Penetration Testing is very commonly used for web application security testing purposes. Let’s now cover this content in detail in this article.
Penetration testing aka Pen Test is the most commonly used security testing technique for web applications.
Web Application Penetration Testing is done by simulating unauthorized attacks internally or externally to gain access to sensitive data.
Web penetration helps the end-users find out the possibility for a hacker to access data from the internet, find out the security of their email servers and also get to know how secure the web hosting site and server are.
Table of Contents:
Penetration Testing

In this penetration testing tutorial I have tried to cover the following:
- The need for Pentest for web application testing,
- Standard methodology available for Pentest,
- Approach for web application Pentest,
- What are the types of testing we can perform,
- Steps to be taken to perform a penetration test,
- Tools that can be used for testing,
- Some of the penetration testing service providers and
- Some of the Certifications for Web Penetration testing
Recommended Vulnerability Scanning Tools:
#1) Astra
Best for effectively combining automated scanning and providing expert guidance
Astra’s Pentest Suite combines a powerful automated vulnerability scanner and manual pen testing capabilities to create a comprehensive security testing solution for web applications with features like CI/CD integration, continuous scanning, and zero false positives.

It has an intelligent vulnerability scanner and an extraordinary pen test capability to help you find vulnerabilities that may be missed by other pentests. You can also efficiently track your team’s progress with its amazing smart reporting function. Astra helps in establishing effective tech team coordination and collaboration.
Features:
- Intelligent vulnerability scanner
- Smart Reporting
- Manual Pentest
- Industry-recognized certification
- Excellent integration capability
Price:
- Scanner: $199/month
- Pentest: $4999/year (yearly billing only)
- Enterprise: $6999/year (yearly billing only)
#2) Invicti (formerly Netsparker)
Best for its proof-based scanning capability
Invicti is easy to use automated web application security testing platform that you can use to identify real & exploitable vulnerabilities in your websites.

Invicti provides excellent automation at every step of SDLC, saving a lot of precious time for your team members every month and making their job easier. You can get complete visibility of your app security which helps in finding vulnerabilities that may be missed by the other tools. It helps you gain effective control resulting in better team management.
Features:
- Easy and effective automation
- Provides security and scalability
- Total visibility
- Accuracy
Price:
- Free trial
- Invicti Pro
- Invicti Enterprise
#3) Intruder
Best for Continuous Vulnerability Management

With Intruder, you get a powerful web application and API vulnerability scanner/penetration testing tool. The software will automatically scan vulnerabilities in your web applications and seamlessly integrate them into your organization’s existing tech environment to catch vulnerabilities as and when they are found.
The continuous, automated penetration testing provided by Intruder gives you complete visibility into your entire IT infrastructure, including your internet-exposed systems, web applications, and internal systems. As such, you can use Intruder to perform reviews across your public and private servers, endpoint devices, and cloud systems.
Features:
- Perform Authenticated Checks
- Meet Compliance Requirements
- Increase Web Application Security
- Streamline Your Security Workflow
Price:
- Essential: $113/month
- Pro: $182/month
- Custom plans are also available
- 14-day free trial
Why Is Penetration Testing Required
When we talk about security, the most common word we hear is vulnerability.
When I initially started working as a security tester, I used to get confused very often with the word Vulnerability, and I am sure many of you, my readers, would fall in the same boat.
For the benefit of all my readers, let me first clarify the difference between vulnerability and pen-testing.
So, what is Vulnerability? Vulnerability is a terminology used to identify flaws in the system which can expose the system to security threats.
Vulnerability Scanning or Pen Testing
Vulnerability Scanning lets the user find out the known weaknesses in the application and defines methods to fix and improve the overall security of the application. It basically finds out if security patches are installed, whether the systems are properly configured to make attacks difficult.
Pen Tests mainly simulate real-time systems and help the user find out if the system can be accessed by unauthorized users, if yes then what damage can be caused and to which data etc.
Hence, Vulnerability Scanning is a detective control method that suggests ways to improve security programs and ensure known weaknesses do not resurface, whereas a pen test is a preventive control method that gives an overall view of the system’s existing security layer.
Though both methods have their importance, it will depend on what really is expected as part of the testing.
As testers, it is imperative to be clear on the purpose of the testing before we jump into testing. If you are clear on the objective, you can very well define if you need to do a vulnerability scan or pen-testing.
Importance and the need for Web App Pen Testing:
- Pentest Helps in identifying unknown vulnerabilities.
- Helps in checking the effectiveness of the overall security policies.
- Help in testing the components exposed publicly like firewalls, routers, and DNS.
- Let users find the most vulnerable route through which an attack can be made
- Helps in finding loopholes that can lead to the theft of sensitive data.
If you look at the current market demand, there has been a sharp increase in mobile usage, which is becoming a major potential for attacks. Accessing websites through mobile phones is prone to more frequent attacks and hence compromising data.
Penetration Testing thus becomes very important in ensuring we build a secure system that can be used by users without any worries of hacking or data loss.
Web Penetration Testing Methodology
The methodology is nothing but a set of security industry guidelines on how the testing should be conducted. There are some well-established and famous methodologies and standards that can be used for testing, but since each web application demands different types of tests to be performed, testers can create their own methodologies by referring to the standards available in the market.
Some of the Security Testing Methodologies and standards are –
- OWASP (Open Web Application Security Project)
- OSSTMM (Open Source Security Testing Methodology Manual)
- PTF (Penetration Testing Framework)
- ISSAF (Information Systems Security Assessment Framework)
- PCI DSS (Payment Card Industry Data Security Standard)
Test Scenarios:
Listed below are some of the test scenarios which can be tested as part of Web Application Penetration Testing (WAPT):
- Cross-Site Scripting
- SQL Injection
- Broken authentication and session management
- File Upload flaws
- Caching Servers Attacks
- Security Misconfigurations
- Cross-Site Request Forgery
- Password Cracking
Even though I have mentioned the list, testers should not blindly create their test methodology based on the above conventional standards.
Here’s an example to prove why I am saying so.
Consider you are asked to penetration test an eCommerce website, now give it a thought if all vulnerabilities of an eCommerce website can be identified using the conventional methods of OWASP like XSS, SQL injection, etc.
The answer is a no because eCommerce works on a very different platform and technology when compared to other Websites. In order to make your pen testing for an eCommerce website effective, testers should design a methodology involving flaws like Order Management, Coupon and Reward Management, Payment Gateway Integration, and Content Management System Integration.
So, before you decide on the methodology, be very sure about what types of websites are expected to be tested and which methods will help in finding the maximum vulnerabilities.
Types of Web Penetration Testing
Web applications can be penetration tested in 2 ways. Tests can be designed to simulate an inside or an outside attack.
#1) Internal Penetration Testing
As the name suggests, internal pen testing is done within the organization over LAN, hence it includes testing web applications hosted on the intranet.
This helps in finding out if there could be vulnerabilities that exist within the corporate firewall.
We always believe attacks can happen only externally and many a time internal Pentest is overlooked or not given much importance.
Basically, it includes Malicious Employee Attacks by disgruntled employees or contractors who would have resigned but are aware of internal security policies and passwords, Social Engineering Attacks, Simulation of Phishing Attacks, and Attacks using User Privileges or misuse of an unlocked terminal.
Testing is mainly done by accessing the environment without proper credentials and identifying if an
#2) External Penetration Testing
These are attacks done externally from outside the organization and include testing web applications hosted on the internet.
Testers behave like hackers who aren’t very aware of the internal system.
To simulate such attacks, testers are given the IP of the target system and do not provide any other information. They are required to search and scan public web pages and find our information about target hosts and then compromise the found hosts.
Basically, it includes testing servers, firewalls, and IDS.
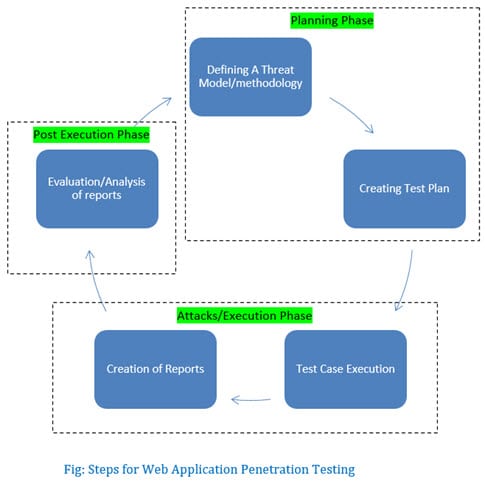
Web Pen Testing Approach
It can be conducted in 3 phases:

#1) Planning Phase (Before Testing)
Before testing starts, it is advisable to plan what types of testing will be performed, how the testing will be performed, determine if QA needs any additional access to tools, etc.
- Scope definition – This is the same as our functional testing where we define the scope of our testing before starting our test efforts.
- Availability of Documentation to Testers – Ensure Testers have all the required documents like documents detailing the web architecture, integration points, web services integration, etc. The tester should be aware of the HTTP/HTTPS protocol basics and know about the Web Application Architecture and traffic interception methods.
- Determining the Success Criteria – Unlike our functional test cases, where we can derive expected results from user requirements/functional requirements, pen-testing works on a different model. Success criteria and test case passing criteria need to be defined and approved.
- Reviewing the test results from the Previous Testing – If prior testing was ever done, it is good to review the test results to understand what vulnerabilities existed in the past and what remediation was taken to resolve. This always gives a better picture of the testers.
- Understanding the environment – Testers should gain knowledge about the environment before starting testing. This step should ensure to give them an understanding of firewalls and other security protocols which would be required to be disabled to perform the testing. Browsers to be tested should be converted into an attack platform, usually done by changing proxies.
#2) Attacks/Execution Phase (During Testing):
Web Penetration testing can be done from any location, given the fact that there shouldn’t be restrictions on ports and services by the internet provider.
- Ensure to run a test with different user roles – Testers should ensure to run tests with users having different roles since the system may behave differently with respect to users having different privileges.
- Awareness on how to handle Post-Exploitation – Testers must follow the Success Criteria defined as part of Phase 1 to report any exploitation. They should also follow the defined process of reporting vulnerabilities found during testing. This step mainly involves the tester finding out what needs to be done after they have found that the system has been compromised.
- The generation of Test Reports – Any Testing done without proper reporting doesn’t help the organization much, same is the case with penetration testing of web applications. To ensure test results are properly shared with all stakeholders, testers should create proper reports with details on vulnerabilities found, the methodology used for testing, severity, and the location of the problem found.
#3) Post Execution Phase (After Testing):
Once the testing is complete and the test reports are shared with all the concerned teams, the following list should be worked upon by all –
- Suggest remediation – Pen Testing shouldn’t just end by identifying vulnerabilities. The concerned team including a QA member should review the findings reported by Testers and then discuss the remediation.
- Retest Vulnerabilities – After the remediation is taken and implemented, testers should retest to ensure that the fixed vulnerabilities did not appear as part of their retesting.
- Cleanup – As part of the Pentest, testers make changes to the proxy settings, so clean-up should be done and all changes reverted back.
Top Penetration Testing tools
Since you have already read the full article, I believe you now have a much better idea of what and how we can penetration test a web application.
So tell me, can we manually perform Penetration testing or does it always happen by automating using a tool? No doubt, I think the majority of you are saying Automation. 🙂
That’s true because automation brings in speed, avoids manual human error, excellent coverage, and several other benefits, but as far as the Pen Test is concerned, it does require us to perform some manual testing.
Manual Testing helps in finding vulnerabilities related to Business Logic and reducing false positives.
Tools are prone to give a lot of false positives and hence manual intervention is required to determine if they are real vulnerabilities.
Also Read – How to Test Web Application Security Using Acunetix Web Vulnerability Scanner (WVS) tool
Tools are created to automate our testing efforts. Please find below a list of some of the tools that can be used for Pentest:
For more tools, you can also refer – 37 Powerful Pen Testing Tools For Every Penetration Tester
Top Penetration Testing Companies
Service Providers are companies providing services catering to the testing needs of the organizations. They usually excel and hold expertise in different areas of testing, and can perform testing in their hosted test environment.
Mentioned below are some of the leading companies that provide penetration testing services:
- PSC (Payments Security Compliance)
- Netragard
- Securestate
- CoalFire
- HIGHBIT Security
- Nettitude
- 360
- NetSPi
- ControlScan
- Skods Minotti
- 2|Sec
- Security Assessment
- Security Audit Systems
- Hacklabs
- CQR
Penetration Testing Certifications
If you are interested in getting certified in web app penetration certification, you can opt for the below certifications:
- OSWE (Offensive Security Web Expert)
- GWAPT (GIAC Web Application Penetration Tester)
- CWAPT (Certified Web App Penetration Tester)
- eWPT (elearnSecurity Web Application Penetration Tester)
Conclusion
In this tutorial, we have presented an overview of how penetration testing is performed for web applications.
With this information, the penetration tester can start vulnerability tests.
Ideally, penetration testing can help us create secure software. It is a costly method so the frequency can be kept as once a year.
To learn more about Penetration Testing, please read the related articles below:
- An approach for Security Testing of Web Applications
- Penetration Testing – Complete Guide with Sample Test Cases
- How to Test Application Security – Web and Desktop Application Security Testing Techniques
Please share your views or experience on the Pentest below. We would love to hear from you.








thanks for sharing. can you share one best tool for pen testing?
A PC with Linux installed.
Not sure who ever thought a PC a.k.a “windows” box could be used as a testing device, but it is for absolute certainty when I say, “don’t make that mistake”. A PC is not a testing device. It is a target device. Testers are Linux, *Nix, MacOs += VM / Docker.
Good explanation for beginners, I’m sure this information will help people who are wishing to get started in the web application penetration testing space
Good overview about PenTesting. I just have one question. I am from InfoSec, and would like to understand how I decide PenTest is required for a an existing Web Application which recently done a small change (like modified a business logic of existing code. This code is to provide static file download.
Hi Karthik, I think the best way to decide is to first get a penetration testing done for the complete application fix all the vulneabilities and perform a pentest as a part of the relesae cycle or perform it when there’s addition of a new module added to your application. You can also perform a pentest every quarter to get better understanding of your code and security posture of your application.
nice intro. please share examples also
Hello, I’m a novice with 0 basics and want to learn web penetration. Can a master teach me?
Good explanation. Please share some example with every phase of it.
Nice piece. It help us greatly. More indepth research is required in future.
great article , can you please provide us with examples
Thanks 🙂
I found this to be an excellent article. You mentioned Web Application Penetration Testing is done by simulating unauthorized attacks internally or externally to get access to sensitive data. In addition to internal and external testing, there is of course, double-blind testing, which can find issues that internal and external testing may not find.