Here you will understand the need for phishing prevention solutions. Review, compare and select among the list of the BEST Phishing Protection Solutions:
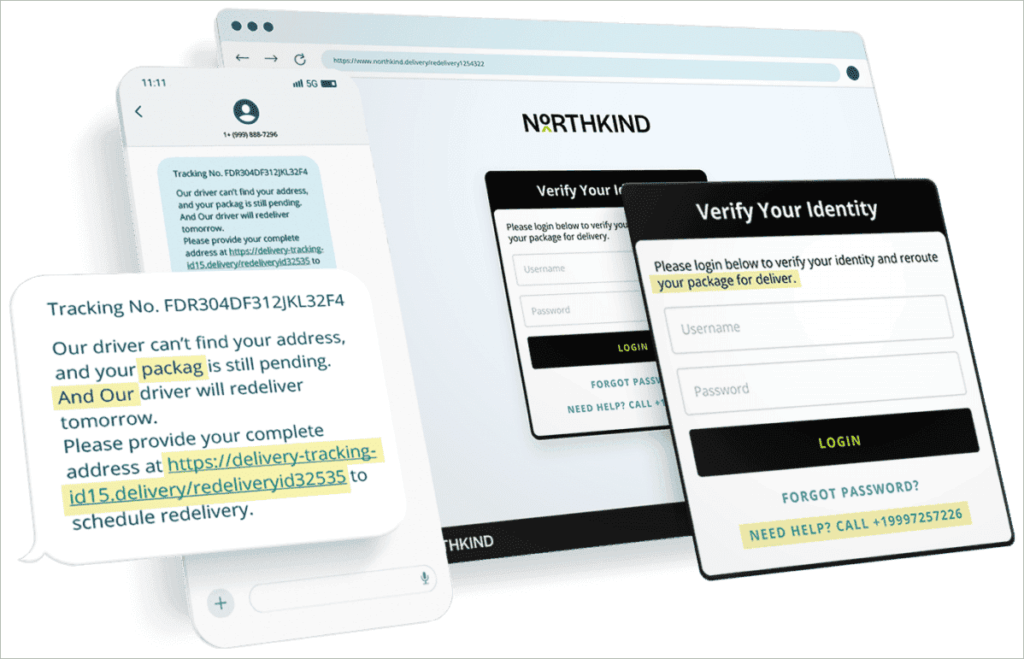
Phishing refers to cyber activity where the attacker contacts individuals for their sensitive information to access accounts, steal data and identities, and download malware onto the user’s computer via email, browser, phone, or social media.
To prevent these kinds of activities, we have various phishing protection solutions or some open-source anti-phishing tools.
These solutions help users block both phishing delivery (email, text) and the phishing payload (website, malware), and help to raise user awareness.
Table of Contents:
Phishing Protection Security Solutions – Review

Need for phishing prevention solutions:
- Growing attack surface: Users are communicating over countless applications and media, and are exposed to more and more phishing attacks.
- Business agility: Securing user interactions allows employee freedom and increased productivity.
- Browser usage risk: There are many web-borne risks that need prevention, like malicious redirects, unsafe plugins, DNS attacks, unsafe use of safe passwords, and so on.
- Working from unmanaged devices: It is helpful in managing and providing security to unmanaged devices. Due to digital transformation and remote work, now we spend our day working from the browser, often from unmanaged devices.
Types of anti-phishing solutions:
- Browser-based Solutions: Scans any web page vs. attack techniques. This solution is focused on eliminating phishing payloads (credentials theft, malware download, etc).
- Email-based Solutions: Scans every email and looks for suspicious indicators. This solution type only protects emails and is focused on phishing delivery.
- API-based Solutions: Checks URLs, messages, and files using a cloud sandbox activated via API. This solution type works on many collaboration tools but is relatively responsive and not proactive.
Benefits of Anti-phishing solutions:
- Identifying Risk: A phishing prevention solution identifies risks associated with email, web, or text that can hamper sensitive information of the users. It determines the phishing by using a common tactic, which is the email conveys a suspicious tone with increased urgency.
- Reduce Cyber Risk: It helps in reducing cyber risks by educating and taking prior prevention measures. Some of the cyber risks are Business Email Compromise (BEC), internal and vendor impersonations, supply chain attacks, Account Takeover (ATO), and other financial frauds that are hyper-targeted against your organization.
- Damage Control: It blocks credentials theft or malware downloads from phishing sites.
- Zero Trust Security: Suspect any user interaction vs. malicious behavior.
- Deliver Operational Efficiency: It accelerates business growth, improves the end-user experience, and ultimately delivers operational efficiency.
In this article, we have covered the meaning of phishing and phishing prevention solutions, along with their needs, benefits, work, market trends, expert advice, and some FAQs.
A list of the best phishing prevention solutions is provided with a detailed review of each and a comparison is made of top solutions. In the end, the conclusion and review process is discussed.
Market Share: According to the research by Grand View Research, the market share of cyber security is expected to grow with a CAGR of 8.9% within the forecast period of 2022-2030. It was valued at $184.93 billion in 2021.

Expert Advice: To select the best phishing protection solution that best fits your organization, you need to consider two things: its pricing plans and its features. Different solutions come with different pricing plans. Some common features you should check are: blocking of suspicious links, granular visibility, identification, prevention and remediation of attacks, etc.
List of Best Phishing Protection Solutions
Popular and Top-rated Phishing Protection Security Solutions:
- ManageEngine Endpoint DLP Plus (Recommended)
- Netcraft
- SlashNext (API based)
- Perception Point (API based)
- Talon (Browser based)
- Island (Browser based)
- Ironscales (Email based)
- Avanan (API based)
- Abnormal (Email based)
- Proofpoint (Email based)
- Mimecast (Email based)
- LayerX (Browser-based)
Comparing Top Anti-Phishing Solutions
| Software | Best for | Type of support | Pricing | Rating |
|---|---|---|---|---|
| ManageEngine Endpoint DLP Plus | Enforcing security policies on a granular level. | — | Contact for a quote, Free edition is available | 4.5/5 |
| Netcraft | Stopping phishing attacks at the source by detecting and neutralizing malicious URLs across the external attack surface before they impact the inbox. | Email-based | Contact for a quote. | 4.5/5 |
| SlashNext | Blocking phishing at scale and speed. | API-based | Starts with $0.13 per call per annum. | 4.7/5 |
| Perception Point | Holistic threat prevention with top attack vector coverage. | API-based | Starts with $7 per user per month. | 4.6/5 |
| Ironscales | Email anti phishing security | Email-based | $6 per user per month | 4.3/5 |
| Abnormal Security | Catching advanced email-based phishing attacks | Email-based | Starts with $3 per user per month | 4.6/5 |
Detailed reviews:
#1) ManageEngine Endpoint DLP Plus (Recommended)
Best for Enforcing security policies on a granular level.

ManageEngine Endpoint DLP Plus is a software designed to mitigate the risk of data leakage. So you can bet the software is great at protecting sensitive data against threats like phishing attacks. You can use the tool to easily configure and deploy security policies that control the access and transmission of data.
The software is also great at data discovery. The software can automate the process of content inspection to unearth the location of both structured and unstructured data. You can also make use of DLP Plus’s various templates to classify and categorize sensitive data.
Features:
- Cloud Upload Protection
- Data Classification
- Advanced-Data Discovery
- Instant alerts and report generation
Pros:
- Quick set-up
- Free edition available
- Centralized management
Cons:
- Better documentation needed
Verdict: ManageEngine Endpoint DLP Plus shines because of its ability to discover and classify both structured and unstructured sensitive data. It is quick and easy to set up. Plus, you’ll have no issue when defining rules-based protocols to control data access and transfer.
Price: A free and paid edition is available. Contact to request a quote for the paid professional plan.
#2) Netcraft
Best for stopping phishing attacks at the source by detecting and neutralizing malicious URLs across the external attack surface before they impact the inbox.
Netcraft is a leader in automated phishing protection and cybercrime disruption. Unlike traditional solutions that simply alert teams to threats, Netcraft provides an active digital risk protection platform designed to identify and remove malicious content in real-time.
By leveraging a global network of hosting and registrar partnerships, the platform automates the takedown process for phishing sites, fraudulent social media profiles, and deceptive mobile apps. This proactive approach focuses on breaking the attack lifecycle, ensuring that phishing campaigns are dismantled hours—if not days—faster than manual intervention.
Features:
- High-Speed Phishing Takedowns: Industry-leading automation for the immediate removal of phishing sites and malware distribution points across the global web.
- Global Phishing Feed: Provides high-confidence threat intelligence used by major browsers (Chrome, Firefox, Safari) and antivirus vendors to block phishing URLs at the network level.
- Deceptive Domain Monitoring: Continuous scanning for look-alike domains and “typosquatting” used to deceive employees and customers.
- AI-Enhanced Detection: Advanced analysis of emerging threats, including the detection of AI-generated phishing content and sophisticated invalid login URL schemes.
- Social Media & App Store Enforcement: Automated disruption of brand impersonation and credential harvesting across social platforms and mobile marketplaces.
Pros:
- Takedown Speed: The fastest takedowns in the industry, with a 1.9-hour median response time for phishing, significantly reducing the window of vulnerability.
- Preemptive Blocking: Direct integration with global browser filters means threats are often blocked for millions of users before the site is even taken down.
- Global Enforcement Network: Massive scale allows for the simultaneous disruption of thousands of phishing campaigns across multiple jurisdictions.
- Technical Precision: Deep-dive research into scammer tactics, such as identifying specific “AI indicators” like emoji-heavy fraudulent communications.
Cons:
- Data-Heavy Interface: The platform’s granular technical reporting is designed for SOC teams and may be overwhelming for generalist IT departments.
- Advanced Scope: Smaller organizations looking for a simple “email filter” may find the full infrastructure-level disruption suite more comprehensive than they require.
Price: Custom pricing based on the scale of monitoring and the volume of automated takedowns. Contact for a quote.
#3) SlashNext
Best for blocking phishing at scale and speed.

SlashNext is a phishing protection solution. It increases ROI with a 99.9% detection rate and 2x more blocking. It can be deployed in a few minutes with unified security analytics and real-time search.
It includes solutions related to email and endpoint security with brand protection, incident response, and Gmail phishing protection. It provides multi-channel protection with multi-channel risk assessments. It provides phishing defense APIs in real time.
Features:
- Secure email gateways are provided and avoid cyber threats.
- Prevent credential stealing, spear phishing trusted service compromise, etc.
- Protects brands and reputations with powerful AI machine learning APIs from phishing threats.
- High-volume threat intelligence lookup is available to block phishing threats
- RTP forensics APIs are provided to remediate sites or take down threat sources.
- Detects threats at scale in milliseconds through dynamic live screening.
Pros:
- Maximum visibility and control.
- Pre-built playbooks.
- Zero-hour AI detection.
Cons:
- Improvements in cleaning up the user interface are suggested.
Verdict: SlashNext has been trusted by various famous brands like Microsoft, StockX, Centrify, Splunk Phantom, and many more. It has been awarded the CISCO choice award 2022 in email security.
Pricing:
- Pricing plans are categorized as:
- Email: $45 per inbox per annum for 25-499 users.
- Browser: $25 per device per annum for 25-999 users.
- Mobile: $25 per device per annum for 25-999 users.
- API- Between $0-$0.13 per call per annum.
- Complete: $80 per user per annum for 25-999 users.
- A free trial and a demo are available.
Website: https://www.slashnext.com
#4) Talon
Best for reducing cyber risk and improving the end-user experience.

Talon is a browser security solution that secures devices regardless of their location, device, or OS. It helps in reducing cyber risks by preventing data loss or malware by providing deep visibility and control of internal activities.
It includes secure thirty-party access, secure employee BYOD, secure browsing, and zero trust features. It can be integrated with other applications and identity providers. The system also provides a comprehensive data loss prevention service.
Features:
- Integrates with other identity providers.
- Prevents cyber risks by providing Data Loss Prevention services.
- Encrypts files to protect them on endpoints or to be transferred externally.
- Restricts screenshots and provides clipboard and printing services.
- Ensures safe browsing by blocking phishing websites with URL filtering.
- Authenticates user access through the Zero Trust feature.
Pros:
- Chromium-based browser.
- ZTNA is available.
- Accelerate business growth.
Cons:
- Slow policy creation.
Verdict: Gartner has awarded it Cool Vendor 2022, recognized in Cyber Security Breakthrough Awards, winner of RSAC Innovation Sandbox 2022, and more. It is good for blocking phishing sites and enhancing email security.
Pricing: Contact for pricing.
Website: https://talon-sec.com/
#5) Island
Best for productivity, visibility, and governance.

Island is an enterprise browser security solution that provides a secure browser with full visibility and control over it. It enables us to safely engage with third-party contractors. It allows BYOD with security to one data.
It enables you to customize the browser internally by the specific company workflows. It makes the organization smarter, simpler, and out of the way. The ZTNA model delivers a simple and efficient zero-trust experience.
Features:
- Prevent phishing websites and malicious activities.
- Integrates with anti-malware and isolation technology for data loss prevention.
- Protects against ransomware attacks by eliminating unnecessary regulatory disclosures.
- Provides visibility of browser activities in a single place.
- Controls everything on the browser like screen captures, extension permissions, network tagging, and so on.
- Enables customizing the browser as per the brand’s specific needs.
Pros:
- Customizable browser.
- Complete visibility of user activities.
- Controls user interaction.
Cons:
- Pricing is not disclosed.
Verdict: Island security is good at providing enterprise browsers with effective features like the visibility of user activities on the web, controlling user interaction, preventing phishing sites, etc.
Pricing: Contact for pricing.
Website: https://www.island.io/
#6) Perception Point
Best for holistic threat prevention with top attack vector coverage.

Perception Point is a lightning-fast API-based phishing security software with holistic threat prevention. It can prevent malicious files, URLs, and social-engineering-based techniques across all channels, whether it is email, web browsers, cloud storage, CRM, etc.
It allows new channels to be added in just one click and can be viewed from a single dashboard. It helps in eliminating false negatives and reducing false positives with a fully managed Incident Response service.
Features:
- Ensures all kinds of threat protection, like APT, phishing, ransomware, malware, etc.
- Provides threat protection across all channels, including email, web browsers, cloud storage, etc.
- Incident response service is provided.
- Provides complete email protection at no limit, cost, or commitment, along with phishing email analysis tools.
- Protects the organization from threats coming through emails or other related channels.
- Optimizes performance eliminates false negatives and reduces false positives.
- Ensures that you are one step ahead of the attackers.
Pros:
- Free email security.
- Holistic threat prevention.
- One intuitive dashboard.
Cons:
- Improvements in report logs are suggested.
Verdict: Perception Point is trusted by many popular brands including Linde, Cloudinary, Acronis, Florida IT Pros, Team Honda, and many more. It has been awarded the #1 Email Security Solution for SE Labs Recent Email Security Review.
Pricing:
- Contact for pricing.
- Email security- Starts at $7 per user per month.
Website: https://perception-point.io
#7) IronScales
Best for automatically detecting and remediating advanced threats like BEC, credential harvesting, account takeover, etc.

IronScales is an API-based, easy-to-use anti-phishing platform with fast deployment. It provides a smart dashboard that shows incidents that require quick action on a priority basis.
A human + machine approach effectively deals with almost all of the attacks. It includes solutions related to ransomware protection, credential theft protection, BEC protection, phishing simulation testing, and many more. It is best for SMBs and enterprise-level businesses.
Features:
- Modern and diverse phishing training and testing are provided to deal with emerging threats.
- Training includes real-world attacks like ransomware.
- Automated incident response enables bulk remediation of threats in seconds.
- Can be integrated with email platforms like Google Workspace, Microsoft Office 365, and more.
- Automatically inspect links and attachments using collaborative threat intelligence.
- Remove malicious URLs in real time.
Pros:
- Easy to use.
- Fast deployment.
- Smart dashboard.
Cons:
- Reporting features that need improvement.
Verdict: IRONSCALES was awarded the Globe Award for Cyber Security Global Excellence in 2022, the Global Infosec Awards for Cyber Defence Magazine in 2021, the best email security provider by Expert Insights in 2021, and Best Phishing Protection 2021 by Expert Insights.
Pricing:
- Pricing plans are:
- Starter: Free
- Email Protection: $6 per mailbox per month
- Complete protection: $8.33 per mailbox per month.
- A 14-day free trial and a demo are available.
Website: https://ironscales.com/
#8) Avanan
Best for cloud email and collaboration security.

Avanan is an API-based cloud email and collaboration security platform that uses AI-based technologies for protecting the user’s inbox. It has been ranked No.1 by G2 for Cloud Email Security Solutions and has been trusted by over 5000 customers.
It is the first among its competitors to use API, machine learning, and AI for cloud security. It provides solutions related to anti-phishing, malware & ransomware, account takeover protection, DLP & compliance, and so on.
Features:
- It includes an easy 5 minutes deployment.
- Complete visibility is provided to monitor the entire suite.
- It provides full suite protection with 99.2% chances of reduction in phishing attacks, ransomware, account takeovers, and more.
- Has a higher catch rate of 99.2%.
- It along with protecting email also protects cloud applications.
- Generates automatic alerts to give knowledge of potential attacks.
- One-on-one customer support is provided.
Pros:
- Inline protection.
- Easy installation.
- Good customer support.
Cons:
- Mobile application.
Verdict: Avanan has been trusted by more than 5000 customers. It has been ranked #1 in Email Security Solutions by Gartner Peer Insights and G2. It is good in anti-phishing and incident response-as-a-service.
Pricing:
- A free trial with a demo is available.
- Pricing plans are:
- SMB under 500- Between $3.60 – $8.50 per user per month
- Enterprise over 500 – Contact for pricing.
- Edu/Gov – Contact for pricing.
Website: https://www.avanan.com/
#9) Abnormal
Best for protecting against the full spectrum of attacks.

Abnormal is a cloud email security platform or anti-phishing app that helps in reducing false positives by leveraging API-based integrations and a data science approach to prevent cyber attacks. It helps to displace the user’s SEG, improving detection efficiency, simplifying email security architecture, and streamlining SOC operations.
It covers various cyber attacks, including credential phishing, malware, ransomware, invoice & payment fraud, business email & supply chain compromise, etc.
Features:
- Detects phishing attacks by passing emails to traditional threat intel and reputation checks.
- Stop scams that have already gone into secure email gateways.
- Authenticated sender information through measures like re-entering the password.
- Determines the email’s suspicious tone and urgency of action.
- Inspects links or URLs to determine whether it is malicious or genuine.
- Automatically remediate similar email-based attacks.
Pros:
- Reduce the number of false positives.
- Leverage API-based integrations.
- Granular email content inspection.
Cons:
- Limited search features.
- Dashboard improvements are suggested.
Verdict: Global enterprises including XEROX, Urban Outfitters, Groupon, Royal Caribbean, and so on have trusted Abnormal. It is good for stopping credential phishing attacks through features like detecting, preventing, and remediating.
Pricing: Starts with $3 per user per month. Contact for pricing.
Website: https://abnormalsecurity.com/
#10) Proofpoint
Best for fighting phishing, data loss, and more with AI-powered defence platforms.

Proofpoint is an API-based phishing protection solution. It helps in securing emails from phishing attacks. Identifying and preventing attacks from entering networks is what it does. It includes advanced threat protection, security awareness training, cloud security, compliance and archiving, and digital risk protection.
It provides solutions related to combating email and cloud threats, changing user behavior, combating data loss and insider risk, preventing loss from ransomware, and more.
Features:
- Prevents cyber attacks including malicious URLs, phishing attacks, advanced malware, and more.
- Provides visibility into the threat landscape.
- Can be integrated fully to get advanced threat intelligence and technology.
- Security awareness training is provided.
- Automated incident response features are available.
- Covers multiple vectors, including cloud, email, network, and socialize.
- Visibility to user risk is provided to identify which users are being targeted.
Pros:
- Fully integrated solution.
- Unmatched visibility.
- Automated incident response.
Cons:
- Admin console
Verdict: Proofpoint is recommended for its effective services including email security and protection, advanced threat protection, premium security services, and more. It has been recognized under 20 Cooled Cloud Security Companies by 2022 CRN Cloud 100.
Pricing:
- A 30-day free trial is available.
- Pricing plans are categorized as under:
- Business: €2.95 per user per month.
- Advanced: €4.95 per user per month.
- Professional: €6.95 per user per month.
Website: https://www.proofpoint.com/us/solutions/protect-against-phishing
#11) Mimecast
Best for advanced email and collaboration security.

Mimecast is a world-class AI-powered efficacy. It is the number one security companion for 365 and workplaces. It provides defence against sophisticated attacks. It can be integrated with your existing investments.
It includes services like insider risk detection, DMARC management, message encryption, email incident response, and many more. It provides solutions related to securing email, ransomware attacks, data governance, brand impersonation, and so on.
Features:
- A secure email gateway is provided with antivirus and anti-spam protection.
- Targeted threat protection is provided by checking URLs.
- Blocks access to suspicious or malicious URLs.
- Inspects the attached files thoroughly under the targeted threat protection features.
- Converts suspicious attachments into a safe format.
- An impersonation protection feature is available to protect emails against impersonating trusted senders.
Pros:
- Automated backup
- AI-powered efficacy
- Integrate with existing security.
Cons:
- Customer Support needs improvement.
Verdict: Mimecast is trusted by more than 40,000 customers. It inspects around 1.3 billion emails daily and has 16 data centers in 7 countries. It has been awarded a gold cybersecurity excellence award for email security in 2022.
Pricing:
- A free trial and a demo are available.
- Pricing plans are categorised as:
- Core- $340 per 49 users per month.
- Hero- $420 per 49 users per month.
- Mega- $630 per 49 users per month.
Website: https://www.mimecast.com/content/anti-phishing/
#12) LayerX
Best for providing holistic browser security with in-browser phishing protection.

LayerX is the browser security solution that prevents web-borne threats and browsing risks.
The platform monitors browser sessions at the application layer, gaining direct visibility into all browsing events at its post-decryption stage, enabling it to analyze and enforce protective actions in real time with no latency or impact on the user experience.
LayerX can seamlessly modify the rendered web page to go beyond crude block\allow access to deliver granular enforcement that neutralizes the malicious aspects of the web page rather than blocking access to it altogether.
This is of critical importance when attackers mount their attack on an essentially legitimate page, such as when traversing the DOM structure of a banking app page. LayerX provides the highest level of security without degrading the user’s browsing experience.
Features:
- Scans and blocks web pages after identifying malicious or phishing content on websites.
- Real-time in-browser analysis of every web page.
- Enhances email security by monitoring and using policies on user’s web interactions.
- Monitors users’ sessions through high-resolution visibility.
- Restricts interaction on untrusted devices (it can be an unmanaged device or a suspected one).
Pros:
- The best phishing protection solution against targeted phishing web pages.
- Granular visibility.
- Frictionless deployment.
- ZTNA is available.
Cons:
- No email coverage.
Further Reading => Best LLM Security Platforms to Look For
Verdict: LayerX is good at integrating with other browsers and security platforms, BYOD-related security, and employee privacy with minimal user impact. It is recommended for granular browsing event visibility, high-precision risk detection, and secure browser access.
Pricing: Contact for pricing
Frequently Asked Questions
1. What are the best solutions for phishing protection?
The top solutions are:
– LayerX
– Abnormal Security
– SlashNext
– Perception Point
– IronScales
2. What is the technology solution for phishing attacks?
There are many solutions and various ways to avoid phishing. Some of them are:
– Catching the phishing delivery – emails, texts, etc – based on sentiment, communication patterns, and attachments.
– Just-in-time protection against malicious links and payloads.
– Up-to-date web security to detect suspicious URLs.
– Monitor all messaging platforms besides email.
– Keep an eye on your account and change the passwords more often.
3. How to increase resiliency against phishing attacks?
The two methods:
– Using up-to-date endpoint protection software that has high performance against malware and malicious code.
– Use multi-factor authentication to log in to your accounts like fingerprint scan, pin code, security question, passcode, etc.
4. Which is the common red flags of phishing emails?
The common red flags for phishing emails are:
– Pressure to respond quickly.
– Requests for sensitive information.
– Winning from contests you never enrolled in.
– Unexpected emails.
– Links that don’t go to official websites.
– Suspicious attachments.
5. What if I clicked on a phishing link?
If you click on a phishing link, then you can get viruses, spyware, or ransomware on your device behind the scenes without the knowledge of an average user. The user may also face data loss and downtime.
Conclusion
Through the research, we concluded how essential the prevention of phishing threats is. It detects a suspicious tone with urgency, which is a common technique of phishing used by attackers.
There are various tools that provide phishing protection. Every tool is different in providing the same. Different solutions have different sets of features with different pricing plans. Some are good at providing granular visibility LayerX, Abnormal Security, and more.
Some are good in reducing the number of false positives like Perception Point, Abnormal security, etc.
In this way, they provide different sets of features and different pricing plans with the ultimate objective of safeguarding the users from cyber attacks like phishing and more. We recommend LayerX to be the best of all Phishing Protection Solutions.
Our Review Process:
Time Taken to Research this Article: We spent 37 hours researching and writing this article so you can get a useful summarised list of tools with a comparison of each for your quick review.
Total Tools Researched Online: 33
Top Tools Shortlisted for Review: 10










