An In-Depth Look at the DNS, FTP, SMTP, and MIME Application Layer Protocols of TCP/IP Protocol Suite:
In this In-Depth Networking Training Series, we explored the Differences between IPv4 and IPv6 Addressing in our previous tutorial. The application layer is the uppermost layer of the TCP/IP protocol suite.
In this tutorial, we will explore the various protocols that work on this layer in detail.
Being a software tester, it is important to understand the different features of each of the application layer protocols as the testers work on this layer and need it for their day to day work.
Each of the protocol has its own role and importance. A few of the majorly deployed protocols which we will discuss here include DNS, FTP, HTTP, MIME, SMTP, LDP, and DHCP.
We will study these protocols into two parts. This tutorial is the Part-1 and here we will discuss DNS, FTP, SMTP, and MIME protocols.
Table of Contents:
DNS (Domain Name Server)
If any user from the personal computer, laptop or tablet uses the Internet and tries to login into some website then the user is using DNS for sure. Thus it is very important to understand the working on a domain name server.
PC’s, laptop or tablets don’t understand the language of a web address, which means the domain name like Google.com to make them understand for which site we are looking for. Thus DNS came into the role and provides the host with the mapped IP address in respect to the domain name of the website.
Suggested read =>> What is Uniform Resource Identifiers
As shown in the above figure, when we request for a web page from our PC on the Internet like PC1 is requesting for www.softwaretestinghelp.com, then resolving the domain name query and providing the respective IP address in return is the part of work of the DNS server.
DNS server stores the database of all the relevant IP addresses mapped with their respective domain names.
Further reading =>> How to flush the DNS Cache
The DNS query for requesting the IP address in respect to the domain name goes to the DNS server 1 from PC1. The server checks within itself, if it has the IP address regarding the query, and it returns a DNS response with the resolution.
Otherwise, it forwards it to another DNS server 2 requesting for information. This time it gets the resolution from the DNS 2 and it gets mapped with the IP address i.e. 10.150.120.2 corresponding to the Domain name in response and sends it back to PC1.
The PC1 now have the destination IP address and it can communicate further with the known IP address as per the routing.
Now the question arises, as of how the PC will come to know which DNS should be used to get the IP address.
The answer to this is when we connect our system to the ISP, the network devices like a router or switch which assigns the routing information and other configurations as well send which or how many DNS server the PC should connect with to get the address translation.
Recommended reading =>>Top Blockchain DNS Software
FTP (File Transfer Protocol)
It is one of the widely used application layer protocol of the TCP/IP protocol suite. FTP is basically used to exchange data between two host devices over the Internet or Intranet securely.
It is referred to as one of the safest modes of file sharing among systems, and thus it is deployed by large industries, universities, and offices.
It works in the client-server model and thus the user needs an FTP client program to run FTP on its system. The common types of FTP client program include Filezilla and Dreamweaver etc.
The data transfer takes place only in one direction at a time. The FTP protocol carry out many duties apart from file transfer like creation and deletion of data files, listing, renaming, etc.
The FTP Model
In this model, one host behaves as the client and another host as a server. The one who requests for file-sharing or data is the client host and one which in response completes the request is the server host.
Firstly the FTP connection is established between the client and server computer and data exchange take place after that. Two channels come into the picture of FTP connection i.e. control channel and data channel.
The control channel establishes the connection between the client and server and remains open for the overall session. The control channel port number is 21 in TCP/IP. While the data channel opens when the client request for a file sharing and get closed after the completion of the request by the server.
Two processes naming data transfer process (DTP) and protocol interpreter (PI) are used in managing the communication between the client and the server. The DTP establishes and manages the connection for the data channel, while PI manages the DTP by applying commands given by the control channel.
The server host end PI is accountable for analyzing the commands received from the client host end via the control channel, connection establishment, and in running the DTP. The client PI is accountable for forwarding the FTP commands, receiving the response from the server and establishment of the connection with the FTP server.
After the establishment of a connection between the FTP client and the FTP server, the client builds up the connection and sends the FTP commands to the server. The server analyzes them and in response completes the request.
Now the server end PI sends the port detail on which the files will be forwarded to the client DTP. The client DTP then waits for the data to arrive at the decided port from the server.
The FTP Response
To make out a secure and reliable file transfer between the client and server, it is important that the server and client should remain in synchronization with each other.
Thus for each command executed by the client, a user is acknowledged by the response and the action is performed by the server host in order. The response consists of a 3 digit code plus a text (a character string is separated from digit by a space) denoting the processing of the commands.
Types of Connection
The FTP server is connected to the FTP client on the control port 21. After this, the client will decide which type of connection it will make with the FTP server, i.e. whether an active or passive connection.
(i) Active Connection: If an active connection is established, then the data connection from the server end is opened on port 20 or to a greater range towards the client’s end. Then all the data flow will take place on this connection.
(ii) Passive Connection: If the passive connection is established, the client requests for passive connection from the server and assigns any port greater than 10,000. The server bounds itself to this port and gets back to the client with it.
The client then opens a new data connection for a particular session on this newly bounded port. In a passive connection, every time a new port is assigned when a new data connection request is raised from the client’s end. The latest trend in the networking system operates mostly in passive mode.
Example: Let’s take the example of a software organization, where hundreds of performance and daily activity reports are generated by the employees and those need to be shared with their vertical head, CEO or seniors at the remote end.
One way of sharing the daily reports and tracker is to send an e-mail to all of them. However, it takes a lot of time and if the size of the attachment is big in an e-mail, then it will take much time for downloading and the mailbox will get full frequently due to oversized mails.
The other way to do this is that the creators of data will put the reports and trackers on the FTP server and share the path with each concern. In this case, the end-user will behave as the client host and can access the files of their era from the server by just logging onto the server.
The server can be made secure by putting a password. Only the concerns will have the username and password to access it. The port used here is 21. As per rights granted to the clients, they can also create a copy, modify and delete the files on the server and from the server.
SMTP (Simple Mail Transfer Protocol)
SMTP is the standardization for transmission of electronic mails on the Internet.
It is used by the e-mail server for sending and receiving messages, but the client host-based application only uses it for sending messages to the mail server. For receiving purposes, they use POP3 or IMAP.
It is a TCP/IP application layer protocol and the TCP port used by the mail servers is 25 while the mail clients use the port 587 or 465 for communication.
The outlook mail system of Microsoft system, Gmail and Yahoo mail, deploy SMTP for sending and retrieving emails from the exterior world whereas for interior mail exchange between their respective systems they use their own protocols.
Mail Processing Scenario
The client using the e-mail services known as mail user agent (MUA) deposit mail to the mail server, Mail submission agent (MSA) using SMTP on port 587. The MSA forwards the mail to its Mail transfer agent (MTA) which in turn does the processing on the PC or laptop host device.
#1) Sometimes for sending the mail to the recipient host, it can move through many intermediate computer host devices, therefore, each device uses SMTP to forward messages on the next host device until it reaches the destination.
#2) The MTA deploys the DNS to find out the mail exchanger record (MX), which provide the details about the domain of the receiver. (Means the part of the mail address after @ For Example Gmail or Yahoo mail etc).
On the basis of information gathered from the MX record about the destination host, the MTA finds out the exchange server and connects to it as a SMTP client for message delivery.
#3) The transportation of message can move through a single hop or series of intermediate hops to reach the final destination. Once the final destination is reached, the MTA handovers the message to MDA (message delivery agent) for final delivery. The MDA stores messages in the appropriate mailbox format.
#4) After the delivery of the mail to the local mail server, the mail is stored, so that it can be retrieved by authenticated end users, i.e. MUA’s. The e-mail clients use IMAP or POP protocol to access the emails and for receiving the mail in the desired format Microsoft Outlook, Lotus Notes etc., which are designed for the SMTP format are used.
#5) The SMTP only concerns about the transportation of the e-mail and not the content of it. It is a connection-oriented protocol and the protocol messages are text-based.
A particular SMTP session includes commands initiated by a SMTP client and the respective response from the SMTP server. At the sending end, the initiating agent performs the actions while at the receiving end the listening agents and the recipient perform the tasks.
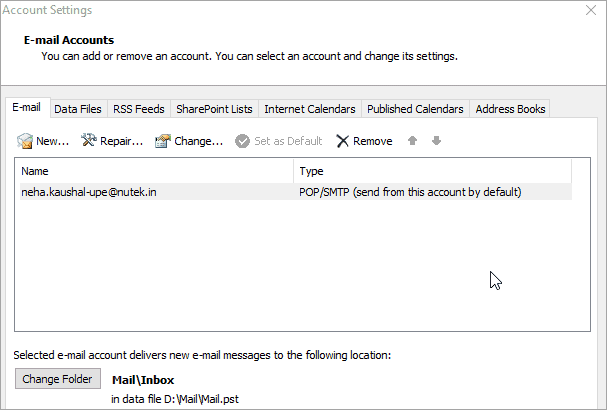
The role of SMTP in outlook is shown with the help of the below screenshots and which of the configurations of SMTP is done for sending e-mails is described as well.
Screenshot 1: In the below figure, the default settings of the mailbox are set and SMTP is chosen for sending e-mails.
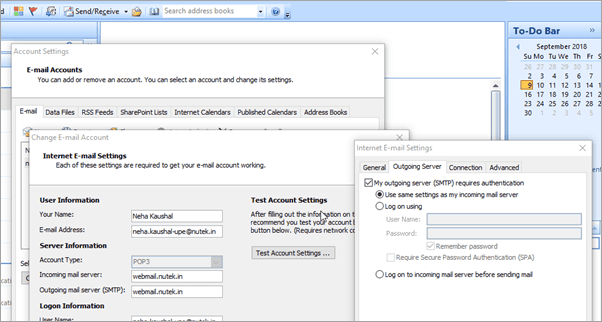
Screenshot 2: In the below figure, after doing e-mail settings, the internet e-mail settings is done in which the address of the outgoing mail server is set, and the default server chosen by outlook is SMTP. Hence, as per the web address of the web server, we are using, the server address is set as webmail.nutek.in.
After this, we go to the more settings tab, in which on the outgoing server option, we checkmark as SMTP authentication required for the outgoing server and also checkmark the same settings for the incoming server. It is not necessary to choose the same settings for the incoming server as well, but here we are using the same server for both.
Screenshot 3: Now let’s move to the advanced setting tab of the more settings option, here the incoming and outgoing server port is defined as 995 and 465 as mentioned earlier and check mark on the encrypted connection to ensure secure communication.
So from the above configuration settings of the mailbox in outlook, we can send and receive e-mails over internet connections by using SMTP.
MIME (Multipurpose Internet Mail Extensions)
It is basically an extension of the initial e-mail protocol known as SMTP and allows the users to use the protocol for sharing various kinds of data files on the Internet such as Audio, video, images and various program files along with ASCII text as deployed in the original one.
Features of MIME
- In a single message, several attachments can be sent easily.
- There is no limitation of the length of the message.
- Apart from ASCII codes, other data files can also be shared through it.
- Different kinds of layouts, font style, colors, and size can be used in the message.
- MIME uses the special header format to illustrate the type of format that the mail body is using. Hence, it will make it simple for the email-client to understand it in the correct format.
- Even though MIME is designed to support the SMTP, the content type which is defined in the MIME has the significance in the Communication protocols apart from the e-mail.
The web servers add the MIME header at the starting point of the circulation of web data. The web clients, thus use this content-type header for finalizing the suitable viewer application for their service as indicated by the header.
MIME Headers
(i) MIME-Version: The existence of this header specifies that the message is MIME formatted. The latest version used is 1.0, hence it is shown as MIME-Version: 1.0.
(ii) Content-Type: It specifies the message data’s type and subtype. The default header value will appear as Content-Type: text/plain. The above type and sub-type mean that the message contains simple text.
For Example, The detailing for image, audio, and video will be like image/gif, audio/mp3, and video/mp4.
(iii) Content-transfer-encoding: It specifies the type of encoding deployed in the message body. The various encoding techniques used are 7-bit, 8-bit, binary, base-64 for binary files with attachments and quoted-printable.
(iv) Content-Disposition: It specifies the presentation style and the filename associated with the message.
The presentation style can be of two types, first is inline in which whenever the mail is displayed, the presentation style will automatically come up, and second is the attachment type in which it is not displayed until we perform a certain action to open it.
The MIME is used in the HTTP protocol to distinguish between the types of web documents used. During the communication session between the web server and a browser, firstly the web server sends the MIME content type.
For Example, Content-disposition: attachment to browser thus the browser comes to know how it should display the content.
Multipart- Messages and Subtypes
There are various kinds of sub-types as mentioned below:
- Multipart/mixed: It is deployed for sending several elements like the plain text with attachment.
- Multipart/alternative: It specifies the alternative method to show the content of the message in a form which can be understood by the user’s client. Generally, it is used to display the content of the message in a text or HTML format. Please remember that the content is the same and only the format is dissimilar.
- Multipart/signed: It is deployed to impose a digital signature with the message in the e-mail.
- Multipart/related: It specifies the related message information of the whole message. This is mostly used when a web page contains various images or video files within it. Thus the overall web page is sent as a single message and in the later part, the images or videos are retrieved.
- Multipart/mixed-replace: It is deployed for streaming of video, i.e. an online movie in collaboration with the HTTP.
There are many other messages types as well, but only a few important ones are explained here.
Conclusion
We have discussed some of the important application layer protocols of the TCP/IP protocol suite here in this tutorial.
Further reading =>> What is SNMP?
We can conclude that these are very useful in our daily activities in the field of communication over the Internet. These, in turn, have a great significance in the information and networking systems industry.