List and comparison of the best Vulnerability Scanners available and why use them:
Attackers are always prowling in dark corners of the internet for vulnerabilities that would allow them to wreak havoc on an unsuspecting individual or business.
A small chink in the armor is all they need to gain unauthorized access to critical data. Hence, it is imperative to detect these “vulnerabilities” in an application or website before the attackers do.
OWASP defines vulnerability as a weakness in the application… a sort of design flaw or implementation bug that provides attackers with the opportunity to harm stakeholders of an application. As such, vulnerability scanning has become the most essential IT security practice in recent years.
Table of Contents:
- Most Popular Vulnerability Scanners
- List of the Best Vulnerability Scanners
- Comparing the Best Vulnerability Scanning Tools
- #1) Astra Security
- #2) Blacksight
- #3) Paessler PRTG
- #4) Indusface WAS
- #5) Invicti (formerly Netsparker)
- #6) Acunetix
- #7) Burp Suite
- #8) Nikto2
- #9) GFI Languard
- #10) OpenVAS
- #11) Tenable Nessus
- #12) ManageEngine Vulnerability Management Plus
- #13) Frontline VM
- #14) SecPod SanerNow
- #15) Intruder
- Other Vulnerability Scanners
- Frequently Asked Questions
- Conclusion
Most Popular Vulnerability Scanners

Vulnerability Scanners use a constantly updating list of databases to detect and classify weaknesses to prioritize their fixes. Some vulnerability scanners even go so far as to automatically patch the vulnerability, thereby alleviating the burden on security teams and developers.
In this tutorial, we will be looking at tools that we would argue are some of the best vulnerability scanners available today. We will be looking at the features they offer and explore whether they are easy to use, and will ultimately let you decide which of these tools would best suit your needs.
Expert Advice:
- The vulnerability scanner should be easy to deploy and run. A visual dashboard that clearly conveys the location, nature, and severity of a detected threat is a must.
- The scanner must be adequately automated. It must run continuously and alert you to detected vulnerabilities in real-time.
- It should verify a detected vulnerability to eliminate false positives. Reduced false positives are crucial to prevent wastage of time.
- The scanner must be capable of reporting its findings with comprehensive analysis. Visual graphs are a huge plus.
- Look for vendors that offer 24/7 support.
- Go for a solution that is reasonably priced and covers your needs without exceeding your budget.

Our TOP Recommendations:
 |  |  |  |
| Astra Security | Paessler PRTG | Invicti (formerly Netsparker) | Acunetix |
| • Continuous Testing • Remediation Guidance • AI Threat Modeling | • Port Monitoring • Visual Maps • Packet Sniffing Sensor | • Web Crawling • IAST+DAST • Proof-based Scanning | • Macro Recording • Schedule Scan • Vulnerability Scanning |
| Price: Starts at $199/month Trial version: Demo Available | Price: Quote-Based Trial version: Available | Price: Quote-based Trial version: Free Demo | Price: Quote-based Trial version: Free Demo |
| Visit Site >> | Visit Site >> | Visit Site >> | Visit Site >> |
List of the Best Vulnerability Scanners
Here is a list of popular free and commercial Vulnerability Scanners:
- Astra Security
- Blacksight
- Paessler PRTG
- Indusface WAS
- Invicti (formerly Netsparker)
- Acunetix
- Burp Suite
- Nikto2
- GFI Languard
- OpenVAS
- Tenable Nessus
- ManageEngine Vulnerability Manager Plus
- Frontline VM
- SecPod SanerNow
- Intruder
Comparing the Best Vulnerability Scanning Tools
| Name | Best For | Fees | Ratings |
|---|---|---|---|
| Astra Security | Web Application Vulnerability Scanner & Pentest | $99 – $399 per month | |
| Blacksight | 17 different security scanners in one platform. The platform will let you know everything about website’s security. | Start at $29/month, free forever with limited capabilities. | |
| Paessler PRTG | Full network monitoring | Starts at $179/month (Billed Annually) | |
| Indusface WAS | A complete scanning solution. | Basic plan is free, Advanced: $49/app/month, Premium: $199/app/month. | |
| Invicti (formerly Netsparker) | Automated Web Security Scanning | Contact for Quote | |
| Acunetix | Intuitive Web Application Security Scanner | Contact for Quote | |
| Burp Suite | Automated Web Vulnerability Scanning | Contact for Quote | |
| Nikto2 | Open Source Web Scanner | Free | |
| GFI Languard | Built-In Patch Management | Contact for Quote | |
| Intruder | Continuous vulnerability scanning and attack surface reduction. | Contact for Quote |
#1) Astra Security
Best for Web Application Vulnerability Scanner & Pentest.
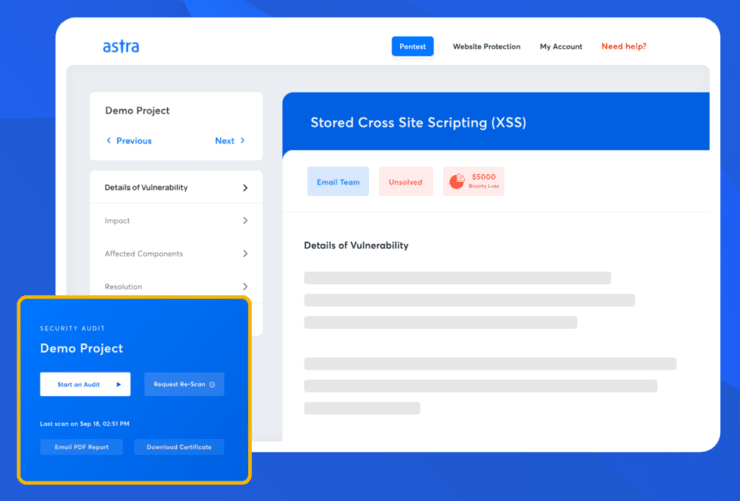
Astra’s vulnerability scanner conducts all the tests required to meet compliance with ISO 27001, GDPR, SOC2, and HIPAA. One unique feature that sets Astra apart is its ability to view the application from hacker’s eyes & perform a vulnerability scan just like a hacker would.
You can integrate the vulnerability scanner with your tech stack with the CI/CD integration feature. It makes turning your DevOps into DevSecOps simple. It also means you do not have to return to the pentest dashboard to start a scan, you can automate continuous scanning for code updates.
Features:
- 8000+ tests covering CVEs including but not limited to OWASP top 10 and SANS 25Compliance based scan for ISO 27001, SOC2, GDPR, and HIPAA
- Scan behind login pages
- CI/CD integration for continuous automated testing
- PWA and SPA scanning
- Risk scores to help you prioritize the fixes
- AI-powered business logic test case generation to ensure deep security testing coverage
- AI-powered conversational chatbot to give engineers contextual insights on fixing vulnerabilities
Verdict: With 8000+ tests, continuous testing, compliance reporting, and detailed remediation guidelines, the vulnerability scanner by Astra Pentest is as good as it gets. Integration features to tackle the challenges of imbibing security into the SDLC perfectly. For that, it is a choice that is hard to beat.
Price: The cost of vulnerability scanning with Astra Pentest starts at $199 per month. You can also request a quote for a one-time scan.
#2) Blacksight
Best for 17 different security scanners in one platform. The platform will let you know everything about website’s securityrability scanning.
Blacksight stands apart from many of its contemporaries on this list because of its user-friendliness. The platform can be used for free to instantly scan your main website. It features a scanner that is highly customizable. You can configure the scanner to perform recurring scans. You can also expand the coverage of your scanner by incorporating additional subdomains into your targets.
Once the scan is complete, you are provided with a comprehensive report that entails the tips you can use to address a detected issue. You are provided with accurate insights and analytical data that grant you more clarity on the security risks plaguing your website.
Features
- Set recurring scans for 24/7 protection.
- Comprehensive reporting with data-driven insight and analytics
- Invite collaborators for assistance with risk mitigation.
- Perform instant scans for quick website checks.
- Scan SOAP, OpenAPI, and GraphQL APIs with the Pro plan.
- 17 different security scanners with uptime monitoring etc.
Verdict: If you are looking for an online vulnerability scanner that is free, simple to use, and effective in abilities to detect threats, then you’ll adore what Blacksight has to offer.
Price: Blacksight’s scanner is free to use. Its premium plans with extended capabilities are as follows:
- Light: $9/month
- Plus: $29/month
- Pro: $89/month
- Custom Enterprise plan
Free plan available, paid plans start at $9/month. Coupon for 1 month free: SOFTH
#3) Paessler PRTG
Best for Full Network Monitoring.

Paessler PRTG continuously monitors every IT asset in your network to ensure they aren’t harboring a potentially dangerous vulnerability. This fully-integrated scanner is easy to deploy and provides full coverage of your network’s entire portfolio.
PRTG uses Windows Update Sensor to tell you whether a particular Windows update is needed. It also detects anomalies when there is unusual traffic with the help of Packer Sniffing Sensors. PRTG also identifies open and closed ports to prevent invasions like Trojan attacks.
Features
- Packet Sniffing Sensor
- Windows Update Sensor
- Port Monitoring
- Visual maps and dashboard
Verdict: Paessler PRTG allows you to continuously monitor everything on your network 24 hours a day and 365 days a year. As such, it instantly detects and alerts you when an irregularity is found. It comes fully integrated, so it works just fine and doesn’t require any additional plug-ins for enhanced performance.
Price: Contact for a quote.
#4) Indusface WAS
Best for a complete vulnerability assessment with application audit (web, mobile, and API), infrastructure scan, penetration testing, and malware monitoring.

Indusface WAS helps in vulnerability testing for web, mobile, and API applications. The scanner is a powerful combination of application, Infrastructure, and Malware scanner. The 24/7 support helps development teams with detailed remediation guidance and removal of false positives.
The solution is efficient with the detection of common application vulnerabilities that are validated by OWASP and WASC. It can immediately detect vulnerabilities that occur because of application changes & updates.
Features:
- Zero false positive guarantee with unlimited manual validation of vulnerabilities found in the DAST scan report.
- 24/7 support to discuss remediation guidelines and proofs of vulnerabilities.
- Penetration testing for web, mobile, and API apps.
- Free trial with a comprehensive single scan and no credit card required.
- Integration with Indusface AppTrana WAF to provide instant virtual patching with a zero false positive guarantee.
- Graybox scanning support with the ability to add credentials and then perform scans.
- Single dashboard for DAST scan and pen testing reports.
- Ability to automatically expand crawl coverage based on actual traffic data from the WAF system (in case AppTrana WAF is subscribed and used).
- Check for Malware infection, the reputation of the links in the website, defacement, and broken links.
Verdict: Indusface WAS solution provides comprehensive scanning and you can remain assured that none of the OWASP Top10, business logic vulnerabilities & malware will go unnoticed. It provides deep and intelligent web application scanning.
Price: Indusface WAS has three pricing plans, Premium ($199 per app per month), Advance ($49 per app per month), and Basic (Free forever). All these prices are for annual billing. The free trial is available with the Advance plan.
#5) Invicti (formerly Netsparker)
Best for Automated Web Security Scanning.

When it comes to scanning websites for vulnerabilities, Invicti is one of the finest vulnerability scanners you can deploy. The software leverages an advanced crawling feature to scan every corner of your web assets without fail. It can scan all types of web applications, regardless of the language or program, they were built with.
Invicti’s combined dynamic and interactive (DAST+IAST) approach to scanning allows it to detect vulnerabilities faster and more accurately.
Moreover, the platform verifies all detected vulnerabilities in an open, read-only manner, thereby eliminating false positives. The tool makes managing vulnerabilities simpler because of its visual dashboard.
The dashboard can be used to manage user permissions or assign vulnerabilities to specific security teams. Furthermore, Invicti is capable of automatically creating and assigning confirmed vulnerabilities to developers as well. The platform also provides you with detailed documentation on detected vulnerabilities.
The reports generated allow you to pinpoint the location of the vulnerability and remediate it as quickly as possible. Invicti also integrates seamlessly with other third-party tools like Okta, Jira, GitLab, and more.
Features
- Combined DAST+ IAST Scanning.
- Advanced Web Crawling
- Proof Scanning to detect false positives.
- Detailed documentation on detected vulnerability.
- Manage user permissions and assign vulnerabilities to security teams.
Verdict: Invicti is easy to use and works well as a website vulnerability scanner. You don’t need to be proficient in source code to operate this tool.
Its automated web security scanning features can be easily integrated with third-party tools. Invicti will help you detect vulnerabilities accurately in no time, and even provide you with actionable insights to handle them effectively.
Price: Contact for a quote.
#6) Acunetix
Best for Intuitive Web Application Security Scanner.

Acunetix utilizes interactive application security testing to accurately detect all types of vulnerabilities in no time. The platform is capable of detecting over 7000 different types of vulnerabilities that can be found on a website, application, or API. It is extremely easy to deploy as you don’t need to waste time on lengthy setups.
Its “Advanced Macro Recording” feature allows Acunetix to scan complex multi-level forms and password-protected pages of a site. It ensures to verification of the detected vulnerability to avoid reporting false positives.
Moreover, Acunetix classifies detected vulnerabilities based on their threat level. As such, security teams can prioritize their repose to vulnerabilities that pose a significantly greater threat.
Acunetix also allows you to schedule your scans to initiate automatic scanning at a specified date and time. Alternatively, you can allow Acunetix to continuously scan your system to alert you about detected vulnerabilities in real-time.
The platform can generate intuitive regulatory and technical reports that reveal how to remediate the vulnerability.
Features
- Advanced Macro Recording
- Schedule and Prioritize Scan
- Integrate seamlessly with other tracking systems.
- Generate comprehensive reports on detected vulnerabilities.
Verdict: Acunetix comes with a current version that is capable of performing continuous, automated scans that detect over 7000 different vulnerabilities. Its utilization of interactive application security testing makes it as one of the fastest and most accurate vulnerability scanners we have today.
Price: Contact for quote.
#7) Burp Suite
Best for Automated Web Vulnerability Scanning.

Burp Suite is a fully automated web vulnerability scanner that can accurately detect and alert you about vulnerabilities in your web application. It performs continuous, automated scans as soon as it is deployed to detect and report weaknesses before an attacker can find them.
The platform assigns threat levels to all the vulnerabilities it detects so you can prioritize threats that exhibit an urgent threat to your system. It also allows you to schedule your scans at a specified date and time to begin full-scale vulnerability scans automatically. Burp Suite’s current version integrates well with multiple CI/CD tracking systems.
Features
- Automated and Continuous Scanning
- Assign threat levels to detect vulnerability.
- Schedule scans at a specified date and time.
- Integrate seamlessly with third-party tracking systems.
Verdict: Burp Suite’s integration with other powerful tracking systems and its ability to generate detailed reports allows it to accurately detect and remediate vulnerabilities quicker than most. The platform will satisfy those who wish to constantly monitor their web applications for vulnerabilities.
Price: Contact for a quote.
Website: https://portswigger.net/burp
#8) Nikto2
Best for Open Source Security Scanning.

Nikto2 is an open-source vulnerability scanner that provides you with all the tools you need to perform scans with the sole purpose of detecting vulnerabilities. The platform verifies detected vulnerabilities to report confirmed threats only.
As of today, Nikto2 can test your network to identify over 125 outdated servers, 6700 potentially dangerous files, and version-specific problems on 270 servers. Nikto2 is also very good with the reports it generates. These are adequately detailed and present actionable insights on how you can remediate a found vulnerability.
Features
- SSL and Full HTTP Proxy Support.
- Generate reports on detected vulnerabilities.
- Verify vulnerability to detect false positives.
- Open Source and Free
Verdict: Nikto2 is a free-to-use, open-source vulnerability scanner that can detect a plethora of vulnerabilities quickly and accurately. It requires minimal to no manual intervention as Nikto2 intuitively verifies a vulnerability to report confirmed vulnerabilities, thereby saving time with reduced false positives.
Price: Free vulnerability scanner
Website: https://cirt.net/Nikto2
#9) GFI Languard
Best for Built-in Patch Management.

GFI Languard is a vulnerability scanner that automatically covers all important assets in your IT infrastructure as soon as it is deployed. It performs continuous scans to accurately detect vulnerabilities before attackers can.
However, it is GFI Languard’s patch management feature that makes it truly shine. The platform is constantly scanning your network for missing patches. It proactively deploys a relevant patch to fix detected vulnerabilities immediately. GFI Languard is constantly updating its list of patches to handle all kinds of vulnerabilities.
Features
- Full Visibility of Your Network’s entire portfolio.
- Automated Vulnerability Detection
- Automatic Patch Deployment
- Generate detailed compliance reports.
Verdict: GFI Languard lets your security team stay one step ahead of scanners, thanks to intuitive threat detection and an in-built patch management feature. We find it particularly impressive that GFI Languard can identify non-patch vulnerabilities by referring to an updated list that currently hosts information on over 60000 known issues.
Price: Contact for a quote.
Website: https://www.gfi.com/products-and-solutions/network-security-solutions/gfi-languard
#10) OpenVAS
Best for Open Source and Free Vulnerability Scanner.

OpenVAS is another open-source vulnerability scanning tool that can detect weaknesses on the web and fix them immediately. It leverages a feed that features daily updates to accurately detect all types of vulnerabilities and their variants.
The robust internal programming language it operates on makes it possible for OpenVas to pinpoint the exact location of the vulnerability. OpenVAS can be used for both authenticated and unauthenticated scanning. It can also be tuned suitably to support large-scale scanning.
Features
- Open Source Scanning
- Facilitates both Authenticated and Unauthenticated scanning.
- Generates reports with actionable insights.
- Accurate and fast detection
Verdict: Thanks to the robust internal programming language it operates on – OpenVAS is extremely quick and fast as a vulnerability scanner. The fact that it can be fine-tuned to support large-scale scanning makes it an ideal open-source scanner to gain full visibility over your entire IT infrastructure.
Price: Free
Website: https://www.openvas.org/
#11) Tenable Nessus
Best for Unlimited Accurate Vulnerability Scanning.

Tenable Nessus performs lightning-fast, in-depth scans to accurately detect vulnerabilities before they are found by an attacker.
The solution takes a risk-based approach to vulnerability identification and assessment. As such, it assigns threat levels to each detected vulnerability based on how high or low a threat they pose to your system’s security.
Recommended reading =>> Top alternatives to Tenable Nessus Scanner
Its in-depth assessment allows you to cover every corner of your network’s infrastructure and detect weaknesses that are otherwise hard to find. It also provides users with key metrics and comprehensive reports that make patching detected vulnerabilities simple.
Features
- High-Speed Scanning
- Continuous non-stop scanning
- Prioritize responses with risk-based vulnerability assessments.
- Generate reports featuring key metrics and actionable insights.
Verdict: Tenable Nessus is a widely used vulnerability scanner because of its high-speed assessment capabilities. It can be used in conjunction with penetration testing to simulate attacks and detect weaknesses. It comes with pre-built templates that make auditing and patching web assets simple.
Price: Contact for a quote.
Website: https://www.tenable.com/products/nessus
#12) ManageEngine Vulnerability Management Plus
Best for 360° full visibility and Patch Management.

ManageEngine is a vulnerability scanner that can effortlessly scan your system to detect zero-day, third-party, and OS vulnerabilities, among many others. The solution performs continuous scans to discover the weaknesses of all your local and remote endpoints.
ManageEngine also allows developers to leverage attacker-based analytics to detect and prioritize areas that are most likely to be exploited by attackers. Perhaps its biggest USP is the in-built patch management system it comes with.
With the help of this platform, you can discover, test, and deploy patches that automatically remediate vulnerabilities once and for all.
Features
- 360° Full System Visibility
- Continuous Automated assessment
- Patch Management
- Security Configuration Management
Verdict: ManageEngine Vulnerability Manager Plus is remarkable when it comes to handling vulnerabilities associated with high-risk software, security misconfigurations, and zero-day vulnerabilities.
Its in-built patch management feature allows you to automate the entire patching process. This tool is highly recommended if you want to quickly deploy patches to fix vulnerabilities once they have been found.
Price: Contact for a quote.
Website: https://www.manageengine.com/vulnerability-management/
#13) Frontline VM
Best for Risk-Based Vulnerability Assessment.

Frontline VM performs comprehensive vulnerability scans to identify vulnerabilities across your network’s entire portfolio, regardless of whether they are on the cloud or on-premise. Frontline VM verifies every vulnerability it detects to reduce the rate of false positives.
It also takes a risk-based approach to vulnerability assessment, assigning threat levels (High, Moderate, Low) to each detected vulnerability. Frontline VM leverages Intuitive Threat Intelligence to help you better understand vulnerabilities in your system.
Frontline VM also excels because of the analytics it provides that allows you to compare security assessment scores with other organizations like yours.
Features
- Risk-Based Vulnerability Assessment
- Referral to Wide Threat Landscape.
- Enhanced Peer Comparison
- Integrate with other third-party tools.
Verdict: Frontline VM earns a coveted position on this list because of its unique risk-based approach to vulnerability assessment. Not many tools generate reports that allow you to compare assessment scores with your peer organizations. Frontline VM does and thus qualifies as a powerful vulnerability scanner.
Price: Contact for a quote.
Website: https://www.digitaldefense.com/platform/frontline-vm/
#14) SecPod SanerNow
Best for SMEs, Enterprises, and MSPs; end-to-end vulnerability and patch management.

SanerNow Vulnerability Scanner offers the fastest 5-minute scans, powered by the natively built world’s largest repository with 175,000+ checks.
SanerNow Continuous Vulnerability and Exposure Management (CVEM) platform rapidly shrinks your attack surface by 3x.
It automatically detects and remediates vulnerabilities and exposures. These vulns include software vulnerabilities, misconfigurations, missing patches, and security posture anomalies from a single console.
Features:
- Industry’s fastest vulnerability scanning in just 5-minutes
- 175,000+ checks powered by natively built the world’s largest vulnerability database
- One single platform for identifying vulnerabilities AND remediating them
- Go beyond vulns such as misconfigurations, IT asset exposures, missing patches, security control deviations, and posture anomalies
- Integrated patching to fix vulnerabilities and exposures instantly
- Automated tasks from scanning to remediation
- Available on the cloud as well as on-premise IT environment
Verdict: SecPod SanerNow provides complete security and strong defense from cyberattacks with a single-pane-of-glass solution. You can rely on SanerNow for your organization’s safety and simplify your vulnerability management process with this excellent product.
Price: Contact for a quote.
#15) Intruder
Best for Continuous vulnerability scanning and attack surface reduction.

Intruder provides the same high level of security enjoyed by banks and government agencies with the leading scanning engines under the hood. Trusted by over 2,000 companies worldwide, it has been designed with speed, versatility, and simplicity in mind, to make reporting, remediation, and compliance as easy as possible.
You can automatically synchronize with your cloud environments and get proactive alerts when exposed ports and services change across your estate, helping you secure your evolving IT environment.
By interpreting the raw data drawn from leading scanning engines, Intruder returns intelligent reports that are easy to interpret, prioritize, and action. Each vulnerability is prioritized by context for a holistic view of all vulnerabilities, saving time and reducing the customer’s attack surface.
Features:
- Robust security checks for your critical systems.
- Rapid response for emerging threats.
- Continuous monitoring of your external perimeter.
- Perfect visibility of your cloud systems.
Verdict: Intruder’s mission from day one has been to help divide the needles from the haystack, focusing on what matters, ignoring the rest, and getting the basics right. Intruder helps you do that, saving time on the easy stuff, so you can focus on the rest.
Price: Free 14-day trial for Pro plan, contact for price, monthly or annual billing available.
Other Vulnerability Scanners
#16) Rapid7 InsightVM Nexpose
Best for Detecting Vulnerabilities in Real-Time.
Rapid7 InsightVM performs lightning-fast scans to detect vulnerabilities in real time. The tool provides interactive dashboards that can be used to find solutions to detect vulnerabilities. This is a lightweight agent that consumes minimal bandwidth when performing scans.
It classifies detected vulnerabilities based on their threat levels to prioritize the management of high-severity vulnerabilities over low-severity variants. It generates comprehensive reports and analytics that can be leveraged to remediate vulnerabilities before an attacker can find them.
Price: Contact for a quote.
Website: https://www.rapid7.com/products/nexpose/
#17) BeyondTrust Retina Network Security Scanner
Best for Cloud and Endpoint Security Scanning.
BeyondTrust offers a wide range of tools to identify and patch vulnerabilities. It can discover, manage, and audit credentials related to privileged accounts.
It can also be deployed to enforce the least privileges across Mac, Windows, Linux, and Unix endpoints. It also allows you to remotely manage service desks, vendors, and managers. Apart from endpoint privilege management, the platform also allows you to enforce the least privilege and control access across the cloud.
Price: Contact for a quote.
Website: https://www.beyondtrust.com/privilege-management
#18) Tripwire IP360
Best for Risk-Based Vulnerability Scanning.
Tripwire allows you to accurately identify and discover all assets in your network. It later performs deep scans that reveal vulnerabilities that may pose a potential threat to your system’s integrity.
It also assigns threat levels to detected vulnerabilities to identify which of them pose a significantly higher level of threat to help developers prioritize their response. Tripwire IP360 integrates well with third-party asset management and help desk solutions.
Price: Contact for a quote.
Website: https://www.tripwire.com/products/tripwire-ip360
#19) W3AF
Best for Open Source Web Scanner.
W3AF is an open-source and free scanner that can identify over 200 vulnerabilities and their variants. It builds an entire attack and audit framework that accurately detects vulnerabilities before an attacker can find them.
It is very easy to deploy and will deliver results as soon as it is deployed. You can initiate scans and find remediation solutions for them with just a few clicks.
Price: Free vulnerability scanner
Website: http://w3af.org/
#20) Comodo HackerProof
Best for PCI Scanning.
Comodo HackerProof is a user-friendly website scanner that can accurately identify all types of vulnerabilities on a website or application. It comes with PCI scanning tools, which can be important to scan a company’s network that accepts and processes credit card data.
Comodo HackerProof can be used to build trust for your website among visitors. It performs scheduled scans to make sure there aren’t weaknesses in your website that allow attackers to get in.
Price: Contact for a quote.
Website: https://www.comodo.com/hackerproof/
Frequently Asked Questions
Why Would You Use a Vulnerability Scanner?
Vulnerabilities act as holes or weaknesses in an application that attackers can exploit to gain access to critical information. It is imperative to find these vulnerabilities before an attacker can exploit them to get in.
Vulnerability Scanners scan every corner of your application to not only detect vulnerabilities but also classify them based on their threat level. They generate comprehensive reports that contain actionable insights on how you can effectively remediate the identified vulnerability.
What are the Types of Vulnerability Scanners?
There are 5 major types of vulnerability scanners.
They are:
– Network-based scanners
– Host-based scanners
– Application Scanners
– Wireless Scanners
– Database scanners
What do Vulnerability Scanners Scan?
Vulnerability Scanners scan computers, networks, and communication equipment to detect system weaknesses plaguing them. They also suggest remediation practices to fix these vulnerabilities before it is too late.
Is Vulnerability Scanning Legal?
Vulnerability Scanning is legal on an application or network system that you own or have permission to scan. Remember, port or vulnerability scanning is also done by hackers to find vulnerabilities.
So although there are no laws that explicitly ban port and vulnerability scanning, scanning without permission can result in legal problems. A civil lawsuit can be brought against you by the owner of the scanned system. The owner of the scanned system can also report you to the associated ISP.
Which is the Best Vulnerability Scanner?
The following 5 have gained enough reviews in recent times to qualify as some of the best vulnerability scanners available today. These tools are also an integral part of our list.
– Invicti (formerly Netsparker)
– Acunetix
– Burp Suite
– Nikto2
– GFI Languard
Conclusion
Cyber-attacks are at an all-time high and attackers have only become bolder in their attempts to breach secure networks.
They are successful in their endeavors if their scans detect vulnerabilities that can be exploited to their advantage. This is why businesses today of all sizes must have vulnerability scanners, ideally those that perform continuous, automated scans.
Suggested Read => Top Vulnerability Scanning Assessment Tools
Vulnerability Scanners can identify vulnerabilities, classify them based on how severe their threat is, and generate reports that include suggestions on how to address them in the best possible manner.
As per our recommendation, we would like you to try Invicti and Acunetix as they are easy to operate and have a comprehensive list of tools to make vulnerability detection and remediation simple.
Research Process
- Time Taken To Research And Write This Article: 15 Hours
- Total Vulnerability Scanners Researched: 30
- Total Vulnerability Scanners Shortlisted: 15











