A complete review and comparison of the top Software Supply Chain Security Solutions for organizations and their businesses:
In 2024, most software utilized a supply chain that included open-source repositories, pre-existing libraries, CI/CD tools, version control systems, and much more.
With so many parts combined to make the final product and code reused across hundreds of thousands of projects, hackers have a lot to choose from and a lot to gain when targeting the software supply chain. Unfortunately, the weakest link in the chain now defines software security.
Table of Contents:
Software Supply Chain Security Tools: An In-Depth Review

In recent years, we’ve seen significant growth in software supply chain attacks, including the infamous SolarWinds hack. What makes these attacks so severe is the fact that they are not limited to a single company.
With SolarWinds, a vulnerability in the company’s Orion platform (used for infrastructure monitoring) led to hackers compromising over 30,000 organizations, including the US government.
SolarWinds is a famous example of a broader trend. Gartner predicts that by 2025, 45% of organizations around the world will have been the target of a software supply chain attack, a 300% increase.
Given the potential consequences and their growing frequency, software vendors, organizations developing in-house applications, and government agencies all need to increase their focus on software supply chain security. To help protect your software supply chain, we’ve compiled the best security platforms out there.
Software Supply Chains: What Are They Exactly
Modern software development relies on ‘sourcing’. Dev teams no longer need to write every line of code or build the entire tech stack. Instead, they can integrate existing third-party resources and spend their time focusing on the new code that differentiates them from the competition.
There is a significant overlap in the basic functionality of many applications – from encrypting and safely storing user data to search functions, syncing across devices, and much more. As a result, little is gained, and a lot is lost, in terms of time and resources, by rewriting code where pre-existing alternatives are widely available.
Thankfully, a universe of open source and proprietary resources has already been invented for software developers to rely upon. The entire code that’s used to develop, publish, run, or interact with your product makes up your software supply chain.
It includes all components, their sources, where and when they are used, any known vulnerabilities, supported versions, and licensing information. Typically, organizations track all this information using a Software Bill of Materials (SBOM), analogous to a bill of materials widely used in other industries, such as manufacturing.
SBOMs have become critical tools in software supply chains and their security, acting as an inventorying tool – a list of all the components that went into making the final product.
Developers and other stakeholders can review the SBOM to check for vulnerabilities, ensure components are up to date, respond efficiently to new threats, and evaluate the product’s overall risk. Naturally, utilizing externally written code brings significant benefits, but it can also introduce additional risks.
Importance of Software Supply Chain Security
Software supply chain attacks have seen a significant increase in recent years. In fact, in 2021, supply chain attacks increased by more than 300% compared to the previous year.
Since development pipelines are now complicated environments filled with CI/CD tools and pre-existing (often open-source) code, cybercriminals now have a vast attack surface to target.
Beyond the SolarWinds hack, we have already witnessed a series of major supply chain attacks, including:
- Kaseya
- Codecov
- ua-parser-js
- Log4J
In all of these examples, a single vulnerability in commonly used code led to a wider breach affecting many victims.
When development teams deliver software for internal or commercial use, they are endorsing the security of the entire product, even the code they didn’t write. But, as we’ve seen, vouching for third-party resources can have dire consequences.
Software supply chain security ensures all third-party code is up-to-date, untampered with, and contains no malicious code or known vulnerabilities.
To do this, you have useful tools that can check every component across the entire Software Development Lifecycle (SDLC) including:
- In-house code
- Outsourced development
- Commercial software packages
- Open-source deployments
- Interfaces and protocols
- Development tools
- Or, anything else that makes up or interacts with the final product.
Scanning individual components for digital artifacts is vital, but it is also critical to understand the dependencies within the project. How do the different parts of code interact with one another? How would a vulnerability affect the rest of the software chain?
A comprehensive software supply chain solution also scans for dependencies and known exploits and implements network protections to guarantee there are no unauthorized access or unapproved changes.
To ensure the end product’s safety, teams can either work in an airtight environment or utilize integrity validation to scan the final code and check for changes. Guaranteed deployed software is untampered with and allows teams to know it is running exactly as intended.
For software supply chain security to be successful, it must:
- Provide continuous code assurance and check the integrity of every component across every part of the SDLC.
- Utilize evidence-based signed attestations to track all files within the project and guarantee they are untampered.
- Enforce compliance, including the latest software supply chain best practices and regulations from SSDF (Secure Software Development Framework) and SLSA (Supply chain Levels for Software Artifacts).
- Facilitate both inter and intra-organizational collaboration so that various organizations and teams can work together to guarantee protection and share the same insights.
List of the Best Software Supply Chain Security Solutions
The following are the best software supply chain security service providers:
- Mend.io
- Anchore
- Codenotary
- Contrast Security
- Argon
- Cybeats
- Legit Security
- Cycode
- Chainguard
- Arnica
- Scribe Security
Comparing the Top Software Supply Chain Security Companies
| Solution | Best suited for | Free trial? | Rating |
|---|---|---|---|
| Mend.io | Automated supply chain security with AI visibility. | Free demo available | 4.5/5 stars |
| Anchore | Generate SBOMs and track vulnerabilities | No | 4.5/5 stars |
| Codenotary | SBOM and vulnerability scanning over an immutable DB | Yes | 4.4/5 stars |
| Contrast Security | Detection of real vulnerabilities with a high level of accuracy and precision | Yes | 4.2/5 stars |
| Argon | Mapping pipeline security posture and risks and preventing misconfigurations and known risks | Yes – 14 days | 4.2/5 stars |
| Cybeats | Generate SBOM to understand and track third-party components | No | 4.2/5 stars |
| Legit Security | Scoring risks across CI/CD pipelines, SDLC systems, product lines, and code | No | 4.2/5 stars |
| Cycode | Finding CI misconfigurations. Scanning engines that look for issues like hardcoded secrets, infrastructure as code misconfigurations, and code leaks. | Yes – 14 days | 4/5 stars |
| Chainguard | Signing and verifying software artifacts | No | 4/5 stars |
| Arnica | Access management | Yes | 4/5 stars |
| Scribe Security | End-to-end software supply chain security solution: automatically generate shareable product SBOMS and gain insights around vulnerabilities and code tampering | Yes | 5/5 stars |
Here is a brief overview of each tool:
#1) Mend.io
Best for automated supply chain security with AI visibility.
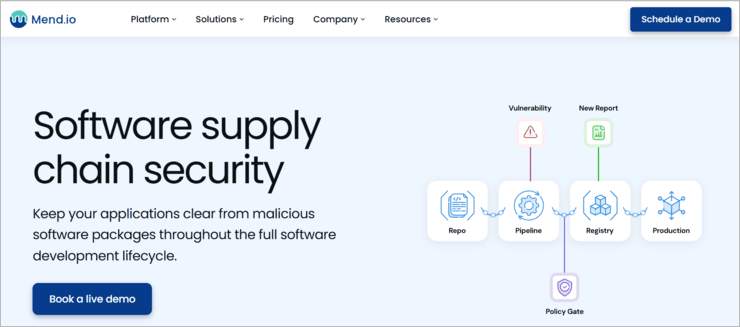
Mend.io is an enterprise-grade application security platform offering deep supply chain protection through its SCA, automated dependency updates (Mend Renovate), container security scanning and AI components visibility – all under one roof. With Mend SCA, organizations can detect and remediate open source vulnerabilities, manage licenses, and analyze reachability to prioritize exploitable risks.
What sets Mend.io apart is its native integration of Mend Renovate, a powerful automation engine that keeps dependencies up to date across repositories. Combined with Mend AI, Mend.io can detect and secure embedded AI models, agents, RAGs and MCPs giving teams full visibility into risks introduced to their applications.
Built for scale, the platform enforces policies across large codebases with low noise and high accuracy. Its one-platform, one-price model simplifies adoption across security, development, and legal teams.
Key features:
- Mend SCA with advanced reachability analysis and license compliance policies
- Mend Renovate for automated dependency updates across repos
- Mend AI for AI components detection for visibility AI red teaming
- Mend Container for integrated container scanning and CI/CD integrations
- One unified platform with 5 AppSec tools for one price.
Verdict: Mend.io delivers scalable software supply chain security with automation, reachability, and AI visibility – ideal for modern development pipelines.
Price: One platform with all capabilities for $1,000 per developer. No professional services needed. Substantial discounts for teams with 50+ developers.
#2) Anchore
Best for generating SBOMs and tracking vulnerabilities.

Anchore is a software supply chain security platform leveraging SBOMs to track dependencies and changes for each build while monitoring for new vulnerabilities after deployment.
The platform provides secure container-based workflows for various teams, including enterprises, software vendors, and the public sector. As a result, internal applications and software releases remain safe while also meeting stringent federal and DoD compliance standards.
Anchore’s security checks are embedded into developer tools to increase visibility and compliance monitoring. Anchore offers free demos to show prospective customers the platform’s image inspection, policy-based compliance, and integration within CI/CD tools.
Capabilities:
- SBOMs
- Container vulnerability scanning
- CI/CD pipeline security
- Container registry scanning
- Kubernetes images scanning
- FedRAMP vulnerability scanning
- Container compliance
Verdict: Anchor’s SBOM-powered platform protects and secures the software supply chain, whether you release software products as SaaS or host them.
Website: https://anchore.com/
#3) Codenotary
Best for SBOM and vulnerability scanning over an immutable DB.

Codenotary Trustcenter offers a solution for software supply chain security. The company claims to reduce the cost of identifying and removing unwanted artifacts, such as Log4J, by up to 90%. Codenotary Trustcenter is based on open source immudb, an immutable database.
It offers fast and straightforward CI/CD integration with the rapid identification of untrusted components within Docker containers and Kubernetes deployments. The platform also allows DevOps teams to attach tamperproof SBOMs to all their apps, making the entire supply chain visible to customers, auditors, and compliance professionals.
Capabilities:
- Vulnerability and compliance
- SBOM Lifecycle
- Code signing
- K8s Enforcement
Verdict: Codenotary offers an open-source solution that protects DevOps teams against cyberattack risks. It offers a fast and simple integration with all existing languages and CI/CD.
Website: https://codenotary.com/
#4) Contrast Security
Best for detection of real vulnerabilities with a high level of accuracy and precision.

The Contrast Secure Code Platform empowers developers to identify and fix risks in real time for the complete SDLC. The platform integrates seamlessly into DevOps pipelines with broad support for application security platforms.
The CodeSec, by Contrast, scanner can be implemented quickly to discover dependencies and secure vulnerable libraries for faster deployment and standardized SBOMs. Contrast embeds directly into the code to detect vulnerabilities with accuracy and precision.
Capabilities:
- CodeSec by Contrast – secure code through a simple command line interface.
- Contrast Scan – quickly identify and fix vulnerabilities.
- Contrast Protect – block run-time attacks.
- Contrast Serverless – fix security issues across serverless environments.
- Contrast SCA – test third-party, open source code.
Verdict: Contrast offers to increase confidence in the quality and security of applications, as an integral part of the SDLC. It enhances developer productivity and security.
Website: https://www.contrastsecurity.com/
#5) Argon
Best for mapping pipeline security posture and risks and preventing misconfiguration and known risks.

Argon provides a security platform for the software supply chain, utilizing a zero-trust deployment approach to ensure visibility, governance, and protection. A DevOps native solution, Argon can easily onboard into the team’s existing CI/CD environment, with dozens of out-of-the-box integrations with popular tools and frameworks.
Argon’s instant visibility delivers actionable insights and eliminates blindspots to show security risks, misconfigurations, or unauthorized changes. The zero-trust approach detects changes in both project components and user behavior. Risks can be prioritized and assigned severity scores and automated responses can immediately respond to threats.
Capabilities:
- Automated responses for each security policy.
- Continuous scanning for secrets and key discovery.
- Compliance review for the entire dev pipeline.
- Source code leaks to reduce exposure.
- An intuitive and customizable security rule engine.
- Least privileged access.
Verdict: Argon enables DevOps and security teams to create tamper-proof software delivery pipelines. It helps you ensure software release trust by delivering visibility, security, and integrity to the CI/CD pipeline.
Website: https://www.argon.io/
#6) Cybeats
Best for generating SBOM to understand and track third-party components.

Cybeats SBOM studio is a management solution for the collection, storage, and distribution of SBOMs. This includes inventory management, risk assessments for vulnerability and licensing risks, and enforcing compliance standards.
Cybeats SBOM solution is aimed at providing comprehensive management for software consumers and producers, as well as government vendors.
SBOM Studios informs users of third-party options’ reputation, nature, and popularity. In addition, it proactively improves risk transparency to detect vulnerabilities and licensing issues early in the product life cycle.
Capabilities:
- SBOM covers the product lifecycle, including security scores.
- Supply chain screening into the security of third-party software.
- Software license analysis to maintain compliance.
- Industry compliance to inspect all software in the supply chain.
- Accurate budgeting based on SBOM forecasts for cybersecurity costs.
- Assesses the potential implications of third-party software breaches.
- Transparency throughout the software supply chain.
Verdict: Using Cybeats’ SBOM Studio, you can document what you have and where it came from, as well as plan maintenance that prevents security posture degradation over time.
Website: https://www.cybeats.com/
#7) Legit Security
Best for scoring risks across CI/CD pipelines, SDLC systems, product lines, and code.

Legit Security implements risk scoring across CI/CD pipelines, SDLC systems, and code to secure software supply chain environments.
The platform combines discovery and analysis with hundreds of security policies to detect, score, and remedy threats. The discovery covers all SDLC assets, including dependencies and pipeline flows, returning a visualization of the complete supply chain.
Users can switch security policies on or off depending on their preferences. In addition, continuous assurance tracks security coverage during the SDLC, monitoring incident trends and comparing security posture.
Capabilities:
- Automated discovery and analysis.
- Best Practice Security Policies and Remediate Risks.
- Continuous assurance.
- Full SDLC transparency.
Verdict: A SaaS-based platform that supports both cloud and on-premises resources and ensures that your applications are released without vulnerabilities
Website: https://www.legitsecurity.com/
#8) Cycode
Best for finding CI misconfigurations. Scanning engines look for issues like hardcoded secrets, infrastructure such as code misconfigurations, and code leaks.

Cycode claims to offer comprehensive software supply chain security across the entire SDLC. The platform integrates with existing DevOps tools and infrastructure to provide governance and a series of scanning engines that find security misconfigurations and gaps.
In addition, Cycode’s knowledge graph allows us to track code integrity, events, and user activity across the SDLC. You can see the platform in action by booking a demo.
Capabilities:
- Source control and CI/CD security.
- Visibility of SDLC flow Hardcoded secret detection.
- Source code leakage detection.
- Infrastructure as code security.
Verdict: Cycode identifies vulnerable dependencies and security issues across the SDLC, pin-points vulnerable dependency locations, and prioritizes threats by exploitability.
Website: https://cycode.com/
#9) Chainguard
Best for signing and verifying software artifacts.

Chainguard Enforce offers a containerized workload solution for software supply chain security. A native Kubernetes application, Chainguard Enforce allows users to define, distribute, monitor, and enforce policies that guarantee trusted container images to ensure developers deploy safely.
The Chainguard team previously helped build Sigstore, an open-source project providing a way to sign software for verification and security. Chainguard Enforce’s supply chain security solution is based on Sigstore and meets a number of SSDF recommendations.
Capabilities:
- Centrally managed and administered policy agent.
- Integration of multiple CI platforms.
- Continuous verification and alerts for policy and compliance deviations.
- Real-time asset inventory for the entire organization.
Verdict: Chainguard offers confidence in open-source software by providing an easy way of signing and verifying software artifacts so they have a trail to trace if a breach occurs.
Website: https://www.chainguard.dev/
#10) Arnica
Best for access management.

Arnica’s behavior-based software supply chain security solution minimizes risk while optimizing the cost for DevOps teams by enhancing security by utilizing the existing developer toolset.
Arnica identifies deviations from expected operations for DevOps governance and implements excessive permission reductions to least privilege autonomously. All this is built around its behavioral analysis, spotting anomalous actions from each identity to reduce risk.
Arnica aims to bring together: development, security, finance, and operations teams, offering benefits for each:
- Developers – automatic code reviews for low-risk updates.
- Security – identifying insider threats and account takeovers.
- Finance – license cost optimization.
- Ops – reduce time spent managing permissions.
Capabilities:
- Secret detection of public and private repositories.
- Excessive permissions identification.
- GitHub user mapping to validated emails.
- Contextual GitHub application inventory.
- Behavior-based least privileged access.
- Behavior-based GitHub CODEOWNERS creation and adjustment.
- Abnormal developer behavior detection.
- Self-service permission provisioning via Slack.
Verdict: By using Arnica you’ll get more context on developer assets and act upon them. You can also identify security risks and mitigate them easily.
Website: https://www.arnica.io/
#11) Scribe Security
Best for end-to-end software supply chain security solutions. It auto-generates shareable product SBOMS and gains insights around vulnerabilities and code tampering.

Scribe’s software supply chain security solution, Scribe Trust Hub, is available for a free trial. Scribe Security delivers continuous code assurance for the entire software development lifecycle in a zero-trust approach.
Scribe automatically generates shareable product SBOMS for insights around vulnerabilities in your containers, dependencies, pipelines, and code tampering. This includes ensuring the code is untampered, source code integrity assurance, and open source dependency validation.
Scribe Security provides visibility to pipelines, validates the integrity of containers, and checks that no malicious modifications were made. Scribe utilizes the “hash everything, sign everything” principle to track every file from origin to build. The product is also easily integrated within DevOps pipelines and is currently offering free access.
Capabilities:
- Continuous code integrity and provenance throughout the SDLC.
- SBOM management and sharing platform.
- Reports of suspicious or vulnerable code components.
- Governed development processes.
- Compliance with SSDF and SLSA recommendations.
Verdict: Scribe Security is truly an end-to-end software supply chain security tool. It provides the ability to build trust in your software across teams and organizations. It allows you to automatically generate shareable product SBOMs and gain insights into vulnerabilities and code tampering.
Conclusion
Having an effective software supply chain security vendor is the key for organizations and their business.
With attackers targeting the entire supply chain, organizations need software supply chain security platforms that protect the entire supply chain – checking every component for vulnerabilities, tracking any changes in the final build, and enforcing compliance.
With one of our ten recommendations, you can help keep your network protected and stay ahead of attackers.











