- Tom tells Harry k = 391 and c = 3 (No one can find t even if they have k, and c).
- Harry calculates Ld = 180 using Ld = Lc (mod k) with knowledge of c and k.
- Tom receives coded message 180.
- Tom calculates Ld)t
L (mod k). L
18059 (mod 391) and decodes the secret message from Harry.
- The computer uses modul
us calculus to determine the results of the above function.
Ideally,
- If a
b (mod n), n divides a-b, and if n divides a –b then n divides (a-b)c = ac-bc which means ac
bc (mod n); and
- As ak
bk(mod n)
- The solution follows this example; To find x in the equation 0
x
100; and 173
x (mod 101);
- Since173 is too large for most calculators, we start with 176= 24137569 and first dividing by 101, we find that 176 = (238985)(101) + 84 so we know 176
84 (mod 101), which can be used to tackle
1713, which is = (176)2 x 17 which is 842 x 17
119952 (mod 10)
Hence x = 65.
#4) Creation Of Digital Signatures
Let us now understand how digital signatures are created in blockchain and their role in confidentiality.
Public keys are availed publicly although securely so through digital certificates for instance in website and email encryption jargon. The certificates are issued by Certification Authorities or CA.
The digital certificate contains personal information in the same way as the public key. The authenticity of a Digital Signature, which is itself signed, is proofed by verifying its signature. In email and web encryption, the public keys from CAs are used to verify the signatures of issued Digital Certificates before verifying the authenticity of the information and message.
In blockchains, the private key is used to digitally sign a transaction. Then the related public key is used to verify that the messages so created with the corresponding private keys are authentic by verifying the authenticity of the digital signatures on those messages. This is what happens when you send through a transaction from your private wallet to the blockchain system.
This way, private keys ensure the confidentiality of the sent data.
The creation of digital signatures is a mathematical computer process and follows the below processes:
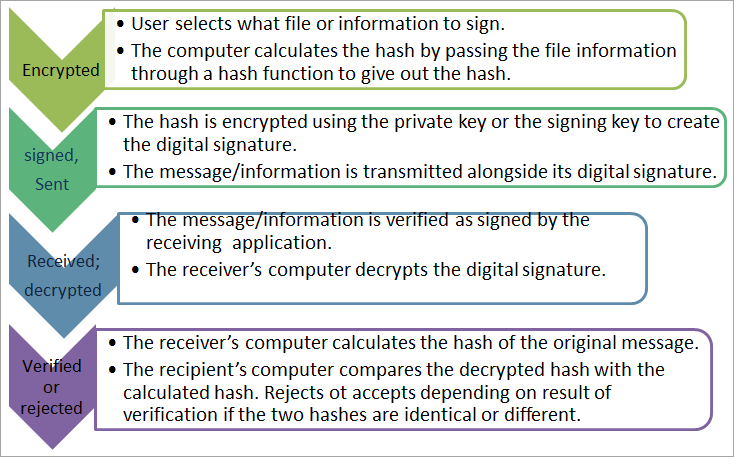
In the last step, the two hashes are identical when the message or transaction is not tampered with or altered. The message is verified as authentic; otherwise, it is rejected as tampered or not authentic.
Hence, if a transaction in a blockchain is altered, it results in a different hash from the one formed by the sender or his machine when sending, where the original transaction is first decrypted with the recipient’s private key.
This idea is used in the trading of cryptocurrencies back and forth, and to make crypto payments.
Other security strategies related to keys within blockchains are:
- Multi-signature wallet addresses protocol within blockchain allows the production of copies of keys to every owner-holder of the wallet. For instance, it applies when a wallet is owned by a family or company and three or more parties are required to sign a transaction to be allowed.
- With a multi-signature wallet, one party cannot spend crypto without others being witnesses. The transaction has to be signed by more than one party owning the key, to spend the funds.
- Some online wallets and blockchain systems use a multi-signature protocol where one private key is stored on a user’s device, the other saved by the user offline or in a separate place, and the other left with the service provider. Any of the two can unlock the wallet or service if one is lost or misplaced.
Moving on to online security, some systems allow the generation of private keys as one-time links for each session; known as the forward secrecy.
#5) How Hashing Helps To Secure Data In Blockchain?
In hashing, input data passes through a mathematical function or formula called a hashing function. The function converts the input into an output that makes no sense unless it is returned to its original message.
- The output must be of the same length regardless of the length of the input. For instance, in a Bitcoin blockchain, which uses the Proof of Work algorithm, SHA-256 is the algorithm used and it produces a hash that is 256 bits or 64 characters long.
- Two different inputs – even those that differ very slightly for instance by way of capital and small letter cannot have similar output.
- The same input renders the same output always without any variance to ensure consistency no matter how many times it is hashed via the function.
- The process is irreversible. It means starting with the output and hashing it does not produce the input that produces it.
Back to the blockchain, which is a chain of blocks each containing a set of data, the block has a hash or output generated concerning the data in the blockchain. Any change in the data would mean a requirement to change the hash. Plus since each block hash is also generated concerning the hash of the previous block, all the blocks are interlinked.
Therefore, a change of data in one block would mean a change in all block hashes. This is an important aspect of securing data in a blockchain as the data is securely interlinked in a blockchain is immutable.
Linking of block data, block identifiers/hashes, and blocks in a blockchain:
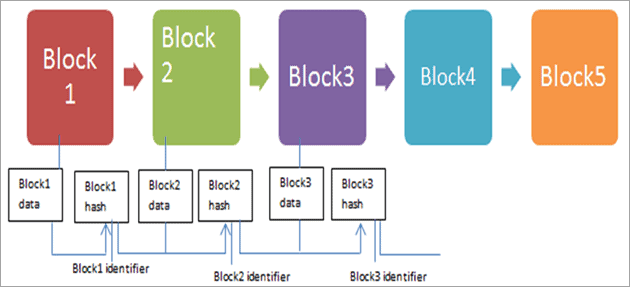
The hash identifiers are therefore interlinked and ensure the security and immutability of data in a blockchain.
The process of verifying transactions utilizes this hashing mechanism. In this, the person who successfully hashes a block then mines it and receives the reward. The miner is repeatedly guessing to find the hashing value that produces the desired output hash required to mine a valid block in the chain.
#6) Crypto-economics And Blockchain Security
Crypto-economics uses the same ideologies as game theory where pre-defined rules and rewards mathematically determine the decisions to be made in different situations. In crypto-economics, the behavior of nodes on the blockchain is modeled by crypto-economics.
- The economic ideologies are encoded on the blockchain protocols including the behavior of participants and the possible outcomes of the behaviors.
- Crypto-economics encourage positive and honest behavior and rewards participants who engage in such behavior while discouraging malicious or faulty behavior.
An example is rewarding those who support the network by committing their computer processing power through mining rewards on Bitcoin. At the same time, dishonest or inefficient nodes are punished by being expelled from the network.
- The balancing of rewards through consensus algorithms and crypto-economics ensures further security of the network because many people are motivated to support and participate in the network positively. This wards off the possibility of more others committing hash rates into malicious activity to a single group or entity which could lead to 51% attacks. For instance, the competitiveness of the Bitcoin network minimizes the likelihood of malicious attacks.
- Crypto-economics, by ensuring a large amount of hash rate is committed to the network by so many people and ensures that insecurities such as 51% attack are hard and expensive if not impossible to carry out. For instance, in Bitcoin, it would be highly punitive in terms of cost to carry out such an attack for a very small potential reward.
Thus blockchains have the characteristic known as Byzantine Fault Tolerance (BFT). This defines the ability of the network to continue operating normally even when some nodes are compromised or act maliciously. This is like this as long as the incentive for honest behavior remains higher than that for malicious activity which would be set as prohibitive.
Smaller blockchain networks with small hash rates may, however, experience 51% attacks because the total hash rates are very small and it is affordable to commit a huge amount of hash rate to attack 51% of the nodes and control the network.
#7) Quantum Computers And Quantum-Resistant Blockchains
Using ultra-fast computer algorithms, it might be easier and faster to calculate, within seconds, the factors of a large number even if it has very large prime factors. This means that it would become possible to break blockchains secured with current cryptography algorithms. This is because it would become possible to unearth the cryptographic keys within seconds.
- To respond to this, debates and work have begun to emerge about blockchains that can counter this. Such a quantum-resistant blockchain would make it even harder for quantum computers to break the chains.
- Instead of employing current cryptographic algorithms that cannot withstand quantum computers, these blockchains would employ algorithms that can generate stronger keys that stand up to the challenge of quantum computers.
Conclusion
This tutorial considered the basics and working of cryptography, hashing, digital signatures, as well as consensus and crypto-economics in securing blockchains. We saw that while cryptography is the central method of securing blockchains, other techniques also play an important role in making blockchains secure.
We saw that digital signatures help maintain authenticity and confidentiality of transactions, even as cryptography through hashing and key encryptions ensures secrecy has a great role in blockchain security.
Suggested reading =>> Best Blockchain DNS Software
We saw that crypto-economics and decentralization encourage as many users to commit their resources to promote and maintain and in the continuity of the network rather than committing more efforts to destroy it.
<<PREV Tutorial | NEXT Tutorial>>