In-depth review and comparison of top Vulnerability Management tools to make it easy to select the Best Vulnerability Management Software from the list:
An unsecured network can be disastrous for any business, especially when data breach scenarios have become painfully common.
While there are tools like antivirus software out there, they are mainly reactive and only come into play after a considerable amount of damage has already been done. Businesses need to find a solution that allows them to stay one step ahead of imminent security threats.
This is where vulnerability management solutions have become so fundamental. Vulnerability Management tools are designed to find weaknesses in your company’s system to mitigate potential security breaches in the future.
Such tools can also tackle potential cybersecurity issues by assigning threat levels to all the vulnerabilities found in a system. As such, IT professionals can decide which threat to prioritize and which threat can wait before it is eventually addressed.

Table of Contents:
- Most Popular Vulnerability Management Tools
- List of the Best Vulnerability Management Software
- Vulnerability Management Software Comparison
- #1) NinjaOne Vulnerability Management & Mitigation
- #2) Astra Pentest
- #3) Indusface AppTrana
- #4) Invicti (formerly Netsparker)
- #5) Acunetix
- #6) ManageEngine Key Manager Plus
- #7) ManageEngine Vulnerability Manager Plus
- #8) ZeroNorth
- #9) ThreadFix
- #10) Infection Monkey
- #11) Tenable
- #12) Qualys Cloud Platform
- #13) Rapid7 InsightVM
- #14) TripWire IP360
- #15) GFI Languard
- #16) Hexway Vampy
- #17) SecPod
- #18) Intruder
- Frequently Asked Questions
- Conclusion
Most Popular Vulnerability Management Tools
Nowadays, we also have tools that can automatically start fixing vulnerabilities in the system. In this tutorial, we will be exploring 10 such tools that we believe are some of the best in the market.
So based on our hands-on experience with each of them, we would like to recommend the 10 best vulnerability management solutions that you can try to strengthen the security of websites, networks, and web applications.
Expert Advice
- Look for vulnerability management software that is reliable, easy to deploy, navigate and interpret. It should be able to detect threats in real-time without complications.
- Make sure that the software you choose is compatible with all prominent operating systems, infrastructure components and applications.
- Look for a tool that performs automated scans, clearly identifies vulnerabilities, and modifies security controls to automatically tackle all types of threats 24 hours a day, or 365 days a year.
- The software should clearly integrate with your current system.
- Look for a tool whose pricing or licensing fee is affordable and fits comfortably within your budget.
- Look for vendors that provide 24/7 customer support. There should be an immediate response from the concerned representatives to address your queries.
Market Trends
According to Statista, a total of 1001 cases of data breaches were reported in 2020. Although considerably less than 2019, the numbers are still alarmingly high. The same report also states that over 155.8 million individuals had their data exposed in the middle of a pandemic.

List of the Best Vulnerability Management Software
Here is the list of top Vulnerability Management Tools:
- NinjaOne Vulnerability Management & Mitigation
- Astra Pentest
- Indusface AppTrana
- Invicti (formerly Netsparker)
- Acunetix
- ManageEngine Key Manager Plus
- ManageEngine Vulnerability Manager Plus
- ZeroNorth
- ThreadFix
- Infection Monkey
- Tenable.sc & Tenable.io
- Qualys Cloud Platform
- Rapid7 InsightVM
- TripWire IP360
- GFI Languard
- Hexway Vampy
- SecPod
- Intruder
Vulnerability Management Software Comparison
| Name | Best For | Fees | Ratings |
|---|---|---|---|
| NinjaOne Vulnerability Management & Mitigation | Protecting the endpoints from ransomware. | Contact for quote | |
| Astra Pentest | Automated & Manual scans, Continuous scanning, Compliance Reporting. | $99 – $399 per month | |
| Indusface AppTrana | Virtual Patching | Starts at $99/app/month | |
| Invicti (formerly Netsparker) | Automated, Continuous, and Highly Scalable Application Security Testing | Contact for Quote | |
| Acunetix | Web Vulnerability Scanning to Secure Websites, Web Applications, and API’s | Contact for Quote | |
| ManageEngine Key Manager Plus | Proactively detecting vulnerable machine identity | Starts at $475 | |
| ManageEngine Vulnerability Manager Plus | Automated Patch Management | Free edition available, Quote-based Professional plan, Enterprise Plan starts at $1195/year. | |
| ZeroNorth | DevSecOps Orchestration and Integration | Contact for Quote | |
| ThreadFix | Comprehensive Vulnerability Management Reporting | Contact for Quote | |
| Infection Monkey | Open Source Threat Detection and Fixing | Free | |
| Intruder | Continuous vulnerability monitoring and proactive security. | Contact for a quote |
#1) NinjaOne Vulnerability Management & Mitigation
Best for protecting endpoints from ransomware.

NinjaOne automates the hardest parts of IT, delivering visibility, security, and control over all endpoints for more than 20,000 customers.
The NinjaOne automated endpoint management platform is proven to increase productivity, reduce security risk, and lower costs for IT teams and managed service providers. The company seamlessly integrates with a wide range of IT and security technologies. NinjaOne is obsessed with customer success and provides free and unlimited onboarding, training, and support.
NinjaOne is #1 on G2 in endpoint management, patch management, remote monitoring and management, and mobile device management.
Features:
- NinjaOne’s multi-platform endpoint management enables monitoring and management of the entire IT portfolio.
- It has features for OS and third-party application patch management and hence helps with reducing vulnerabilities.
- It supports Windows, Mac, and Linux platforms for automating patch management.
Verdict: NinjaOne provides a 360º view into all the endpoints. It can perform third-party patching for more than 135 applications. Application-related vulnerabilities will be minimized with the use of this tool. It facilitates centralized management of IT infrastructure. It is a network and domain agnostic. It is a fast, intuitive, and easy-to-manage solution.
Price: A free trial is available for NinjaOne. For this platform, pay monthly and only for what you need. You can get a quote for pricing details. As per reviews, the price of the platform is $3 per device per month.
#2) Astra Pentest
Best for Automated & Manual scans, Continuous scanning, and Compliance Reporting.
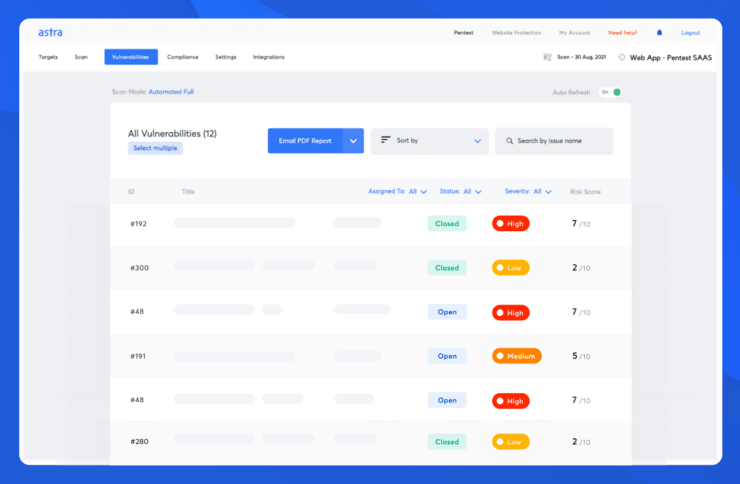
Astra’s Pentest makes vulnerability management super simple for users with features geared towards tackling specific pain points. Astra’s automated vulnerability scanner conducts 8000+ tests covering OWASP top 10 and SANS 25 CVEs. On top of that, it helps you conduct all vulnerability checks required for compliances like GDPR, ISO 27001, SOC2, and HIPAA.
Astra’s pentest engineer-friendly dashboard gives users the easiest possible way to monitor and manage vulnerabilities. The dashboard shows you the risk scores for each vulnerability based on the CVSS score, potential losses, and overall business impact. They also come up with suggestions for fixes. You can use the compliance reporting feature to view the compliance status of your organization according to the vulnerabilities found.
Astra vulnerability scanner packs the intelligence acquired from years of pentesting and is continuously updated with latest vulnerabilities. You can trust it to detect the latest vulnerabilities almost as soon as they gain public visibility.
Features:
- 8000+ tests covering ISO 27001, SOC2, HIPAA, & GDPR requirements
- Developer-friendly dashboard & reporting
- Automated scan to continuously scan for vulnerabilities
- Continuous automated scanning & schedule scan feature
- Visibility of compliance status
- Scanning single-page apps and progressive web apps
- CI/CD integration for scanning product releases
- Vulnerability analysis with risk scores, and suggested fixes.
Verdict: When it comes to the features included in the vulnerability scanner, Astra’s Pentest is a formidable contender with all relevant features you can think of, be it scanning behind the login screen, or continuous scanning. When it comes to remediation support and expert guidance from security engineers, Astra’s offerings are quite unmatched.
Price: Web app vulnerability assessment using Astra’s Pentest starts at $199 per month. You can get a tailored quote for your needs and the frequency of the pentest required.
#3) Indusface AppTrana
Best for Virtual Patching.
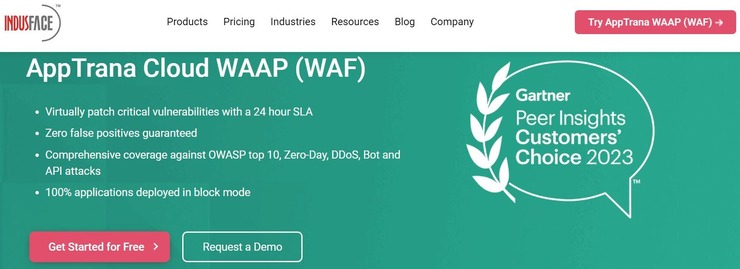
Indusface AppTrana is an effective vulnerability management tool that allows you to virtually patch critical vulnerabilities within 24 hours. The tool lets you leverage virtual patching with 24-hour SLAs for serious vulnerabilities like Log4J.
The software is also great at mitigating Bot and DDoS attacks, thus ensuring your applications are functional round-the-clock. The tool is also very good at detecting vulnerabilities inside an API. It does so via an automated scanner and efficient penetration testing.
Features:
- Virtual Patching
- DDoS and Bot Mitigation
- API Vulnerability Scanning
- 24/7 Expert Support
- Pen Testing
Verdict: If you are looking for a tool that virtually patches critical vulnerabilities in the span of a day, then this tool is for you. The software provides you with comprehensive coverage against all sorts of attacks, which include OWASP Top 10, Zero Day Vulnerabilities, Bot attacks, and more.
Price: AppTrana’s plans start at $99/app/month. Its premium plan will cost you $399/app/month. A custom enterprise plan is also offered.
#4) Invicti (formerly Netsparker)
Best for Automated, Continuous, and Highly Scalable Application Security Testing.

Invicti is an automated and highly scalable vulnerability management solution that scans web applications and services to detect potential flaws in their security. This is a software that can scan all types of applications, regardless of the language or platform they were built with.
Moreover, Invicti combines DAST and IAST scanning to detect all kinds of vulnerabilities. It’s unique combination of signature-based and behavior-based testing gives you accurate results in no time.
The visually dynamic dashboard is where Invicti truly shines. The dashboard gives you a holistic picture of all your websites, scans, and detected vulnerabilities on a single screen.
The tool empowers its users with comprehensive graphs that allow security teams to assess the severity of threats and categorize them accordingly based on their threat level, i.e. low or critical.
The dashboard can also assign particular security tasks to team members and manage permissions for multiple users. The tool can also automatically create and assign detected vulnerabilities to developers. It also makes fixing these vulnerabilities easy by providing developers with detailed documentation on the detected weakness.
Invicti’s ‘Proof Based Scanning’ feature can automatically detect vulnerabilities and exploit them in a safe, read-only environment to determine whether they are false positives or not. With false positives reduced dramatically, the software expertly eliminates the need for manual verification.
Furthermore, Invicti can be seamlessly integrated with your existing issue trackers, CI/CD platforms, and vulnerability management systems.
Features
- Combined DAST + IAST Scanning.
- Proof Based Scanning
- Detailed Documentation on Detected Vulnerabilities.
- Assign security tasks to teams and manage permissions for multiple users.
- Continuous 24/7 security.
Verdict: Invicti is a fully configurable, automated, and highly scalable solution that can detect vulnerabilities and suggest actionable insights to strengthen your system’s security. Its advanced crawling feature scans every corner of an application to detect weaknesses that other similar tools may miss.
Invicti is also extremely beneficial for developers as it provides detailed reports to effectively resolve vulnerabilities and prevent their recurring occurrence.
Price: Contact for a quote.
#5) Acunetix
Best for Web Vulnerability Scanning for Secure Websites, Web Applications and API’s.

Acunetix is an intuitive application security testing solution that can be deployed to scan and secure all types of websites, APIs, and web applications. The solution’s ‘Advanced Macro Recording’ feature allows it to scan password-protected areas of a site and sophisticated multi-level forms.
It is known to detect over 7000 vulnerabilities. These include exposed databases, SQL injections, weak passwords, XSS, and more. It can scan your system at an incredible speed, thereby finding vulnerabilities quickly without overloading the server.
Acunetix also reduces the rate of false positives as it verifies the detected vulnerability before reporting it as a subject of concern. Thanks to advanced automation, Acunetix allows you to schedule a scan ahead of time as per your business requirements or traffic load.
The solution integrates seamlessly with the current tracking system you’ve been using, such as Jira, Bugzilla, Mantis, or other such systems.
Features:
- Initiate Scan at the Scheduled Time and Interval Automatically.
- Detect Over 7000 vulnerabilities.
- Integrate seamlessly with the current systems being used.
- Advanced Macro Recording
- Reduces False Positives with Intuitive Vulnerability Verification.
Verdict: Acunetix is a powerful application security system that is easy to deploy and use. You can get started with this solution with just a few clicks. Moreover, the app can scan all types of complex web pages, applications, and API’s to detect and suggest remediation actions for more than 7000 vulnerabilities.
It also possesses top-notch automation, thereby allowing you to initiate prioritized scans automatically at a scheduled time. Acunetix has our highest recommendation.
Price: Contact for a quote.
#6) ManageEngine Key Manager Plus
Best for Proactively detecting vulnerable machine identity.
ManageEngine’s Key Manager Plus can help you identify vulnerabilities in relation to weak or expired certificates. The platform’s primary purpose is to help enterprises manage SSH keys and SSL/TLS certificates. It automates their lifecycle management. For instance, you can use it to discover, consolidate, create, and associate SSH keys within your network.
Once deployed, Key Manager Plus proactively scans for vulnerabilities like the Heartbleed bug or the POODLE SSL. These are examples of vulnerabilities that can cause some serious damage to critical certificates and business operations.
Key Manager Plus identifies and discovers a misconfigured certificate or one that’s about to expire. It also automatically renews it.
Features:
- Automated certificate discovery
- SSL, TLS, and SSH key lifecycle management
- Strong auditing system
- Centralized access control
- Disaster Recovery
Verdict: ManageEngine’s Key Manager Plus isn’t your typical general-purpose vulnerability management solution. ManageEngine already has a tool for that in the form of Vulnerability Manager Plus. What you do get with this platform is that it can help your enterprise eliminate security gaps by automating SSH keys and SSL/TLS certificate management.
Price: License fee for ManageEngine Key Manager Plus starts at $475. A 30-day free trial and a free demo are also offered. You can contact ManageEngine’s team to get a custom quote tailored to your organization’s requirements.
#7) ManageEngine Vulnerability Manager Plus
Best for Automated Patch Management.

ManageEngine Vulnerability Manager Plus is a powerful vulnerability management and compliance tool in one solution. The software can scan and assess vulnerabilities that are affecting the OSs, applications, systems, and servers on your network.
Once detected, Vulnerability Manager Plus proactively prioritizes them based on their severity, age, and exploitability. The software comes with impressive built-in remediation capabilities, which makes it excellent at dealing with all forms of threats. It can customize, orchestrate, and automate the entire patching process.
Features:
- Continuous Vulnerability Assessment
- Automated Patch Management
- Zero-day vulnerability Mitigation
- Security Configuration Management
Verdict: Vulnerability Manager Plus offers rigorous network monitoring, attacker-based analytics, and superior automation… all in a bid to keep your IT infrastructure safe from security breaches.
Price: There is a free edition available. You can contact the ManageEngine team to request a quote for the professional plan. The enterprise edition starts at $1195 per year.
#8) ZeroNorth
Best for DevSecOps Orchestration and Integration.

ZeroNorth offers a comprehensive suite of scanning tools that aid in finding, fixing, and preventing vulnerabilities threatening the security of your system’s applications.
It presents a visual dashboard that hosts analytics and reports pertaining to potential vulnerabilities risking your app’s security. You can undertake consistent, repetitive scanning with ZeroNorth to detect app security risks without changing the existing workflows.
Furthermore, this solution also simplifies remediating app security risks by aggregating, de-duplicating, and compressing AppSec risks at a ratio of 90:1. ZeroNorth integrates seamlessly with most commercial and open source AppSec tools being used today.
Features:
- Visual Dashboard with Comprehensive Analytics and Reports.
- Simplified AppSec remediation
- Consistent and Repetitive Scanning.
- Seamlessly Integrate with many Prominent Commercial and Open Source AppSec tools.
Verdict: ZeroNorth is an easy-to-use solution that offers a wide range of tools that aid in the continuous scanning of multiple business-critical applications. As such, it is capable of accurately detecting and preventing security risks before they can affect the application.
Its visual dashboard with comprehensive analytics and reporting is easily ZeroNorth’s highlighting feature.
Price: Contact for a quote.
Also Read => Top External Vulnerability Scanner Tools
#9) ThreadFix
Best for Comprehensive Vulnerability Management Reporting.

ThreadFix is a great vulnerability management software that exhibits its efficiency with the comprehensive set of reports it provides to help developers better understand and manage vulnerabilities. ThreadFix can detect vulnerability trends and immediately suggest remediation actions to prevent these risks from aggravating.
The solution integrates with other open-source and commercial app scanning tools to automatically consolidate, correlate, and de-duplicate vulnerabilities found in an application. ThreadFix also allows you to easily assign vulnerabilities to the right developers and security teams to patch them faster.
Features:
- Comprehensive Reporting and Analytics.
- Consolidate Test Results
- Integrate seamlessly with the most open-source and commercial app security tools.
- Assign detected vulnerabilities to developers or security operations teams to manage them efficiently.
Verdict: ThreadFix offers a seamless vulnerability management experience, thanks to the comprehensive reports and analytics it provides on the detected security risks. The report allows developers or security teams to quickly identify the vulnerability and make smart remediation decisions to prevent it from causing harm to the system.
Price: Contact for a quote.
Website: https://threadfix.it/
Further Reading => Explore the TOP SBOM Solutions of the Year
#10) Infection Monkey
Best for Open Source Threat Detection and Fixing.

Infection Monkey sets itself apart from the other tools on this tool by being an open-source platform. The solution can be used for free to perform breach and attack simulations to detect and fix potential security risks. Infection Monkey provides its users with 3 analysis reports with actionable insights to deal with security threats to your network.
First, the solution simulates a breach on a machine you choose to deploy it in. It evaluates the system and detects risks that can cause potential harm to your network. Finally, it suggests remediation advice, which can be followed to fix these issues before they aggravate.
Features:
- Open Source Breach and Attack Simulation.
- Test Network Adherence to ZTX.
- Detect weaknesses in cloud-based and on-premise data centers.
- Comprehensive reports and analytics.
Verdict: Infection Monkey is a smart open-source solution to find and fix potential vulnerabilities in your system in just 3 simple steps. The software simulates an APT attack with real-life attack tactics to conjure suggestions that can competently remediate vulnerabilities in no time.
Price: Free
Website: https://www.guardicore.com/infectionmonkey/
#11) Tenable
Best for Machine Learning Powered Security Risk Prediction.

Tenable takes a risk-based vulnerability management approach to detect and resolve weaknesses found across your system’s network, site, and web applications. It presents a holistic snapshot of your system’s entire infrastructure, covering every corner to detect even the rarest variants of vulnerabilities without fail.
The solution expertly leverages threat intelligence to predict which vulnerabilities pose a severe threat to your system’s security. Furthermore, the solution arms developers and security teams with key metrics and actionable insights to mitigate critical risks.
Features:
- Leverage Threat Intelligence to Identify and categorize weaknesses based on their severity.
- Provide comprehensive reports to act on identified security risks quickly.
- Continuous scanning and assessment of cloud assets.
- Advanced Automation
Verdict: Tenable allows you to monitor activities across your entire attack surface to find, predict and address potentially harmful risks.
Its advanced automation allows you to prioritize vulnerabilities that have a higher chance of being exploited by attackers. It possesses threat intelligence, which makes identifying a threat’s severity level easy.
Price: Subscription starts at $2275 per year to provide protection to 65 assets.
Website: https://www.tenable.com/
#12) Qualys Cloud Platform
Best for Monitoring All IT Assets in Real-Time.

Qualys Cloud Platform allows you to continuously monitor all your IT assets from a single visually impressive dashboard. The solution automatically gathers and analyzes data from all types of IT assets to proactively detect vulnerabilities in them.
With Qualys Cloud Platform’s continuous monitoring service, users can proactively address threats before they cause serious damage.
Users are immediately notified of threats as soon as they are detected in real-time, thereby affording enough time to address them before it’s too late. You get a complete, updated, and continuous view of your IT assets from a single dashboard.
Features:
- Real-Time Data Analyzes
- Monitor IT assets from a single comprehensive dashboard.
- Proactively address threats with real-time notifications.
- Continuous assessment of IT assets to find vulnerabilities at all times.
Verdict: Qualys Cloud Platform is a powerful end-to-end solution to continuously monitor IT assets for vulnerabilities, regardless of whether they are deployed at the endpoint, in cloud, or on-premise.
Its dashboard provides accurate information on all your IT assets, so you can identify threats before it’s too late. The solution also provides you with appropriate remediation suggestions to proactively address security threats.
Price: Contact for a quote.
Website: https://www.qualys.com/cloud-platform/
Suggested Read => Most Popular IT Asset Management Software
#13) Rapid7 InsightVM
Best for Automatic Risk Assessment.

Rapid7’s Insight Vulnerability Management platform is known to automatically detect and assess weaknesses across an entire infrastructure. This is a lightweight endpoint agent that prioritizes the remediation of real risks by verifying the vulnerabilities it detects before reporting them.
However, it is in its comprehensive reporting that Rapid7 truly shines. It presents users with live dashboards that contain data collected on vulnerabilities in real-time. This data can make appropriate remediation decisions to address risks before they have a chance of affecting the system.
The software is particularly impressive because of its advanced automation. The solution can automate the steps in gathering key data on vulnerabilities, getting fixes for detected weaknesses, and applying patches as and when approved by a system admin.
Features:
- Real Risk Prioritization
- Cloud and Virtual Infrastructure Assessment.
- Automation Assisted Fixing
- Easy to Use RESTful API.
Verdict: Rapid7 InsightVM competently monitors your entire cloud and virtual infrastructure to detect all types of security threats. Moreover, it allows you to proactively take care of these vulnerabilities with automation-assisted patching. Rapid7 has a live dashboard with an easy-to-navigate interface.
Price: Pricing starts at $1.84/month per asset for the protection of 500 assets.
Website: https://www.rapid7.com/products/insightvm/
#14) TripWire IP360
Best for Scalable and Flexible Vulnerable Management.

TripWire is a vulnerability management solution that lets you monitor all assets on your network on-premises, container, and cloud. It is extremely flexible and can be scaled to meet the needs of your largest deployment. The software can also detect previously undetected assets as well with the help of agentless and agent-based scans.
TripWire not only finds vulnerabilities but also ranks them according to their severity level to prioritize which threats to address quickly. It seamlessly integrates with your system’s existing asset-management software to detect and fix breaches proactively.
Features:
- Full Network Visibility
- Prioritized Risk Scoring
- Seamlessly Integrate with Existing Programs and Apps.
- Detect assets accurately with agentless and agent-based scanning.
Verdict: TripWire is a flexible and highly scalable vulnerability management solution that accurately identifies all assets in your entire network. This makes the software efficient in finding vulnerabilities and scoring them to prioritize remediation efforts.
Price: Contact for quote.
Website: https://www.tripwire.com/products/tripwire-ip360
#15) GFI Languard
Best for Automatically Fixing Security Gaps.

GFI Languard is quite effective when it comes to protecting your network and applications from potential vulnerabilities. It automatically discovers all assets on your network and monitors them proactively to detect issues.
Not only can GFI Languard help you find security gaps, but you can also scan the network to find missing patches to fix these gaps. The software can automatically deploy patches centrally to address vulnerabilities.
Alternatively, you can assign teams and agents to a particular identified vulnerability to better manage them. Apart from finding patches, the software also helps you find bug fixes that can help apps run smoother.
Features:
- Automatically Discover Assets across your entire network.
- Find security gaps and non-patch vulnerabilities.
- Assign vulnerabilities to security teams for management.
- Search for patches and deploy relevant patches automatically.
Verdict: GFI Languard provides users with a decent solution that can automatically detect and fix potential risks on your network and applications. This is a solution that is constantly updated to provide users with the most relevant patches to address vulnerabilities detected in a system.
Price: Contact for a quote
Website: https://www.gfi.com/products-and-solutions/network-security-solutions/gfi-languard
#16) Hexway Vampy
Best for Application Security Testing, CI/CD automation, DevSecOps orchestration, and Security data normalization.

Hexway Vampy is an easy-to-use platform that maximizes the efficiency of vulnerability management and easily integrates into SDLC.
Vampy aggregates security data from different sources (like SAST, DAST, Security scanners, bug bounty programs, pentest reports & more) to provide users with the advanced toolsets to work with this huge amount of data.
Vampy has internal parsers and stable data correlation engines to work with deduplication, see the big picture in customizable dashboards, and create Jira tasks for developers.
One of the main Vampy benefits is that it simplifies traditional complicated workflows to save teams some time and help them release safer products in less time.
Features:
- Smart dashboards
- Risk scoring and prioritization
- Collaborative tools
- CI/CD Automation
- Data centralization
- Support manager
- Actionable risk insights
- Asset management
- SDLC-ready
- Vulnerability Deduplication
- Jira integration
Price: Contact for a quote
#17) SecPod
Best for SMEs, enterprises and MSPs, continuous and most accurate detection and remediation of vulnerabilities.

SecPod detects vulnerabilities beyond CVEs. These vulns include misconfigurations, missing patches, security posture anomalies etc. The tool patches them instantly.
SecPod performs the entire cycle with a continuous vulnerability and exposure management (CVEM) framework. It integrates vulnerability and patch management into a unified console.
Features:
- 175,000+ checks powered by natively built the world’s largest vulnerability database
- Fastest vulnerability scanning with 5-minute scans
- Supports all OS versions such as Windows, LINUX, macOS and AIX
- Patching 450+ third-party applications
- Zero-day checks are readily available
- Get high-fidelity attack metrics
- In a single console perform a complete vulnerability management cycle
- Industry’s best accurate scanning
- Automated tasks from scanning to remediation
- Risk prioritization based on severity and business context
Verdict: SecPod is a complete vulnerability and patch management solution that streamlines and automates your vulnerability management process. In addition, it can replace multiple solutions, improving the efficiency and safety of your organization.
Price: Contact for a quote
#18) Intruder
Best for continuous vulnerability monitoring and proactive security.

Intruder provides the same high level of security enjoyed by banks and government agencies with some of the leading scanning engines under the hood. Trusted by over 2,000 companies worldwide, it has been designed with speed, versatility, and simplicity in mind, to make reporting, remediation, and compliance as easy as possible.
You can automatically synchronize with your cloud environments and get proactive alerts when exposed ports and services change across your estate, helping you secure your evolving IT environment.
By interpreting the raw data drawn from leading scanning engines, Intruder returns intelligent reports that are easy to interpret, prioritize, and action. Each vulnerability is prioritized by context for a holistic view of all vulnerabilities, saving time and reducing the customer’s attack surface.
Features:
- Robust security checks for your critical systems
- Rapid response to emerging threats
- Continuous monitoring of your external perimeter
- Perfect visibility of your cloud systems
Verdict: Intruder’s mission from day one has been to help divide the needles from the haystack, focusing on what matters, ignoring the rest, and getting the basics right. Powered by one of the industry’s leading scanning engine, but without the complexity, it saves you time on the easy stuff, so you can focus on the rest.
Price: Free 14-day trial for Pro plan, contact for price, monthly or annual billing available
Frequently Asked Questions
What does a Vulnerability Management Software Do?
A vulnerability management solution helps to monitor a system’s security in real-time, detects breaches, and takes necessary actions to remediate the threat before it has the opportunity to cause harm to the system or application.
These solutions assist organizations in prioritizing the management of possible security threats to their system infrastructure.
How are Vulnerability Management Software Different from Anti-Virus software or similar tools?
Anti-Virus software and Firewalls are reactive. They manage threats as they occur. This is not the case with Vulnerability Management Solutions. Unlike their counterparts, these tools are proactive in nature.
They monitor the system for potential threats by scanning and detecting vulnerabilities in the network. These threats can be prevented by the remediation suggestions provided by the Vulnerability Management software.
What are DAST Tools?
A DAST tool, also known as dynamic analysis security testing tool, is a kind of application security software that can find vulnerabilities in a web application while it is still running. A DAST test can help identify errors or configuration mistakes while also detecting other significant problems plaguing an application.
DAST usually works when automated scans are implemented to stimulate external threats on an application. It does so to detect outcomes that aren’t part of an expected set of results.
Define the Threat Modeling Process.
Threat Modeling is a process with which vulnerabilities are identified to optimize the security of a business’s system and applications. Appropriate counter measures are then developed to mitigate the threats that were identified during the procedure.
Which is the Best Vulnerability Management Tool?
Based on popular opinion and our own experience, we believe the following 5 to be the best Vulnerability Management Software available today.
Invicti (formerly Netsparker)
Acunetix
ZeroNorth
ThreadFix
Infection Monkey
Conclusion
In a world where information is heavily digitalized and often in transit across multiple networks, it is wise to adopt proactive security measures to prevent security breaches. After all, a security breach can cost massive losses to a business.
It is necessary to strengthen the security of your site, application, and network to avoid malicious attacks that happen regularly. This is why a vulnerability management solution is so important.
These solutions can help developers and security teams achieve a clear understanding of the threats they face and suggest appropriate remediation insights to fix them. All the above-mentioned tools accomplish this with impeccable finesse.
We recommend that if you seek a fully automated and highly scalable vulnerability management software that accurately detects a wide variety of vulnerabilities, then look no further than Invicti and Acunetix. For an open-source solution, you can try Infection Monkey.
Research Process
- Time Taken To Research And Write This Article: 12 Hours
- Total Vulnerability Management Tools Researched: 20
- Total Vulnerability Management Tools Shortlisted: 10










