This step-by-step guide explains the reasons why you should back up and Microsoft Office 365 Backup process with NAKIVO Backup & Replication:
Numerous businesses manage their data in the cloud. That’s why Office 365 security is a popular discussion topic today. Some businesses think that data in the cloud is safe enough and doesn’t require extra protection. Others consider that data in the cloud requires continuous protection.
So, do you really need to back up Office 365?
The answer is yes; you do!

Table of Contents:
Microsoft Office 365 Backup: Reasons
This article discusses the top reasons why you should back up your Microsoft 365 data and simple steps to back Microsoft 365 data with NAKIVO Backup & Replication.
Recommended Tool
#1) ManageEngine RecoveryManager Plus (Recommended)

RecoveryManager Plus is an integrated backup and recovery solution for your Exchange Online, on-premises Exchange, and Google Workspace mailboxes. It can help you Backup and restore all items in your mailboxes, including all attachments.
It also aids in exporting entire Exchange Online and on-premises Exchange mailboxes or just a part of it as a PST file and secure them with a password for an additional layer of security.
Features:
- Exchange Online backup
- Sharepoint Online backup
- Incremental backup
- Backup retention
- Scheduled backups
- Backup encryption
- OneDrive for Business backup
Free trial: Available
Price: Standard Edition starts at $595
#2) MSP360
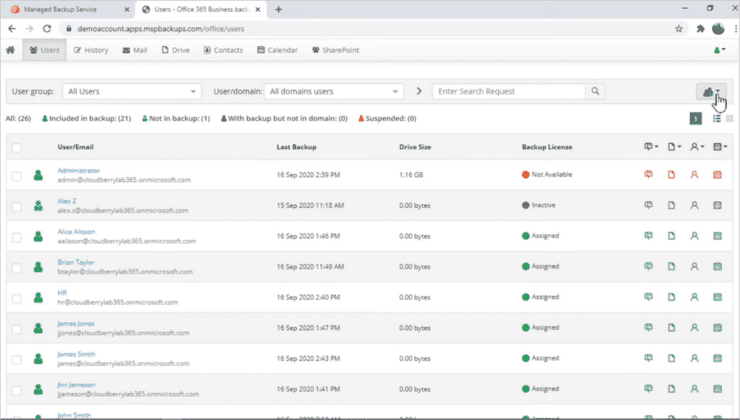
MSP360 offers cost-effective data protection and backup tools for all the core components of Microsoft Office 365, including Outlook, Calendar, OneDrive, SharePoint, Microsoft Teams and more. Plus, IT teams can get notification emails about backup, restore granular files with a few clicks, export files to PST, analyse backup reports, stay audit ready, and much more.
MSP360 has a flexible pricing structure. MSPs, businesses and individuals will find this platform quite useful for M365 backup. It is a complete, scalable, cost-effective cloud-to-cloud Microsoft 365 backup tool.
Features:
- Backup for Microsoft 365 and Google Workspace
- Backup history
- Reporting
- Multi factory authentication
- Role based access controls
- Audit Logs
- Email support
Free Trial: Available
Price: Starts at $3 per month.
Let us discuss the reasons below:
The Shared Responsibility concept implies that data protection obligations are divided between Microsoft and Microsoft 365 users.
Microsoft delivers the Microsoft 365 platform and services worldwide. Microsoft 365 users, on the other hand, handle the safety of their data. Microsoft 365 offers native data protection tools to its users; however, if a user deletes data permanently, it can be restored only with the help of backups.
#2) Limitations Of Native Data Protection
Microsoft 365 offers native data protection features. Those features are not a substitute for backups; however, they can drastically enhance your data security.
With Microsoft 365 native data protection, you can safeguard your Exchange Online mailboxes, Sharepoint Online sites, and OneDrive for Business from accidental deletions, cyber threats, and insider threats.
Let’s take a detailed look at Exchange Online, Sharepoint Online, and OneDrive for business data protection features.
a) Exchange Online
Litigation Hold: This allows you to place all items in the mailbox on hold. You can hold your items indefinitely or for a specific time. You can use litigation hold to preserve legal or other critical data that you may need for compliance purposes, court hearings, or reporting.
In-Place Hold: You can either place all items in the mailbox on hold or just specific ones. You can use In-Place eDiscovery in Exchange Server to search your mailboxes for individual items in cloud mailboxes or on-premises.
A web-based interface enables you to search quickly and doesn’t require high-tech skills. After you find the needed item, you can place this item on hold.
Inactive mailbox: You can create an inactive mailbox by placing a litigation or In-Place hold and deleting the associated user account. When you need to find and retrieve data from the inactive mailbox, you can easily do it with the search tool.
Data Loss Prevention (DLP): It enables you to keep track and manage your sensitive data. Every time you are about to send out credit card information, identification numbers, or private credentials, you receive a notification. By setting up the DLP settings, you can automatically block the transmission of sensitive data.
Exchange auditing reports: Enable you to monitor any change to your Exchange Online account either by Microsoft or your organization’s administrator. You can also check who has accessed the mailbox beside the mailbox owner.
Messaging Record Management (MRM): You can effectively manage high daily email volumes through MRM technology. With MRM, you can retain or delete emails within a certain period. You can also remove messages that have a low retention value and are seen as clutter.
Message encryption: Protects your message in transit, from sender to receiver and vice versa. You can also prevent your message from being forwarded. Message encryption allows you to protect your data from cybercriminals and unauthorized personnel.
Secure/Multipurpose Internet Mail Extensions (S/MIME) enable you to send signed and encrypted email messages inside your organization.
Journaling: You can use journaling to record your incoming and outgoing messages to meet legal compliance requirements and to monitor employee-client interactions. First, identify a person or group for journaling. Then record the external and internal messages of this person or group.
Mail transport rules: Enable you to surveille outgoing and incoming mail. You can also perform actions on the messages you inspect, such as block, bounce, hold, or forward the selected messages.
Monitoring: You can monitor the overall amount of spam and malware invasion attempts for the last 90 days. You can also generate reports about your monitoring activity, such as mailbox summary reports and mail protection reports.
Backing up Exchange Online: Microsoft does not provide a traditional backup, so you cannot restore your data to a previous point in time. However, you can use Exchange Online Archiving as storage.
b) SharePoint Online
Two-factor authentication: Enables you to protect your data by adding a second authentication factor. You can use a phone call, text message, or mobile application to complete the second step of the authentication process.
Control access from unmanaged devices: To prevent access to unmanaged devices such as airport and hotel kiosks, you can use Azure Active Directory device-based conditional access.
Inactive user sign-out: You will be signed out automatically if you stay idle for longer than indicated. You can also be signed out if you simultaneously use multiple tabs to enter the site.
Location-based access: Establish continuously secure access by defining a specific IP range. This IP range makes a connection available only for the users located in the area you trust. This area can be any size, from large to small. Users outside this range cannot enter the SharePoint site.
Safe sharing: You can allow external sharing or you can turn it off. If you have confidential data that you can’t share, store this data on a site that has external sharing turned off.
Data loss prevention policies
In transit protection: Encryption is used to transfer data safely between users and data centers. Microsoft uses only a secure access protocol, such as HTTPS.
At rest protection: Ensures protection of data on multiple levels, including:
- Physical: Only personnel with high-security clearance can access the data center equipment. In addition, video surveillance and security alerts ensure continuous data protection.
- Network: Microsoft uses Active Directory domains with separate domains for testing and production. The production domains have multiple divisions for extra security.
- Application: Vulnerabilities on the application level can compromise your SharePoint site’s security. Microsoft tackles app vulnerabilities by reinforcing researchers around the globe to detect vulnerabilities in the apps and report them through the Microsoft Online Services Bounty Program.
- Content: You can encrypt your data at the disk (BitLocker) or file level (Keys). Microsoft 365 has an anti-virus engine that scans uploaded files. The Office 365 Advanced Threat Protection (ATP) can help you analyze shared content and identify threats.
To protect your content even better, you can:
- Sync devices to the specified domains only.
- Use Intune to safely access your data from a mobile device.
- Create Information Rights Management (IRM) policies.
- Use Microsoft Secure Score to assess the security of your organization.
c) OneDrive For Business
OneDrive for Business and SharePoint Online share similar data protection features. In addition, you can use the following features to boost the security of your OneDrive for Business:
Strong password
Use a long and strong password. The password can be a combination of several words, numbers, and symbols. Simple passwords can be easily guessed by a password cracking tool. Don’t use the same passwords for different accounts.
As a Microsoft subscriber, you can get an alert about an occurring ransomware attack. In addition, you can restore your files to the point before they were affected, and you can restore your whole OneDrive to what it was before the attack. You can revive your OneDrive for business files within a 30-day timeframe.
History of versions
If your document editing went wrong or some data was accidentally deleted, you can recover it by referring to the earlier version of the document. You can restore the versions of various file types, such as PDFs, images, Microsoft 365 files, and video files.
Accidental deletion alerts
Don’t panic if you accidentally delete a large number of files in your OneDrive Cloud Backup. Microsoft can send you an alert, and you can recover your data promptly.
Expiration date for a sharing link
You can enhance the security of your data by assigning an expiration date to the sharing link. Doing so makes the data available to the user only for an indicated time. After this period expires, the data stops circulating on the net. Thus, there is a greater chance that your data won’t be misused.
Password-protected sharing
You can also put a password on your shared files. Doing so can decrease the chance of unauthorized access to your data.
OneDrive Personal Vault
Personal Vault is a protected area in your OneDrive that requires you to have an additional authentication method, such as fingerprint, facial recognition, or an SMS pin. Personal Vault can safeguard your data from unauthorized access and potential cyber threats. There are additional features that you can use to keep the data in your Personal Vault more secure.
These are:
- DirectScan: EIt enables you to take images, make scans, and shoot videos directly into your Personal Vault with the help of the OneDrive mobile app. By using DirectScan, you can access your files from any location or device.
- BitLocker: You can encrypt data located in your Personal Vault for extra security.
- Automatic locking: Your Personal Vault becomes locked after a short period of inactivity to ensure the security of your data. To access your files, you need to go through authentication steps.
Role-based Access Control (RBAC) In Microsoft 365
RBAC is a safety measure that prevents human error, unauthorized access, and cyber-attacks by permitting only the designated users to do particular tasks.
Microsoft 365 has various admin roles that you can assign to your employees. The admin roles include Exchange admin, SharePoint admin, billing admin, password admin, etc. In addition, ExchangeOnline Server has extra permissions based on the RBAC model that can be assigned either to administrators or end-users.
In SharePoint Online, you can also protect data by creating role-based access to the SharePoint objects. To grant access to a SharePoint item, you can add a user to a group that permits access by default. Alternatively, you can create a role assignment object.
The three main groups in SharePoint Online are owners (administrators), members (contributors), and visitors (readers).
Note: Using native Microsoft data protection tools can be the first step toward maintaining the security of your business. For example, use multi-step authentication to double-protect your business from a potential invasion. A recent ransomware attack on Brenntag was successful only because the company didn’t use multi-step authentication.
However, if your data becomes deleted due to the failure to use Microsoft data protection tools, backups are your only chance to revive the lost data.
#3) Accidental Deletions
Accidental deletions take place regularly and for various reasons. An employee may delete data because of a heavy workload or lack of knowledge about the importance of that data. The deleted items can remain in the recycle bin for up to 30 days before they go through a hard deletion.
But after they are gone, it’s impossible to bring them back with Microsoft native tools. The only option left is to recover those files from backups.
#4) Internal And External Threats
There are internal and external threats that can compromise your Microsoft 365 data. External threats include cyber threats such as ransomware or malware attacks. Often the reason for external threats is financial gain; however, there are other reasons. Your competitors may launch a cyber attack to pilfer your intellectual property or disrupt your workflow.
Current or former employees are often responsible for internal threats. A disgruntled employee can leak critical information, such as passwords or personal credentials, to hackers. Then cybercriminals can use this information to sabotage your system and steal or delete crucial data.
Alternatively, an insider who knows all the ins and outs of your IT infrastructure can find critical data and sell it to competitors.
Backups are the best way to recover your Exchange Online, SharePoint Online, and OneDrive for Business after a ransomware attack or insider threat. The attackers may know how to damage your data along with your backups. That’s why it is critical to keep an extra backup copy in a safe offsite location.
#5) Retention Policy Gaps
Businesses must retain data for legal and compliance purposes. However, if your business cannot manage data properly, policy gaps may emerge. Policy gaps arise due to operational disruptions such as failure to backup former employees’ data, inadequate Office 365 backup rules, and data loss during migrations.
- Failure to backup a former employee’s data: Microsoft automatically deletes inactive user accounts after a 90-day retention period. Often you find out later that the deleted account held critical data. In this case, backups are your best bet to restore the missing data.
- Inadequate Office 365 backup rules: To back up your data effectively, define clear-cut Recovery Time Objectives (RTOs) and Recovery Point Objectives (RPOs). An RTO is how much time your business needs to recover from a disaster. An RPO is how much data your business can afford to lose during a disaster.
- Data loss during migrations: Data loss often occurs during migrations from on-premise to cloud or from hybrid to cloud environments. During a data migration process, your company’s usual backup routine may become disturbed, resulting in retention policy gaps and data loss.
#6) Legal Compliance
Every business must meet legal compliance requirements relevant to its location to ensure continuous Microsoft Information Security. Organizations in the United States must follow the Sarbanes-Oxley Act. European companies must adhere to General Data Protection Regulation (GDPR).
Businesses are required to store financial data for reporting and possible court cases. Some businesses are also mandated to notify the appropriate authorities when they delete data. If you have deleted your legal compliance files and it’s too late to recover them, you can only restore your information from prior backups.
We have reviewed the 6 top reasons for backing up your Microsoft 365 data. Now, we can discuss how to backup your Microsoft 365 with NAKIVO Backup & Replication in simple steps.
Backing Up Microsoft 365 With NAKIVO
NAKIVO Backup & Replication is a backup solution that allows you to back up and restore data in Exchange Online, OneDrive for Business, and SharePoint Online, including mailboxes, contacts, calendars, emails, document libraries, individual files and folders, sites, and subsites.
Here’s how to use NAKIVO Backup & Replication to back up Microsoft 365 data:

Step 1: Add Microsoft 365 to Inventory.

Step 2: Create a SaaS Backup Repository.

Step 3: Create a Microsoft 365 backup job

Note: Click here to review the steps on how to create a Microsoft 365 backup job.
Conclusion
Microsoft 365 has comprehensive native data protection features. However, those features have certain limitations when it comes to sophisticated ransomware attacks and permanent data deletion. If you look for advanced data protection, Microsoft 365 backup is the best solution for protecting your business from data loss.
=> Visit here to learn more about how to back up your Microsoft 365 data.